Forensic Analysis of Email in Cybersecurity: Find Hidden Evidence Accurately
Blog Overview – You know the evidence you are searching for your investigation is wrapped inside an email. But finding it efficiently and quickly feels slow and extremely disorganized. When combined with large inboxes, hidden details, and with approaching deadlines, things get even more difficult. In this blog, we will boil down forensic analysis of email in cybersecurity into clear steps. By the end, you will understand how professionals uncover hidden evidence.
Why Email Forensics Is Hard
Forensic analysis of email in cybersecurity is challenging, as emails contain lots of hidden data:
- Metadata
- Routing paths
- Attachments
Which do not remain completely visible inside a normal inbox. Large volumetric data and manual review increase the risk of missing important elements. If you have ever spent days searching emails and still felt unsure, you are not alone. Many investigation teams and departments reach upto a point where manual methods of investigation don’t work efficiently.
Process of Forensic Analysis of Email in Cybersecurity
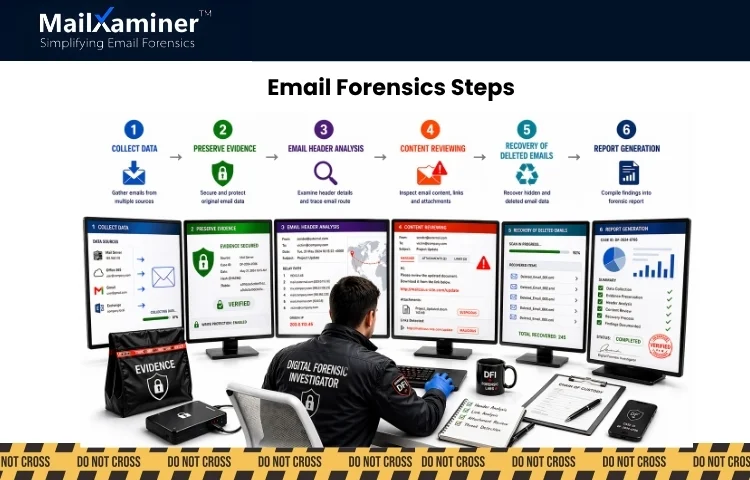
The process of email forensics is collecting, preserving, examining, and reporting of email data for identification of evidence. Here is how it works in structural steps or chronological order.
- Collect Data – The first step is to collect emails from all the available and relevant sources. While ensuring no data is lost during extraction phase.
- Preserve Evidence – Preserving of original email files in a secure state to prevent any modification and tampering.
- Email Header Analysis – In this step, investigators examine technical header details for verifying sender’s identity and tracing the email route.
- Content Reviewing – Inspection of email body, links, and attachments to detect any suspicious and malicious activity.
- Recovery of deleted emails – Retrieving hidden and previously deleted messages that could have contained critical evidence.
- Report Generation – Document findings into a clear and structured report to be presented for legal use.
Each level plays an important role that no evidence is missed, and findings remain reliable. If this process is performed manually. It becomes increasingly complex, especially when dealing with large volumetric email data. In many cases, maintenance of accuracy and speed at the same time becomes a major challenge. This is the reason investigation teams demand a structured approach for forensic analysis of email.
Related Read – Link analysis in criminal investigation
Manual Methods
Most investigators start their email forensic investigation using basic manual methods:
- Export emails from email clients like Gmail or Outlook.
- Search through keywords.
- Opening and reviewing emails one at a time.
This approach works well for small cases. But as case sensitivity and data size increase, this manual approach can become overwhelming. For more clarity, this can be seen as reading every page of the book just to find one important sentence. One may find it, but it takes a lot of time and patience.
Related Read – Current challenges in digital forensics investigations
Risks Associated with Manual Methods
Forensic analysis of email in cybersecurity, if done manually, can be slow, error-prone, and often fails to detect hidden and deleted data. There are some risks associated with manual approach, which are:
- Important evidence can be missed.
- Time taken in investigation increases.
- No clear structure is present for analysis.
- Reports become extremely hard to prepare.
In many corporate espionage investigations. Evidence must be clear, accurate and well documented. Manual methods fall short of these expectations. This is the reason a structured approach is preferred.
Manual vs Structured Approach
| Method | Time Taken | Risk Level | Accuracy |
|---|---|---|---|
| Manual method | High | High | Low |
| Structured approach | Low | Low | High |
Smarter Approach
Smarter approach to forensic analysis of email in cybersecurity is to use highly organized and structured tools where you load your evidence and then organize, search, and analyze large email datasets efficiently. Instead of hopping between emails, everything remains centered in one place.
Investigator can filter, search, and review the data quickly. It can be thought of as using a search tool rather than scanning every document manually. This approach reduces manual effort, saves time, and improves accuracy. Tools like MailXaminer help simplify this process, which allows investigators to examine and organize email data in a highly organized way.
Instead of working on multiple tools, you can review all email data in one environment. This helps invite clarity to scattered data and makes analysis efficient. As it supports deeper visibility into emails, helping investigators identify information that may not appear in normal inbox view.
If you want to understand how this works in a real-world scenario, you can request for demo and see the workflow in action
Common Mistakes Investigators Make
We have observed many investigators fail due to unprofessional mistakes:
- Ignoring email headers.
- Not preserving the original data.
- Missing deleted emails.
- Relying only on visible content.
Not committing these mistakes can significantly improve forensic analysis of email in cybersecurity.
Quick Check
Before going ahead, take a moment and ask:
- Are you handling large volumetric emails – sometimes thousands in a single case ?
- Do your investigations stretch from hours into days?
- You are still unsure whether you have uncovered critical details or not.
If your answer was yes to any of the above questions, there is a gap in your current process that needs to be filled-up with an email forensics software. As in large investigations, missing just one email thread can shuffle the entire direction of the case.
Where It’s Used
Email forensic analysis plays a critical role across different sectors:
- Corporate investigations (fraud and internal misuse)
- Legal disputes and eDiscovery.
- Government and law enforcement operations.
Why this matters:
- According to research, 90% of cyber incidents involve email in some form.
- In business environments, professionals deal with 10,000+ emails per case.
- Even a single overlooked message can delay a decision and weaken evidence.
In situations like these, accuracy is must and clarity in findings impacts how legal action will be taken. We hope from the above information that you have clarity on importance of forensic analysis of email in cybersecurity.
Pro Tip: Missing even one email is not a small mistake. It can change the direction of an entire investigation.
Final Thoughts
Email evidence can shape the outcome of an entire investigation. When the process is unstructured, even an experienced investigator can miss important details. When email data is handled in an organized way. Patterns become clearer, timelines make more sense, and evidence becomes easier to validate.
A structured approach not only provides investigators speed but builds confidence in the findings. This is important when results need to in legal and corporate environments.
Frequently Asked Questions
Q – How forensic analysis of email is done in cybersecurity?
A – Forensic analysis of email in cybersecurity is executed via collecting email data, preserving it’s original state, and analysis of headers and content. It goes all the way to documenting the findings. This process helps investigators identify the sender, trace email paths, and uncover hidden and suspicious activity.
Q – Why is email forensic analysis important?
It becomes important when emails contain critical evidence in cyber incidents. It helps investigators in fraud identification, communication pattern tracking, and providing reliable proof for corporate investigations.
Q – What are the biggest challenges in email investigation?
A – The major challenge is handling large columns of email data, detecting hidden or deleted messages, and maintaining accuracy during the analysis. When you depend on manual methods, the chance of missing important evidence increases.

