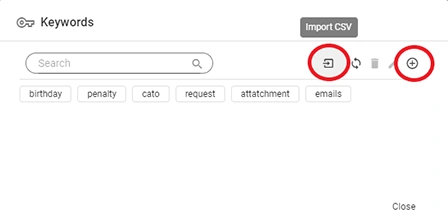
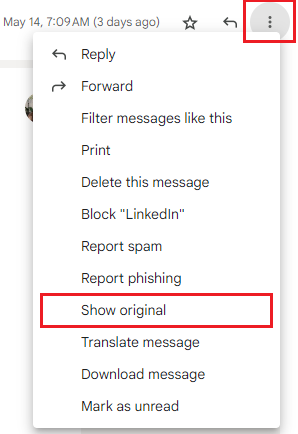
Gmail Email Header Analysis
Gmail Email Header Analysis
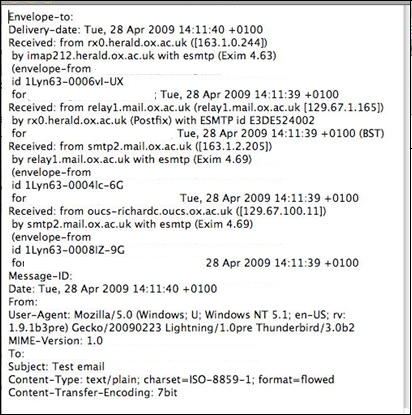
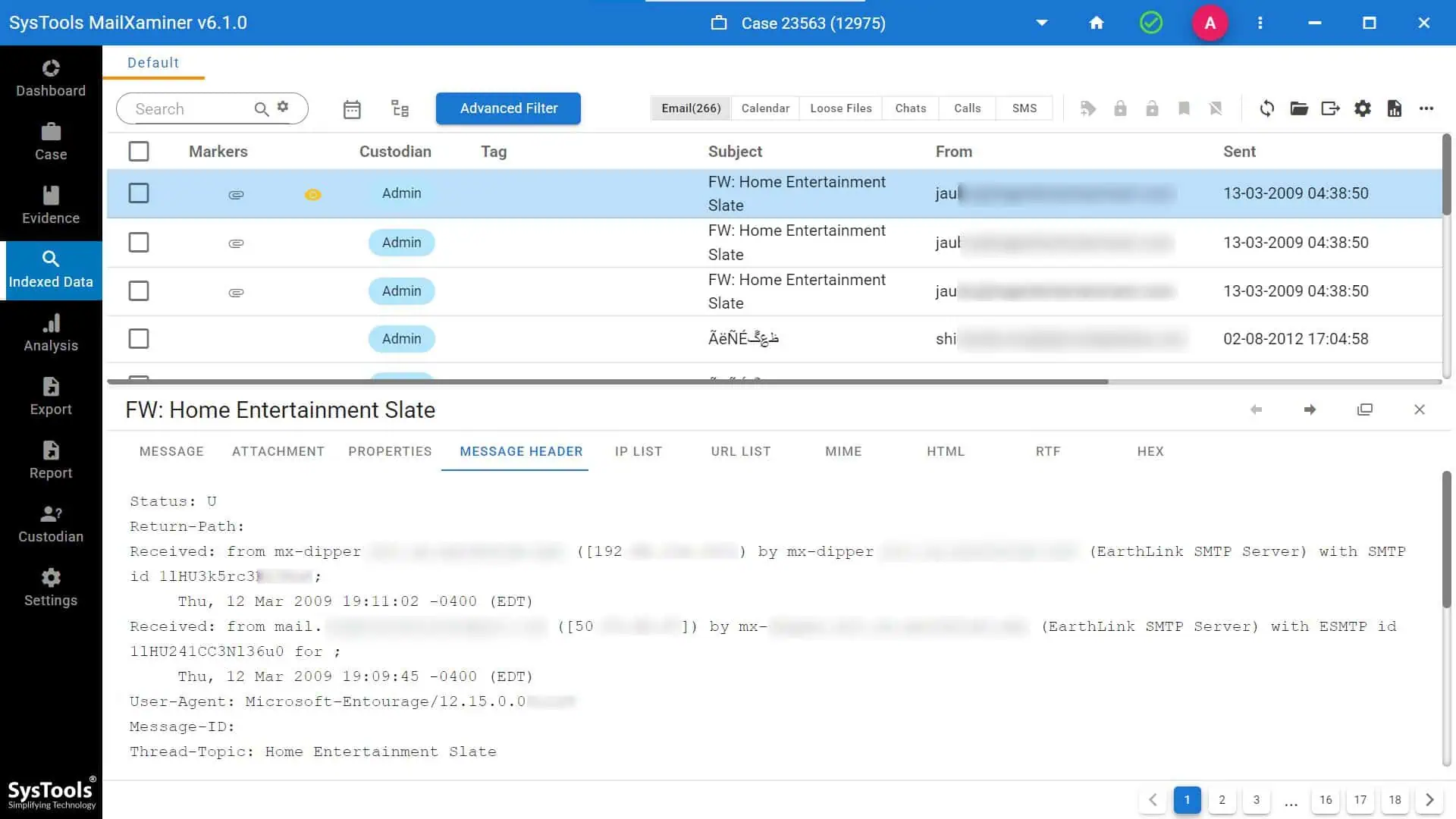
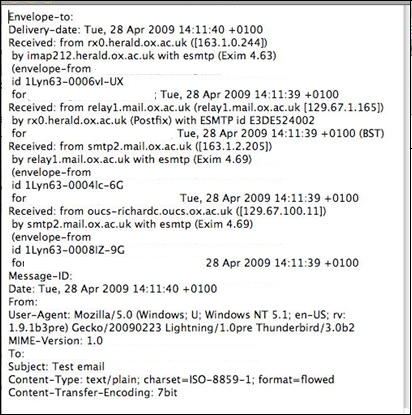
Open a particular email in Gmail. Then, click on three vertical dots and press ‘Show original’ to view all the information in the email header.
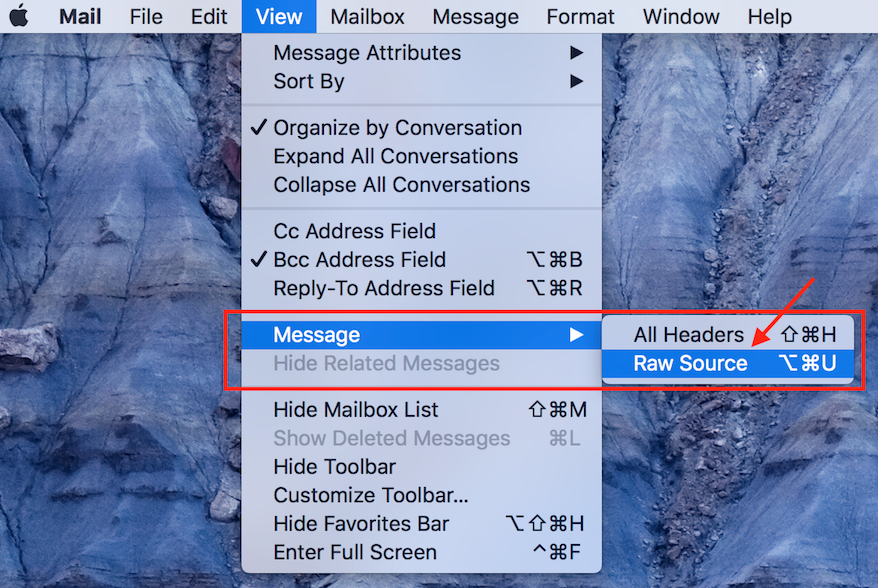
 View Apple Mail Header
View Apple Mail Header
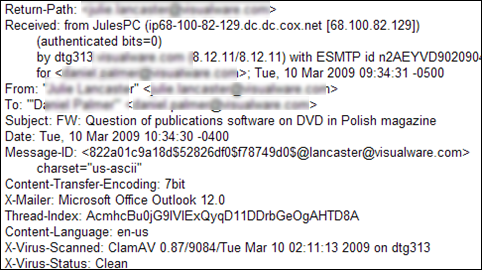
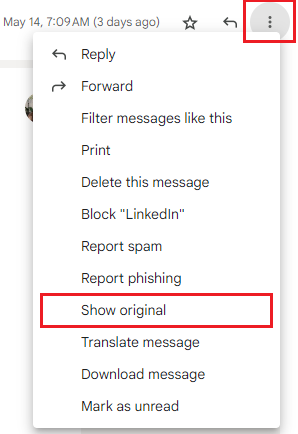
To start with Apple mail forensics and email header analysis, Click on a specific email on Apple Mail. Then, go to the View tab >> Message >> Raw Source to view the email header information.
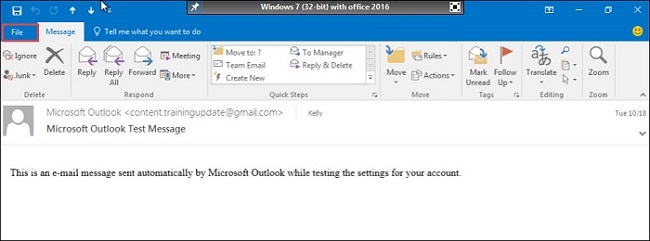
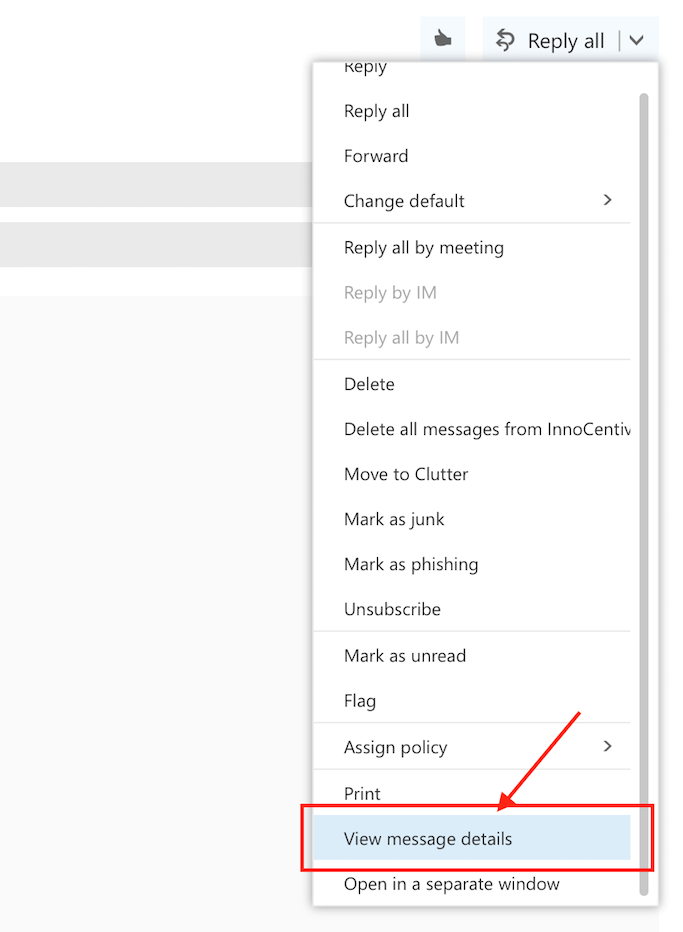
 View Outlook Web App Email Header
View Outlook Web App Email Header
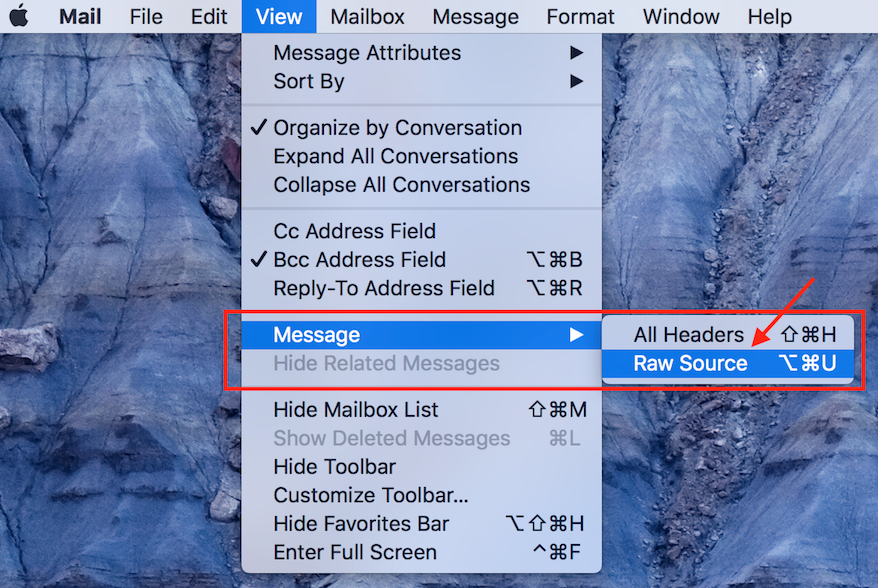
Open an email on Outlook. Then, press More and finally click on View message details.
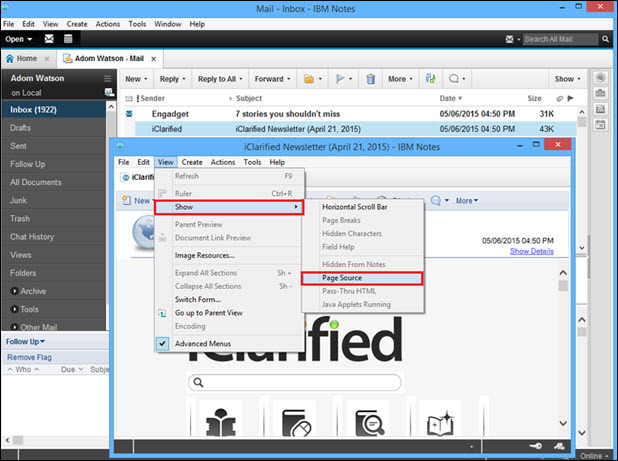
 View Lotus Notes Header
View Lotus Notes Header
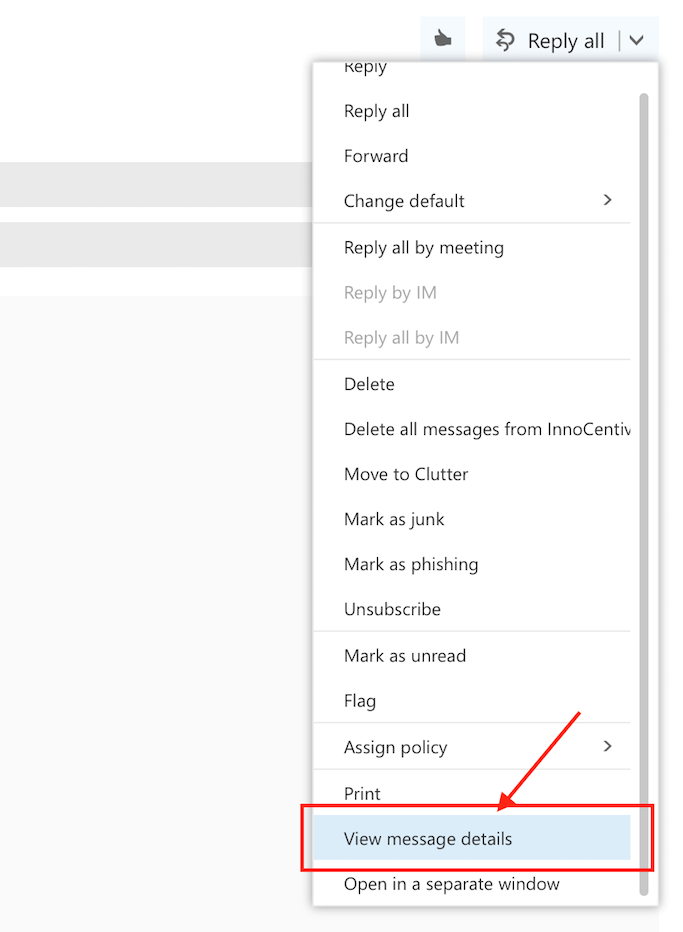
When a user send the message using Lotus Notes the server adds an unique field in the header data. A user cannot see this field through the normal email message view. The Lotus Notes NSF file forensics process help the investigators to identify email spamming, spoofing and the actual rout of the email message. To perform email header forensics of Lotus Notes data, please follow the below process:
- Open the email message of which you want to examine email headers.
- Now select the show option from the view tab.
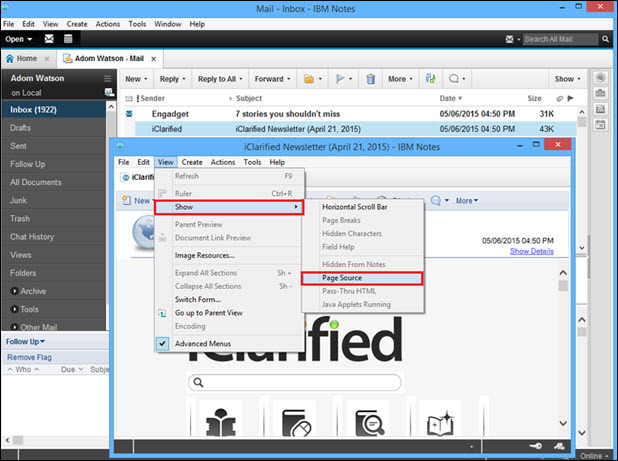
- After that through the Page Source option obtained through the Show menu user can easily view email headers of the selected message.
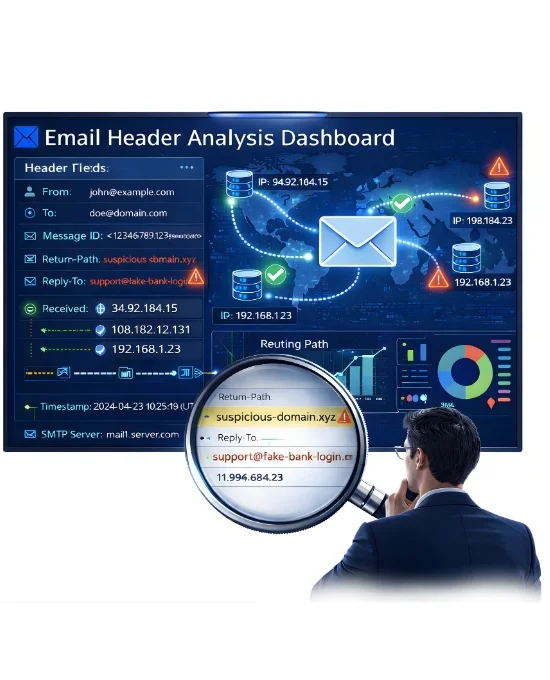
Understanding the purpose of each header field carefully will help the help the investigators to identify the evidence during the cyber crime investigation.
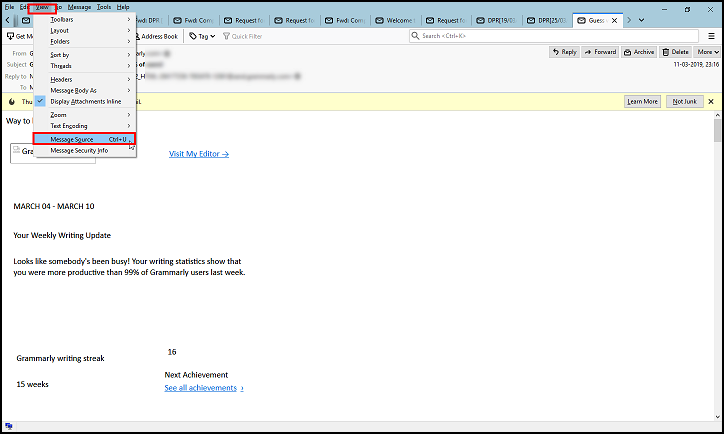
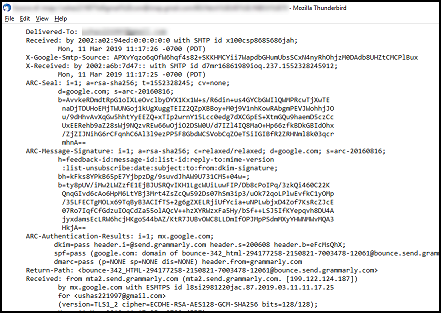
 Retrieve Thunderbird Mail Header
Retrieve Thunderbird Mail Header
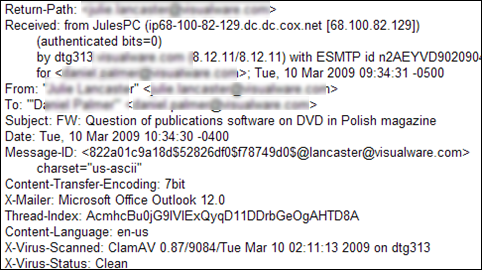
Since Thunderbird is one of the leading email applications used to share email messages between the users, the chance of email crimes through this platform is also very high. Any manipulation or discrepancy of the email content can be easily identified by the careful email header forensics while performing Thunderbird forensics. Before the analysis, understand how to get email header from the Thunderbird application.
- Open the email message for you want to check email header.
- Select the Message Source option from the View tab.
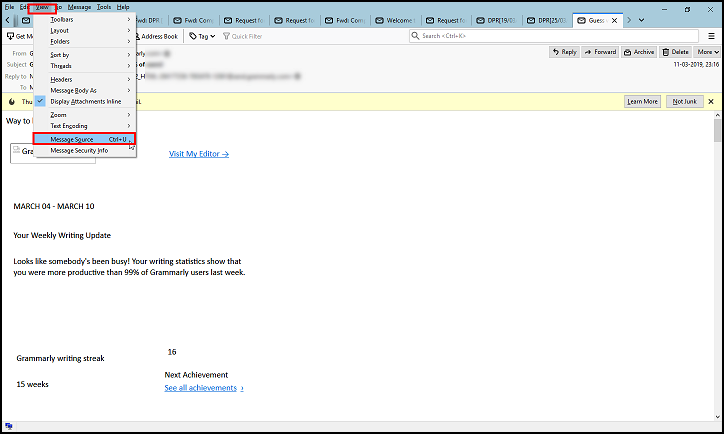
- Which will provide the email header information related to the specific email message.
 View Entourage Header
View Entourage Header
Entourage is an open source email client also known as personal information manager commonly used for communicate email messages between the email users. Follow the steps given below to perform Entourage Forensics and examine email headers for extracting the email related informations.
- First open the email message for view email header data associated with it.
- From the menu bar select the message option. Which provide you drop down menu with a number options.

- From the drop down menu click on the Internet Headers through which you will get full mail header information.
 Access Eudora Email Header
Access Eudora Email Header
Eudora is an open source desktop based email client. The careful study of Eudora email header field helps to access the complete information of the email messages such as sender receiver address, the server that handles the sharing etc. during Eudora email forensics.
- Double click on the email message for which you want to analyze email headers.
- It will shows the email message with partial header information.
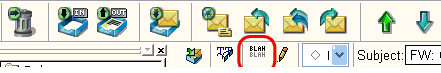
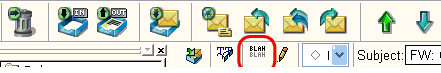
- Click on the BLAH BLAH BLAH icon to get full email header data of Eudora email.
 View IncrediMail Header
View IncrediMail Header
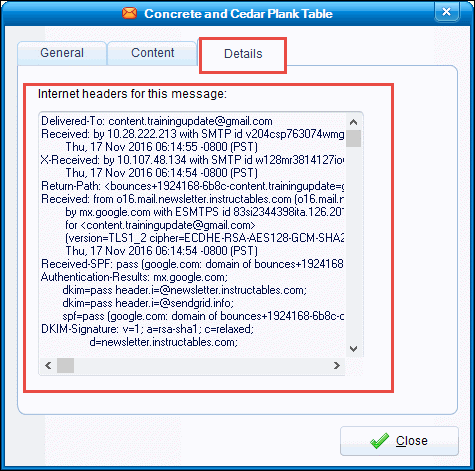
IncrediMail is an advanced email application which provides great feature experience while working with it. It also allows users to work in offline mode with great protection from spam and fraud emails. To get email header data during the forensic analysis of IncrediMail mailbox follow the below process.
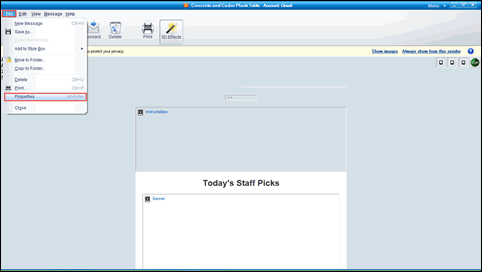
- Open the email message of which you need to examine the email header.
- Click on the file menu and select the properties option.
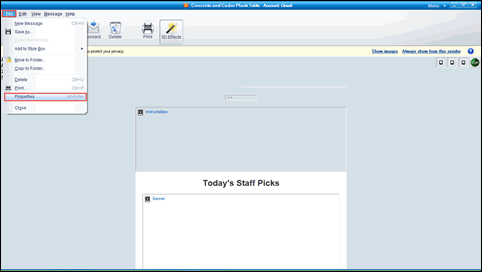
- To examine email headers of the IncrediMail, go to the Details tab from the properties window.
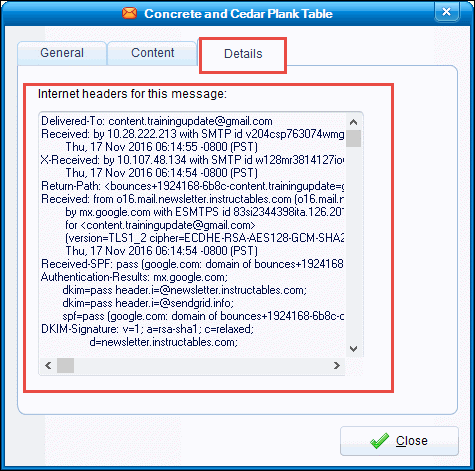
Using this method, a user can easily open and examine the IncrediMail header data manually.
 View Email Headers of The Bat!
View Email Headers of The Bat!
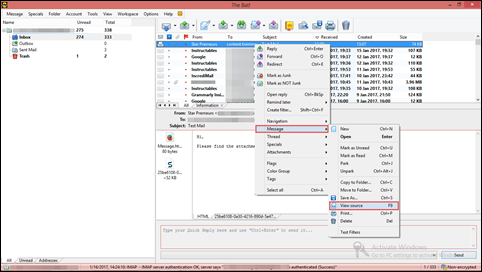
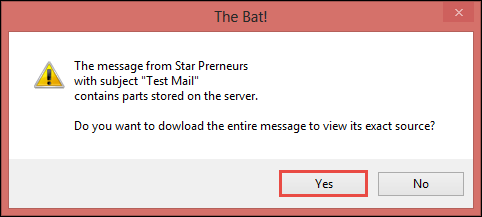
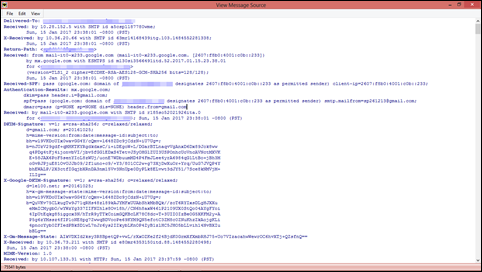
The Bat! is a desktop based email application known for its security, interface customization and filtering capability. Whenever an email communication is take place through The Bat!, the predefined server append unique field to header of the email. By the careful forensic analysis of The Bat! mailbox, you can get all the desired information through forensic email header analysis.
- Open the messages of which you want to read email header properties.
- Right click on the message and select the View Source option from the Message section.
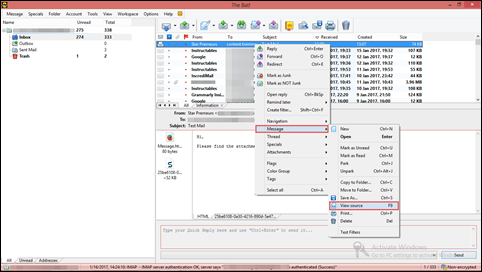
- A dialog box will appear to take the permission to download the entire message to view the its exact source.
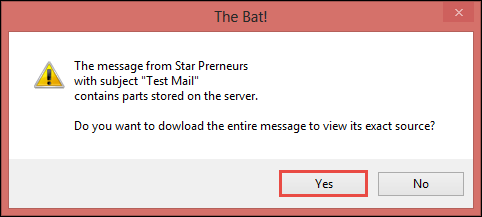
- After that a new window will open with the entire message source of selected message wich allows to view email headers of The Bat.
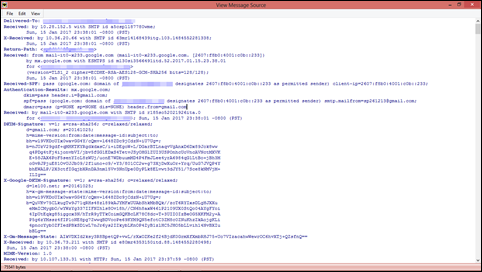
By following the above instructions you will be able to open and view the header information. However, sometimes it becomes difficult to analyze them. Let’s see why.