How Can Digital Forensics Be Used in Criminal Investigations
Mansi Joshi | April 14, 2026 | Forensics | 6 Minutes Reading
Blog Overview – Think you are in the middle of a criminal investigation. Evidence that needs to be extracted is Read More…
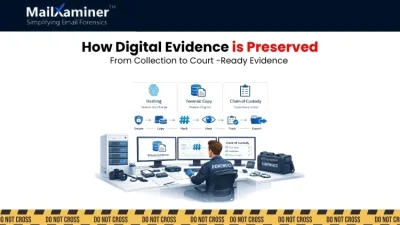
How is Digital Evidence Preserved Without Loss of It’s Legal Value
Mansi Joshi | April 10, 2026 | Forensics | 7 Minutes Reading
Blog Overview – As an investigator, you open a case. In a giant dataset, you found an email as evidence Read More…
Big Data Investigative Analytics: Simplified Guide
Mansi Joshi | April 7, 2026 | Forensics | 6 Minutes Reading
Blog Overview – Investigators today are consumed with massive digital data in the form of emails, chats, and files. In Read More…
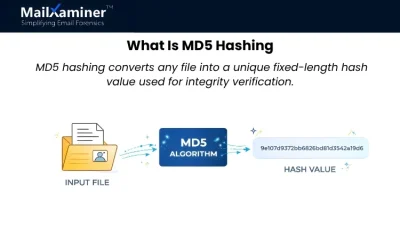
What Is MD5 Hashing? Guide to Data Integrity Verification
Mansi Joshi | April 4, 2026 | Forensics | 7 Minutes Reading
Blog Overview – In your investigation, you found an email that can prove a fraud case. Everything looks completely normal. Read More…
Why Are Mobile Devices Critical to a Digital Forensics Investigation
Mansi Joshi | March 31, 2026 | Forensics | 6 Minutes Reading
Blog Overview – A critical investigation is underway. Laptop data shows nothing suspicious. But the smartphone? It holds messages, locations, Read More…
Role of Digital Forensics in Commercial Litigation: Turning Digital Evidence into Courtroom Wins
Mansi Joshi | March 27, 2026 | Forensics | 7 Minutes Reading
In a courtroom, a high-stakes business lawsuit is about to be decided. Everyone in the courtroom senses that truth exists. Read More…
What is Email Bombing in Cyber Crime Guide for Investigators
Mansi Joshi | March 20, 2026 | Forensics | 6 Minutes Reading
Picture this – You are working in your company on a normal day, and suddenly your email inbox explodes with Read More…
How to Write a Digital Forensic Report (Step-by-Step Guide)
Mansi Joshi | March 17, 2026 | Forensics | 7 Minutes Reading
After conducting a proper forensics process, you found the evidence. Emails, logs, and hidden traces are all there. But now Read More…
How to Maintain Chain of Custody for Digital Forensic Evidence
Mansi Joshi | March 14, 2026 | Forensics | 7 Minutes Reading
When an investigator finds out the critical digital evidence, the real challenge begins for him/her. Courts and legal teams often Read More…
Corporate Espionage Investigations: How Investigators Uncover Hidden Data
Mansi Joshi | March 11, 2026 | Forensics | 6 Minutes Reading
An investigation that happens when a company spots that its confidential data has reached its competitor. When a company conducts Read More…