Search PST Files for Keywords without Outlook Easily
Overview: Many email forensic experts and law enforcement agencies need an advanced solution that can help them search inside PST files without Outlook. This article discusses one such solution that offers multiple search types and permits users to load multiple PST evidence files without any hassle. Know more about the solution in detail below.
Microsoft Outlook is one of the most preferred email applications that stores/exports its data in PST file format. Since PST file store almost the entire data of Microsoft Outlook, it is primarily used by email investigators to look and search for specific evidence within PST files. Moreover, if you have a certain set of keywords, performing email analysis becomes quite simple and effective. Before that let us see the reasons as to why
Why Won’t PST Files Open for Search in the Absence of Outlook Client?
Directly double-clicking on a PST file pops up a notification that these types of files are only accessible from an Outlook client. So, how to view the contents of PST files without the Outlook app?
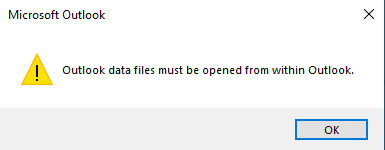
As even when you have a working copy of the client, you can’t open the files on your own you have to launch the client first, import the files to a preconfigured account, and only then can the files become searchable.
If you attempt to bypass it by trying to see what’s inside the PST using a free text editor like Notepad as unlike MBOX, the Portable Storage Table is a proprietary file format whose intellectual property rights stay with Microsoft.
Moreover, due to enhanced security features, you will only end up with encrypted gibberish that cannot be read or used for any sort of forensic examination. Neither the new Outlook desktop variant nor the Web-only version allows the upload of these storage tables.
Attempting any further tries of this may make unwanted and unintended changes inside the evidence, rendering it useless for any further investigation.
Thus, a proficient Email Forensics Tool is required that can help you load multiple PST files into it and help perform in-depth search PST files for keywords.
Know more about the solution in the following section.
How to Search Inside PST File Using Keywords?
In order to perform searches within PST files, you need to use the most advanced software i.e. , MailXaminer. This is one of the best solutions that enables you to add multiple email data files, including PST files, into the software. Following that, the tool performs thorough Indexing within the PST file and ensures that you can search PST files for keywords.
The tool also comes with OCR (Optical Character Recognition) capability, using which this tool can also perform searches within the attachments and images. Thus, if you are looking for an all-in-one solution, this is the perfect solution to help you perform searches within PST files without Outlook.
Along with OCR forensics there are multiple search options as well that you can use to make sure you find the desired evidence without putting in additional effort. There are many other advanced features as well loaded in this application that make it a one-stop solution for all email forensic investigators.
You can schedule a free demo with our experts and get to know more about our software in detail.
Highlighted Features of this Tool
This software allows searching inside the PST file without the installation of Microsoft Outlook Email Client. It provides the following features:
- Facilitate multiple email views for the forensic analysis of damaged, password-protected & healthy PST files.
- Dig into suspected PST files & search for the evidence by using specific keywords and various search algorithms.
- The tool enables to create an evidence list with bookmarked selected emails & attachments.
- The tool provides multiple searches based on advanced algorithms such as General, Proximity, Regular Expression, Stem, Fuzzy, and Wildcard Searches.
- Multiple analytics options are available to perform systematic evidence search i.e., Timeline analysis, Link analysis, and Word Cloud analysis.
- Provides OCR technology to examine textual data from image attachments in emails.
- Its bookmark and tagging feature allows users to save evidence for further investigation.
A Guide to Search PST Files for Keywords Without Outlook
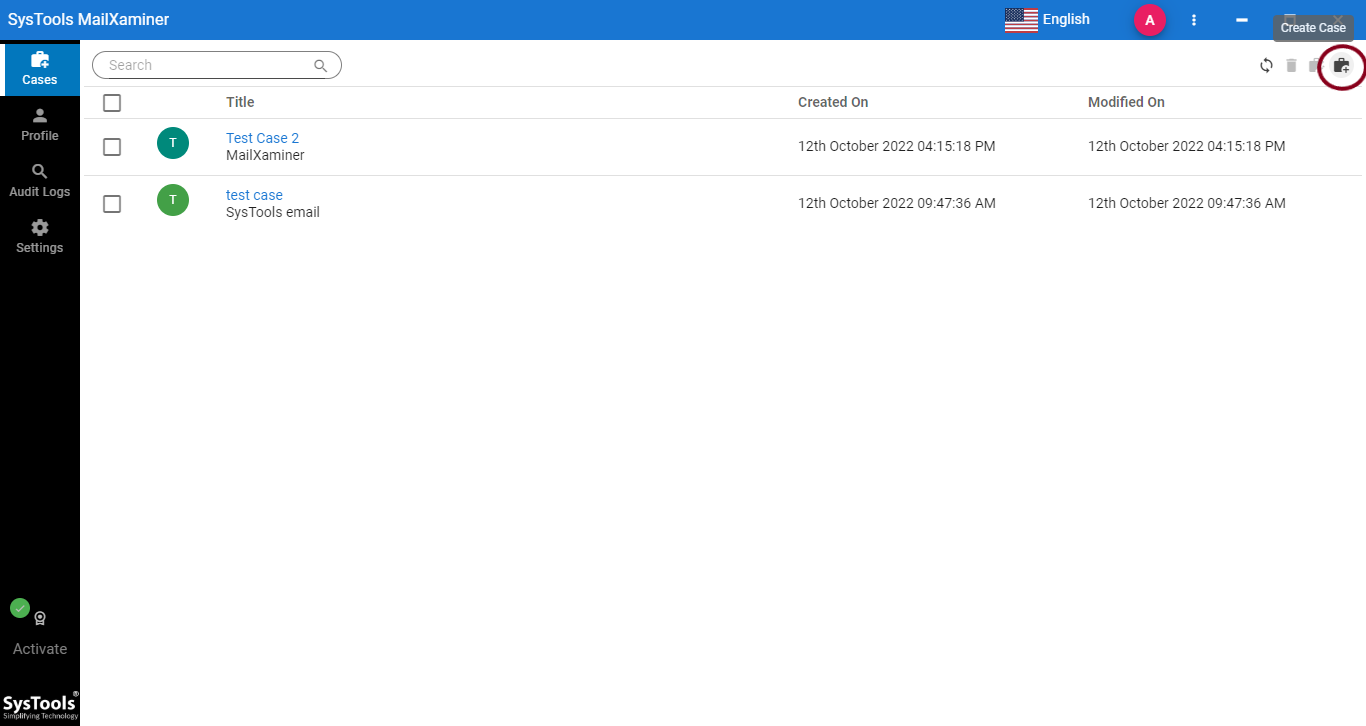
Step 1: Case Management
To conduct PST file forensics, start by creating a new case. You may also use any premade case for analysis and resume examination.
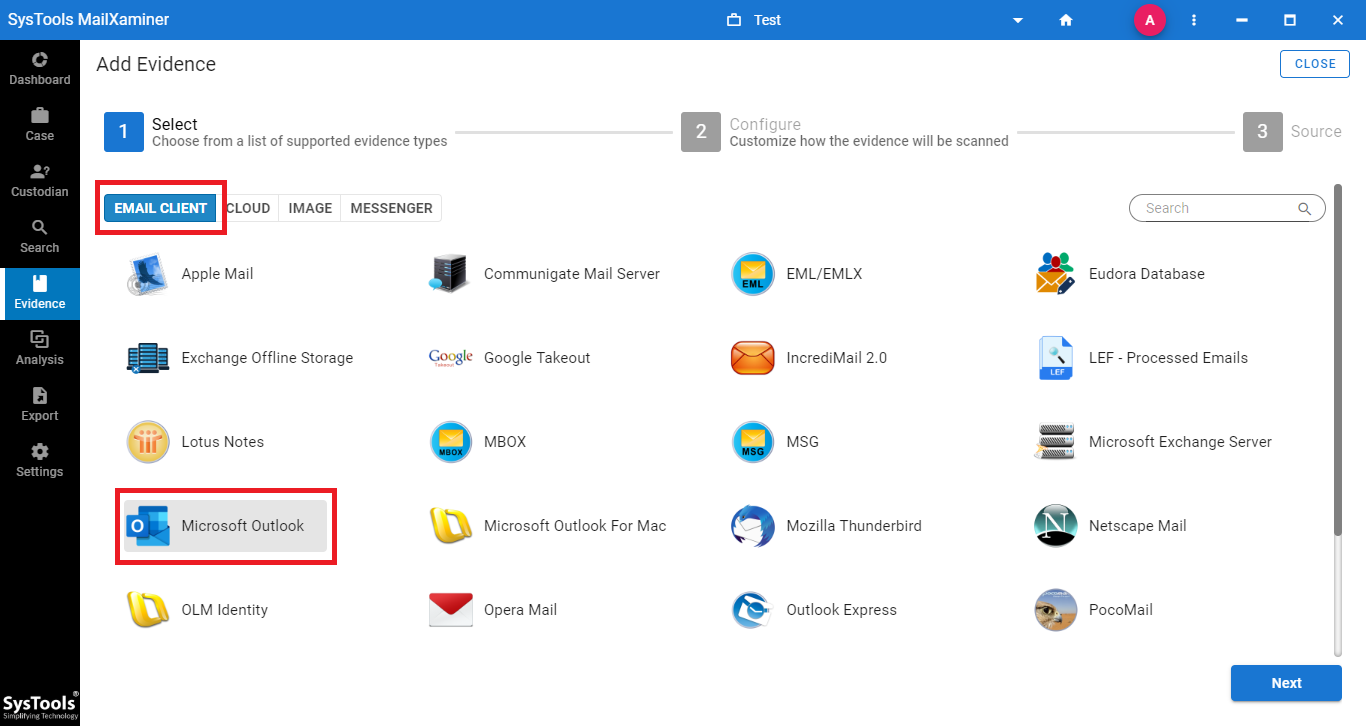
Step 2: Add PST File
Inside a case, click on the Add New Evidence button. A new window will pop up. Here, select the Microsoft Outlook (*.pst) option under the Email Client tab and browse the suspected PST data file to add it to the software.
NOTE: – User is not required to install Microsoft Outlook to perform any operation on Microsoft Outlook if the user is following this method.
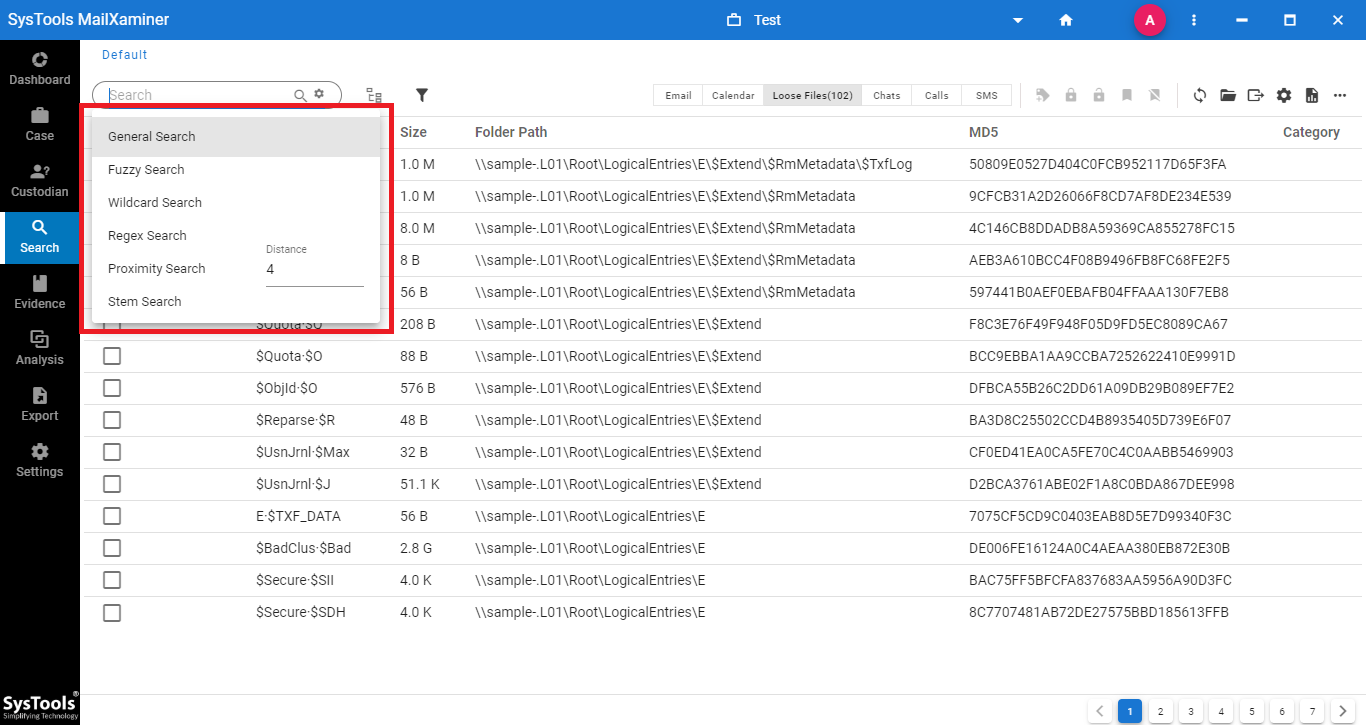
Step 3. Search Option
After uploading is done the PST files are ready for investigation. Investigators can search PST files for keywords, bypassing all Outlook requirements.
Go to the Search section on the left menu panel. There you can find many advanced algorithms such as
- General Search
- Proximity Search
- Regular Expression
- Stem Search
- Fuzzy Search
- Wildcard Search
With these search options, investigators can extract the required evidential files in a hassle-free manner.
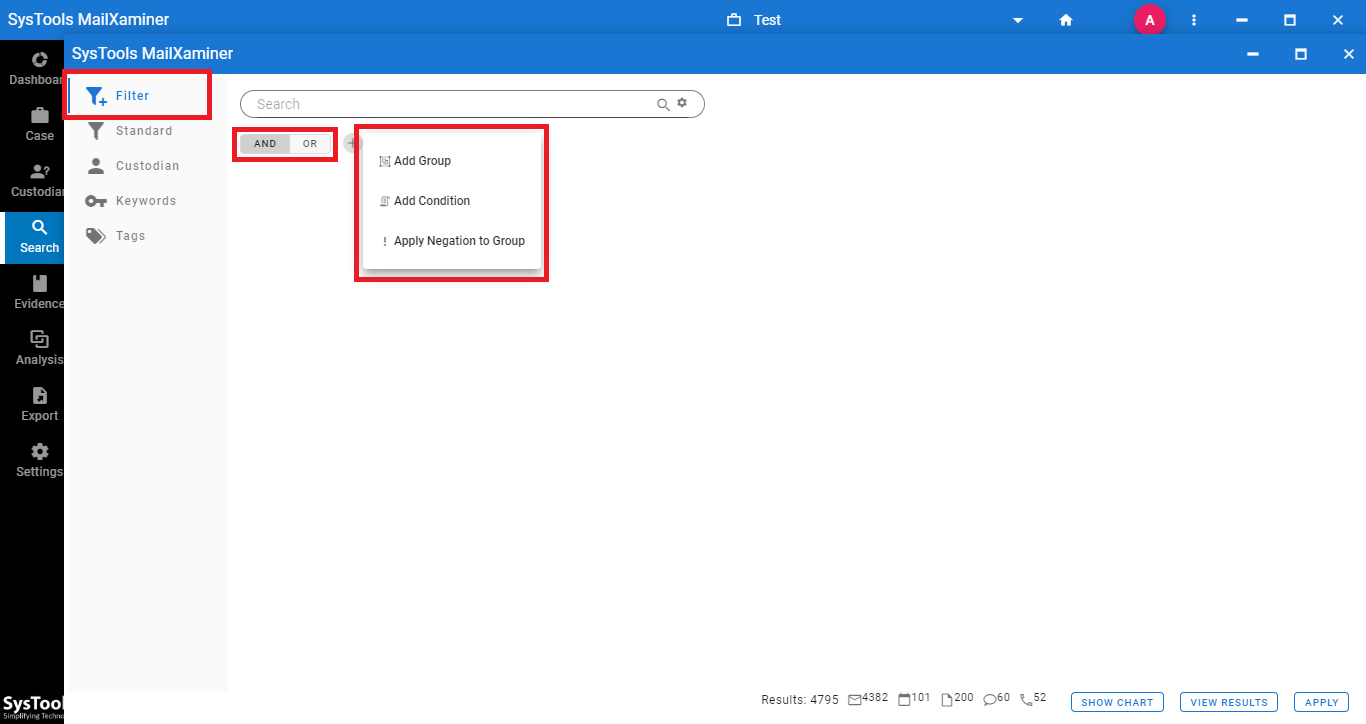
Step 4: Use Search Filters and Logical Operators
The tool provides options to customize the search by adding filters while searching for evidence in files. Use the Filters button and Logical Operators such as AND, OR, and NOT to search PST files for keywords.
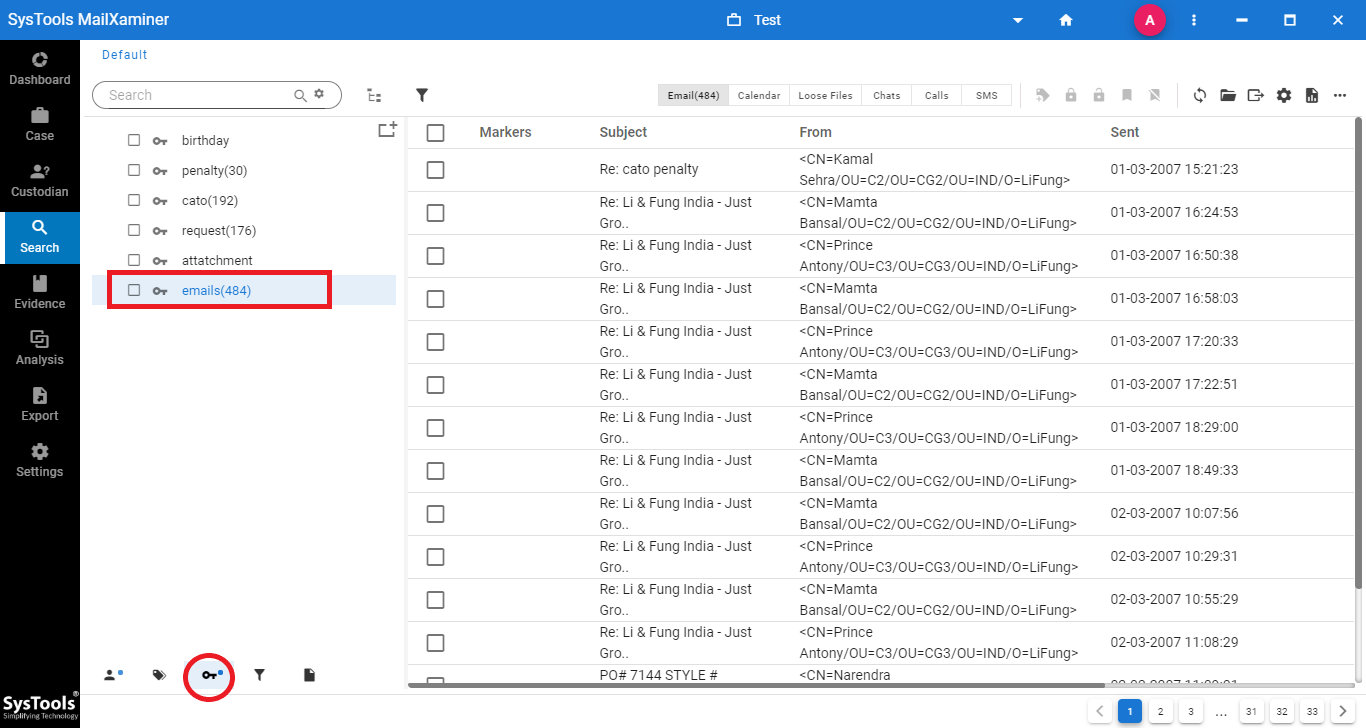
Step 5: Extract Evidence with Keyword Searches
With the Keywords pane, users can instantly fetch the evidential files belonging to a particular set. The tool automatically scans the entire evidence list and puts forth the contents that match the query. There is no limit on the number of keywords, so you can customize as per the case requirements.
With more exploration of the available features, detectives can search inside PST files without Outlook installed with this powerful software.
Conclusion
In order to perform forensic analysis of suspected Outlook PST files, one can bypass Outlook requirements. For this scenario, the above-mentioned software is most suitable. It is one of the most power-packed and super-fast software, which works with 100% precision because of its advanced functionalities. This forensic tool not only lets you search PST files for keywords without Outlook. So you can perform a variety of searches on data files to carve out the evidence in a detailed manner.

