Netscape Forensics Through Email Backup Analysis
Netscape Email Backup Analysis is important during the digital forensic investigation on Netscape Mail client. It’s simple and unique features make this email client a target for criminal activities. With the help of a highly efficient Email Forensics Tool, investigators can perform the Netscape forensics through the mailbox analysis. The tool also enables the transfer of data from Netscape to Outlook using the export option. In this blog, we are going to understand the process on how to perform Netscape email analysis with the help of an automated solution.
Netscape Mail is an email and news client developed by Netscape Communication Corporation. It is mainly using for messaging purposes. Initially, the Netscape mail program with the origin from Mozilla Thunderbird. The initial name was Netscape Mercury, later it became Netscape Mail client. In 1998, after the purchase of Netscape by AOL, the development of Netscape Mail & Newsgroup was hand over to Mozilla Foundation.
In 2008, AOL announced that they have ended the development and support of Netscape Navigator and Messenger. The desktop email client, Netscape allows configuring and managing multiple email account at a time. It is integrated with free Netscape Webmail & AOL email account which also supports IMAP, POP, SMTP protocols.
Extract Email Evidence During Netscape Forensics
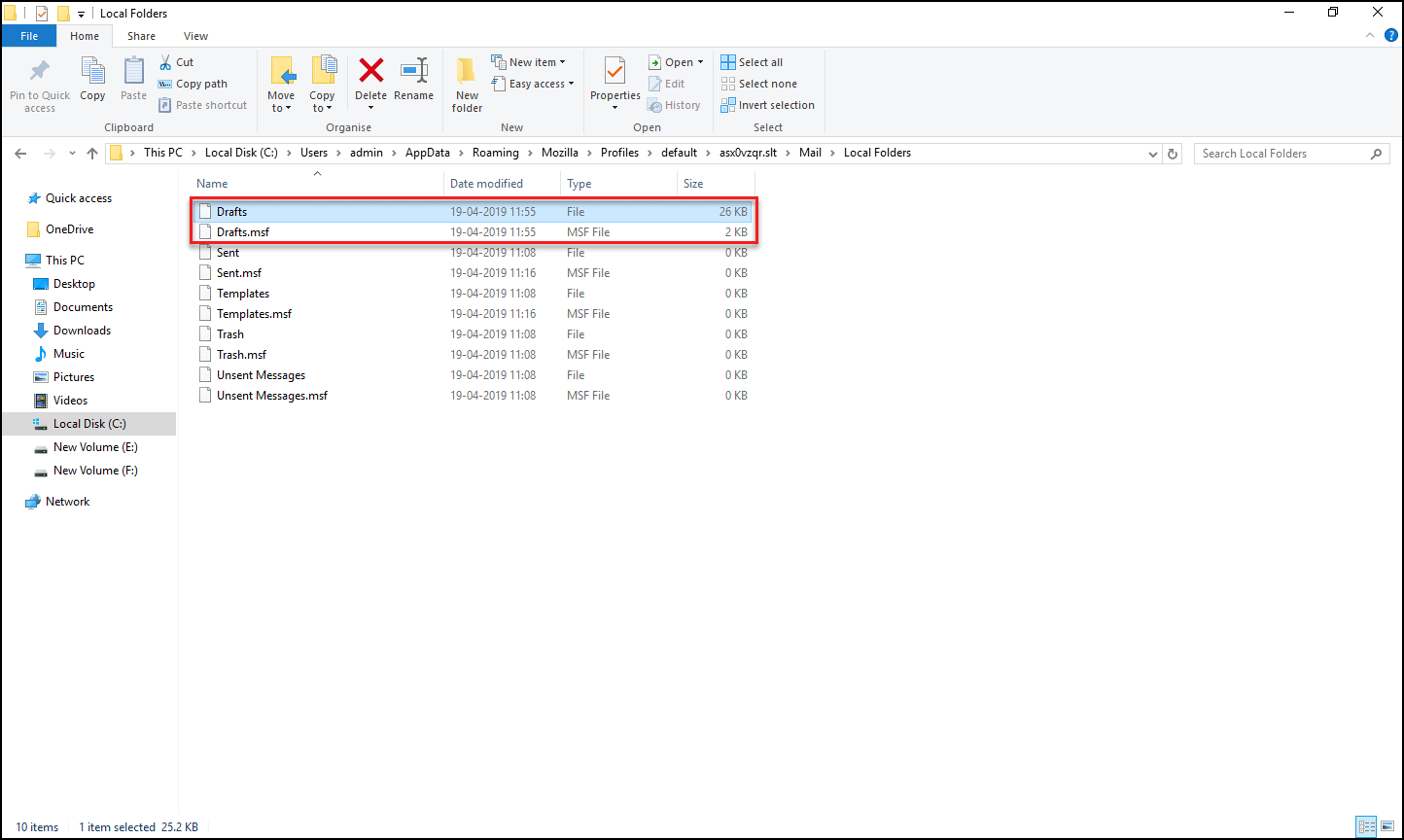
Email storage files are normally an important source of evidence. In the case of Netscape Mail, it uses MBOX file format to store its email data which can be considered as the primary source of evidence. Each folder creates a separate MBOX file to store the email data. The MBOX files generally appear without any extension, at the location. And, each folder is associated with a summary file with the extension .msf.
Default Location of Netscape Mail Folder
The default location of the Netscape email data varies according to the “User Settings” and “Operating System”. These are the common location in use to store email data. It will help you to extract email data and perform Netscape mailbox analysis.
Windows: C:\Users\admin\AppData\Roaming\Mozilla\Profiles\\
Mac: ~\Library\Mozilla
Linux: $HOME/.mozilla
Netscape Forensics Email Backup & Analysis with MailXaminer
During Netscape forensics, the email storage files are an important source of evidence. But unfortunately, the MBOX files can not be viewed without the corresponding email clients. It is the main challenge faced by most forensic investigators. Even after the email data is extracted from its location, investigators cannot analyze the data without the help of the respective email client. In such a situation, the Computer Forensic Tool is an appropriate solution for the investigation.
The automated solution provided by the software will help the investigators in Netscape email analysis. It also helps to import or export Netscape data to perform the analysis process more conveniently. Follow the below section to know how to perform Netscape email backup analysis with MailXaminer and extract the evidence through it.
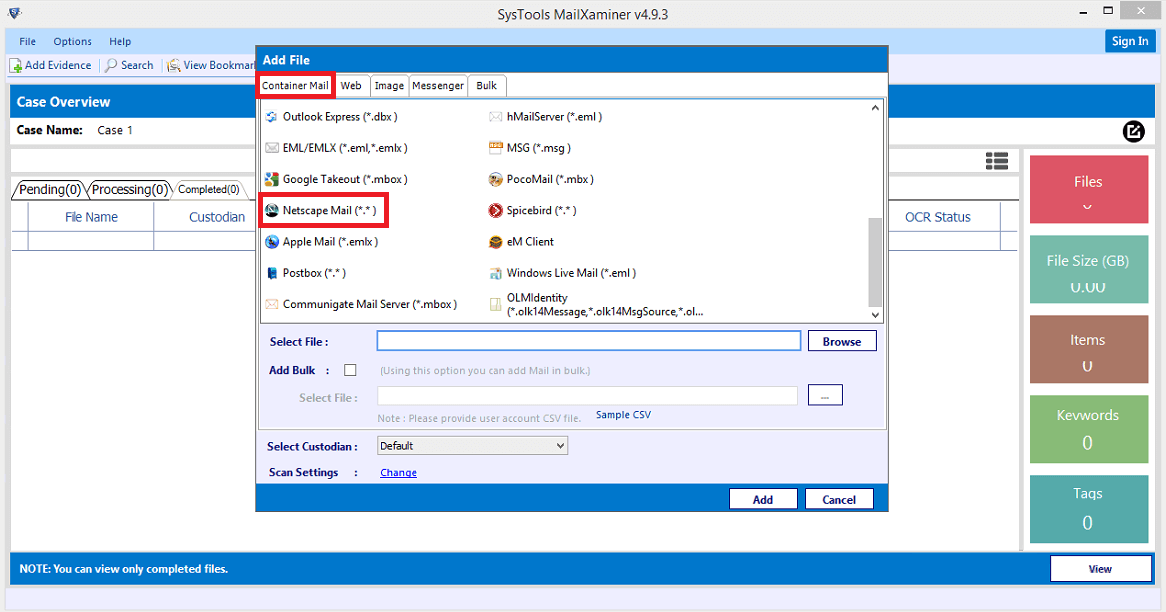
Add Mailbox File
Firstly, users just have to add suspected email data into the software to perform the Netscape mailbox analysis. Then, click on the “Add Evidence” button and select the Netscape Mail (*.*) option from the Container Mail section. The tool will also help the forensics examiners to back up the deleted email data.
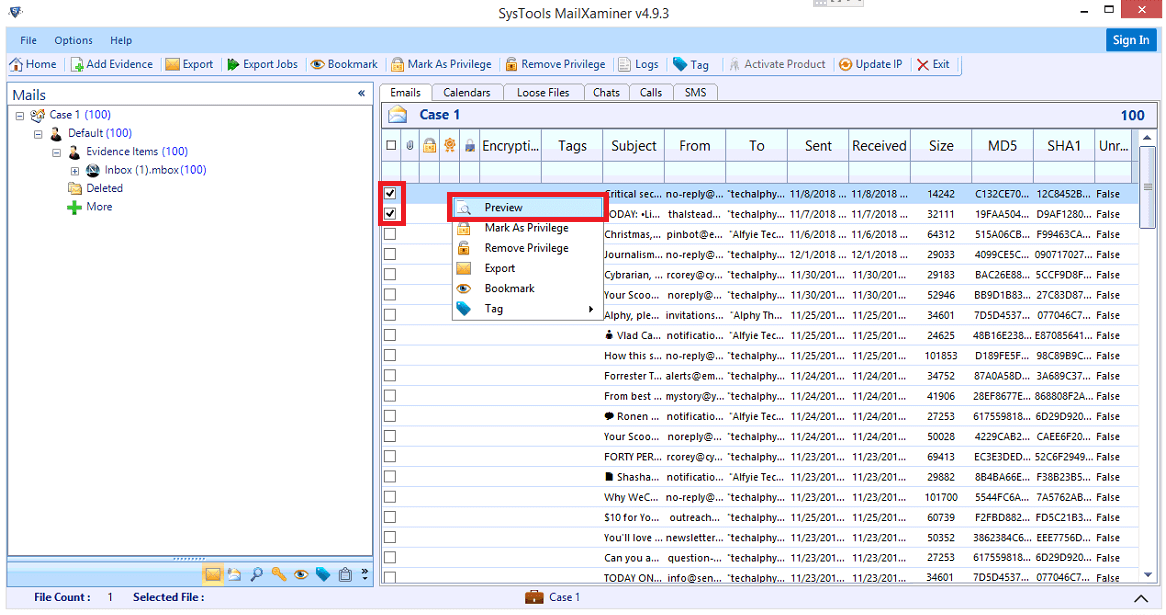
Preview Email Files
After the completion of the Netscape mail backup process, the forensic tool allows performing advanced Netscape email analysis through different views. Each view helps to extract important evidence. For this, select and right-click on the email, then choose the “Preview” option. The software will display the email in different previews such as Normal Mail, Hex, Properties, Message Header, MIME, Email Hop, HTML, RTF, Attachment, and Word Cloud.
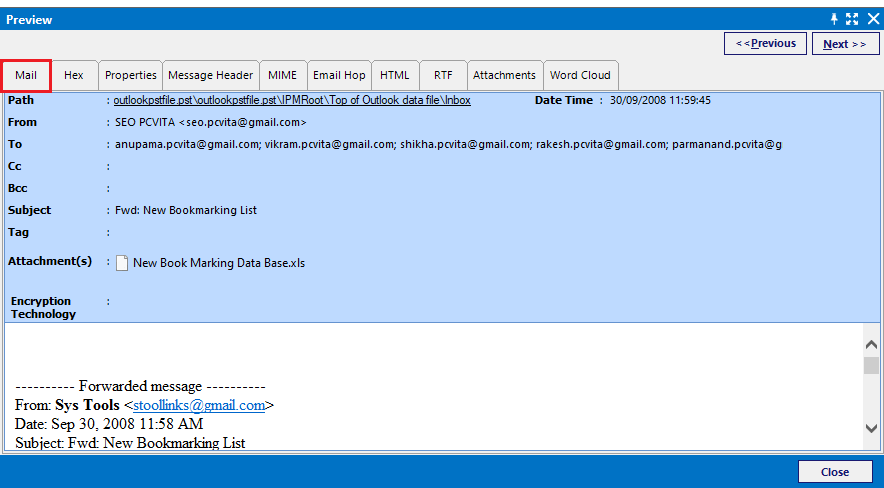
Normal Mail View
During the Netscape forensics, the “Mail” views of the email in forensic software help the investigator to easily analyze the email data from a user perspective.
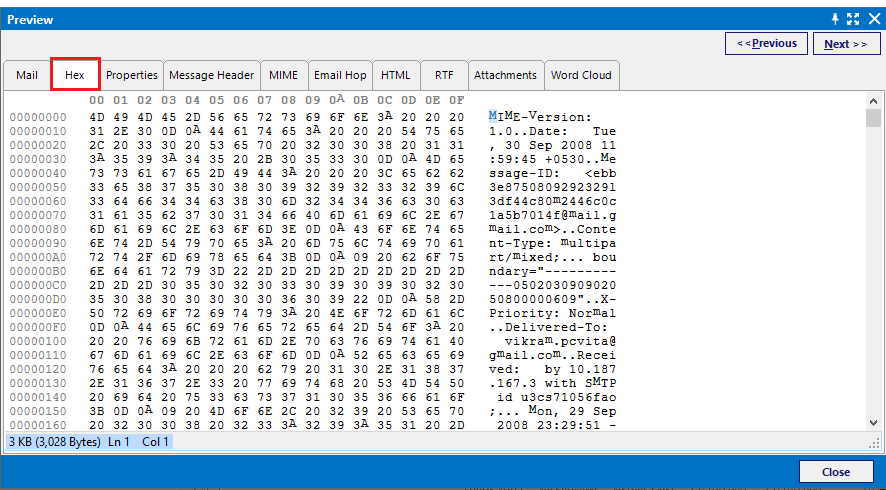
Hex View
The “Hex” view option of the tool allows users to do Netscape email backup analysis through its hexadecimal code. It provides the hexadecimal value corresponding to the data and it consists of Offset Value, Hex Code, and Text Value of email data.
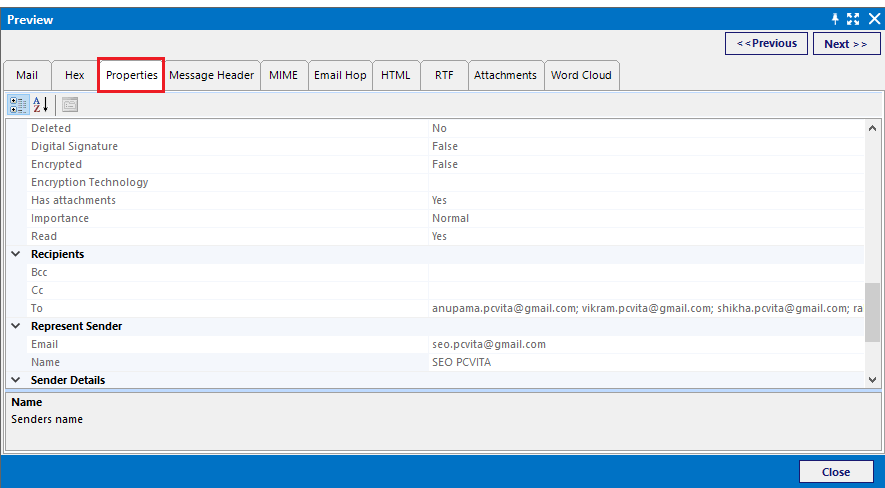
Properties View
During the Netscape forensics, the “Properties” view of the email provides metadata related to the email message. It helps the investigator to obtain the summary of email data easily. This view contains details such as Hash value, Body details, Date, Internal header details, Message flags, etc. It helps in the fast retrieval of data related to email without performing the deep Netscape email analysis.
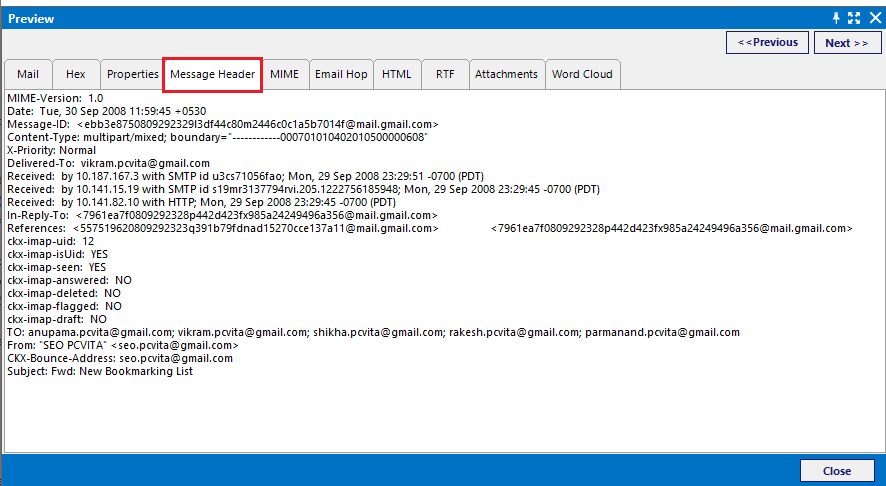
Message Header View
Through the “Message Header” view of email data, users can examine the email header details deeply while performing the Netscape email backup analysis. It includes basic details such as MIME version, Message-ID, Content type, Sender & Receiver address, etc. It is a complete set of data that can help an investigator to obtain user-related information and hidden evidence.
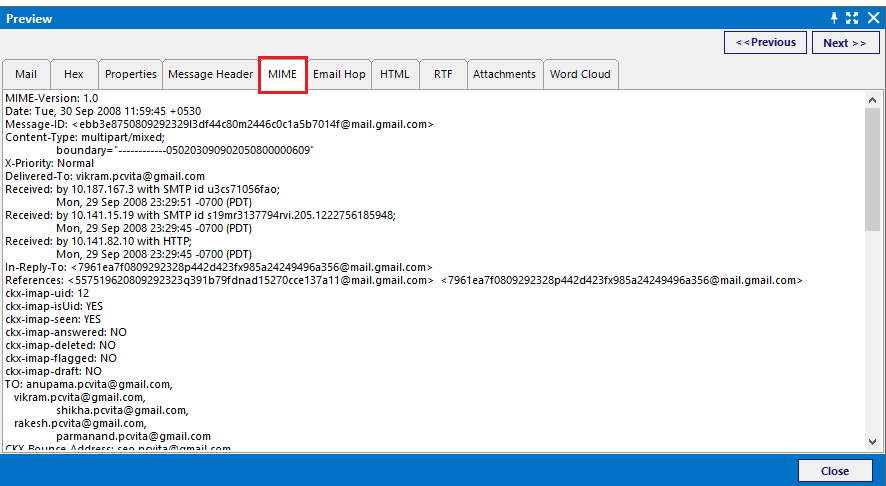
MIME-Version
The “MIME” view helps investigators to disclose important information related to email data like Priority Field, References, etc. It also gives the information supported for text or non-text attachments and its header information.
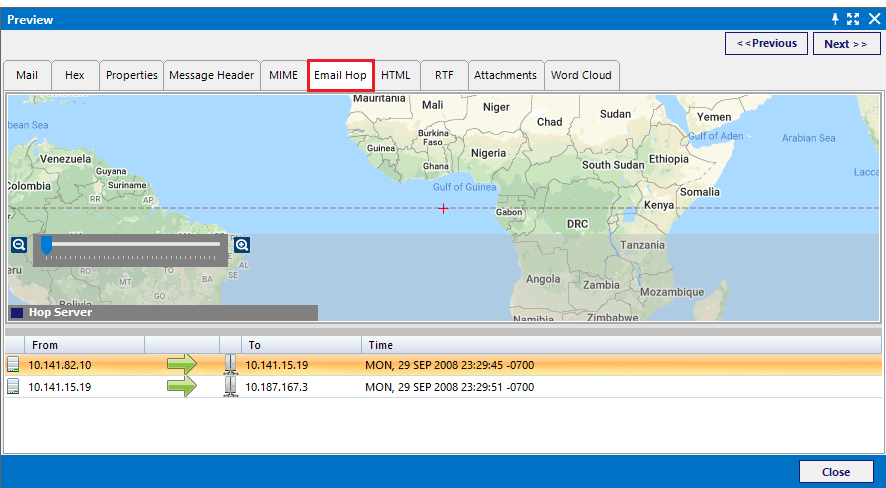
Email Hop
It is a special view provided by the tool which helps the examiner to trace the path through which the email message has been traveled. Through the other Netscape mailbox analysis views, users can get the sender-receiver-related information only. But they cannot find what is happening between the sender & receiver end. The email hop view graphically represents the routers, gateways & switches through which the email has traveled.
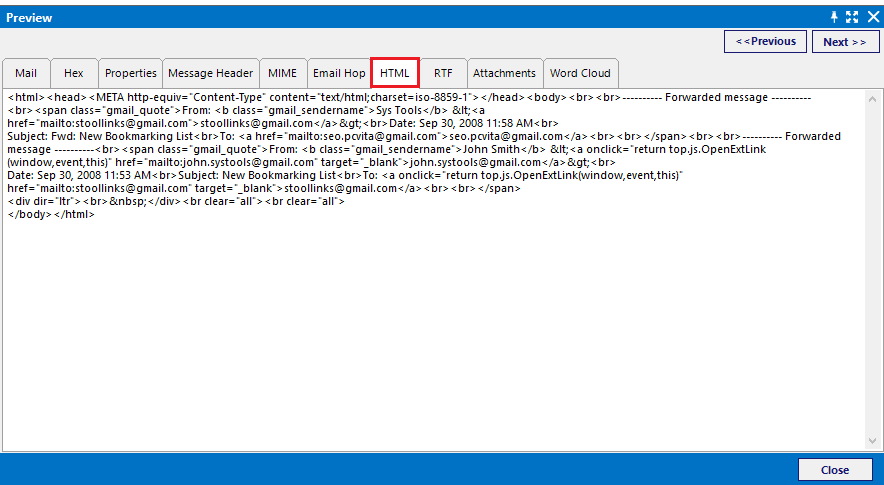
HTML View
This view provides the HTML script code corresponding to the email content. Through the HTML code comparison analysis, the examiner can easily identify whether any actions to remove the originality of the email message.
RTF View
If the email contains the Rich Text Formatting, then it will represent through this RTF view. In digital forensics, this view helps investigators to recover evidence by comparing and analyzing the original formatting of the email message.
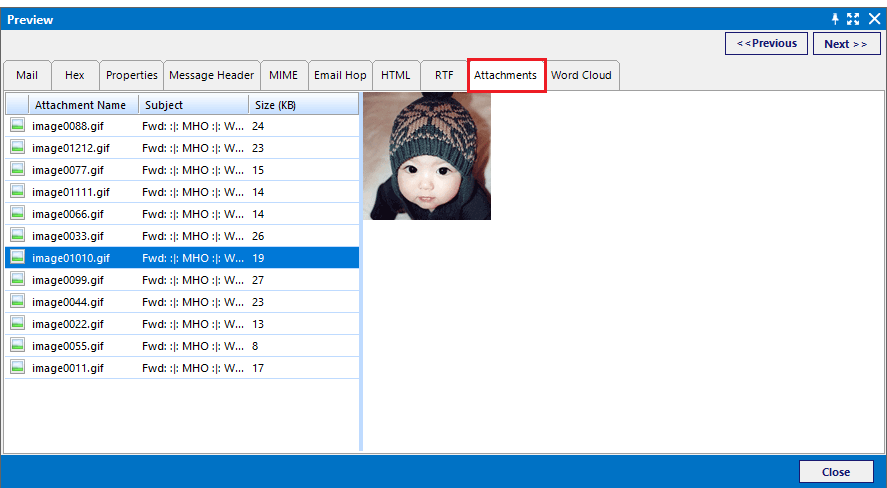
Attachment View
The “Attachment” view helps the user to examine the attachment separately without considering the content of the email message. It provides the list of attachments present within the email and allows previewing it.
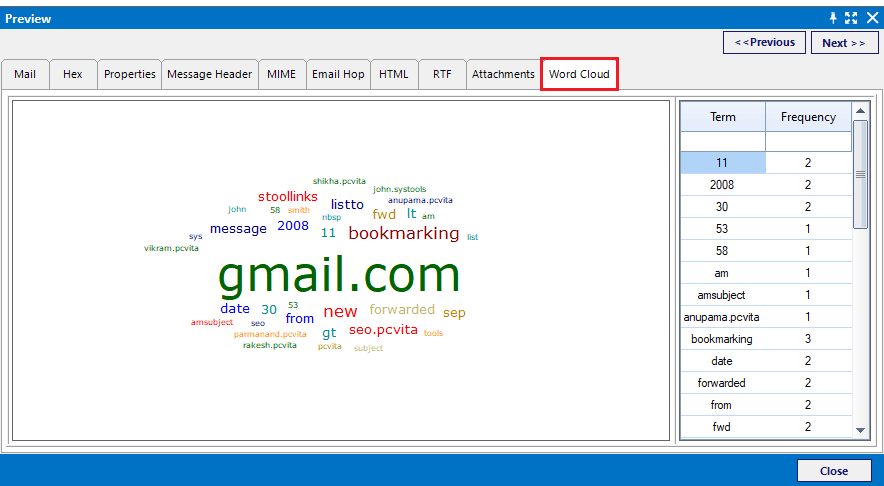
Word Cloud View
This view allows investigators to view the email files in pictorial form. Word Cloud view of the email file will represent the visual representation of words used in the data file. The tool displays words in different sizes which is directly proportional to their frequencies.
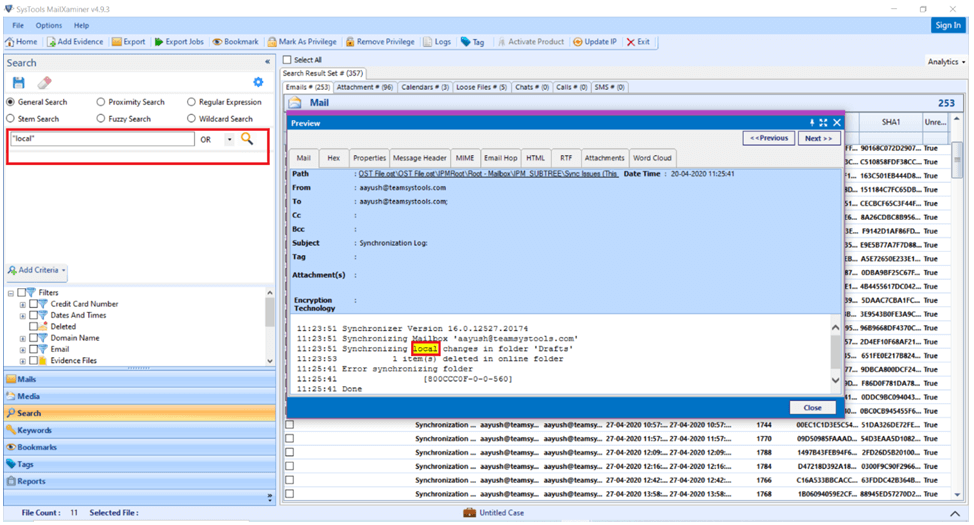
Search Suspected Evidential Files using Advanced Searches
Through the Advanced Search option, the software allows performing Netscape email backup analysis in a more precise way. The tool helps to search easily and extract the evidence from the email data with help of logic operators AND, OR, NOT, and various Search algorithms such as “General, Proximity, Regular Expression, Fuzzy search, Steam search, and Wildcard” etc.
Final Words
During Netscape forensics, email files always act as the primary source of evidence. Netscape email backup analysis always helps investigators to extract the evidence from the Netscape mailbox in an efficient way. With the help of forensic analysis tool MailXaminer, the investigators can easily search and perform Netscape mailboxes analysis through various forensic advanced features.

