How to Maintain Chain of Custody for Digital Forensic Evidence
When an investigator finds out the critical digital evidence, the real challenge begins for him/her. Courts and legal teams often ask a powerful question: How can it be proved that this evidence was never changed? If the chain of custody is not maintained, even strong proof can be rejected. In this blog, we will explain how to maintain chain of custody for digital forensic evidence in such a way that investigator, IT teams, and businesses can ensure their evidence is protected and can be presented in court.
Why Chain of Custody Matters in Digital Investigations
We can think of a detective collecting an extremely important file from a crime scene. This file gets passed through multiple hands.
- Analysts
- Investigators
- Legal teams
Before reaching the courtroom, if no one records who handled, when it was accessed, and where it was stored, then the evidence can become questionable. This is what the digital evidence chain of custody solves.
Chain of custody can be defined as a record which shows how the document was collected, handled, transferred and preserved. From the time it was discovered till the time it is presented in court. As courts need proof that evidence remained authentic, untampered, and traceable in an entire investigation. If documentation remains incomplete the evidence may lose its value.
It can be thought of like handing over the keys to our motorbike. Each time the key is moved from one person to another, someone records who received it and when they received. If your keys disappear even for a short time without a proper record. People start questioning what happened. Let us check how one can maintain it.
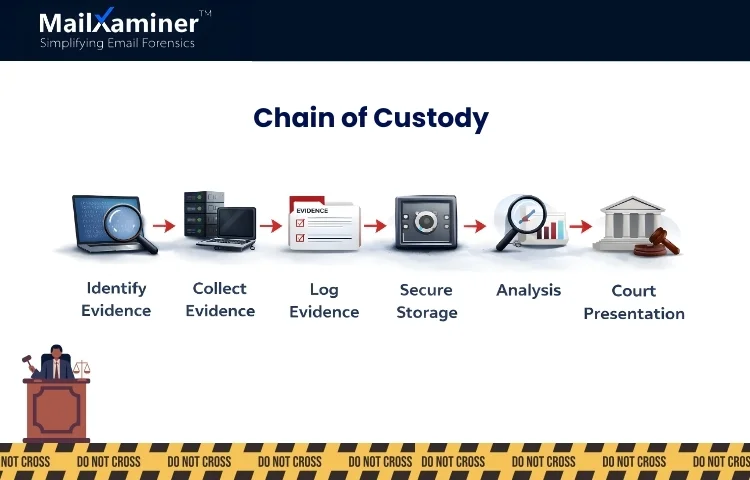
How to Maintain Chain of Custody for Digital Forensic Evidence
Understanding how to maintain chain of custody for digital forensic evidence becomes simple if we break this process into simple and short steps. In these steps, we will learn how investigators follow a structured process and ensure everything remains documented.
Step 1: Identify the Evidence
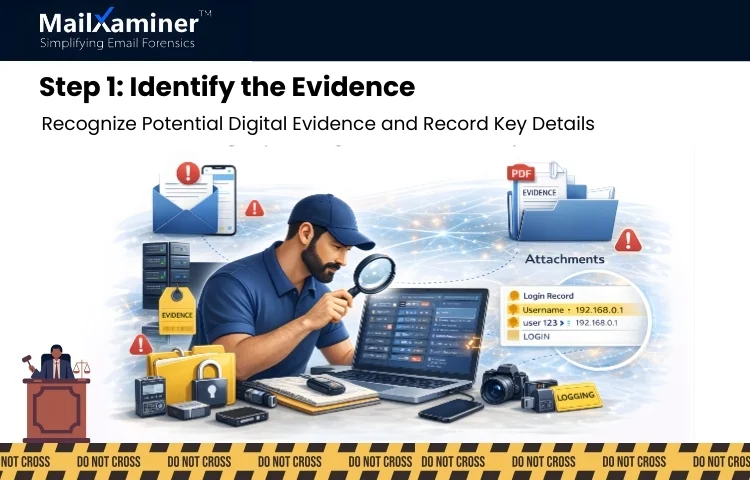
The first and major step is to recognize that this is a potential digital evidence. It can include:
- Emails related to fraud or insider threats.
- Attachment or documents shared between employees.
- Communication logs and records of logins.
- Files are stored in computers, servers, and cloud platforms.
Investigators have to record
- Where the evidence was found
- The device or system that contained it.
- Exact time of discovery.
This step has to be seen as marking a location on a map before the beginning of an investigation. Without marking the location, the investigation can lose its direction.
Step 2: Collection of Evidence
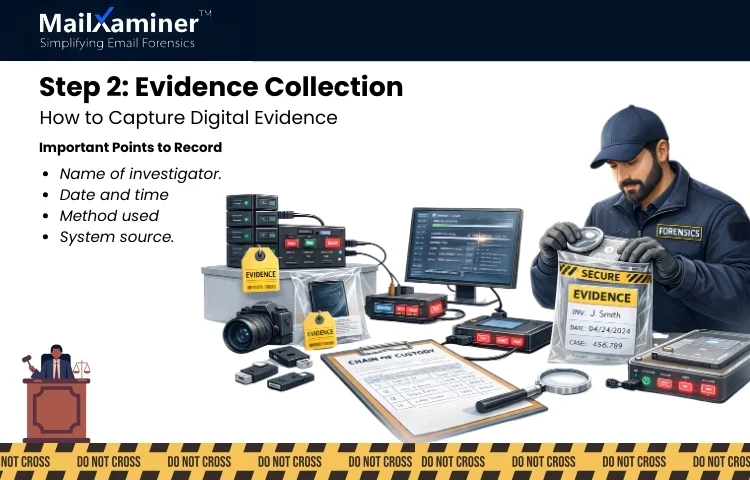
Once the evidence is identified. Investigators have to collect it using forensic methods. In the process of collection, they must record:
- Name of investigator.
- Date and time of collection.
- Method used to collect the data.
- Device or system source.
The goal here is capturing the evidence exactly as it exists without alteration. Even a small change like opening it incorrectly can modify the internal details like metadata and raise doubts later. We hope that you are now getting some clarity on how to maintain chain of custody for digital forensic evidence. If yes, let’s dig deeper.
Related read – Corporate espionage investigations, how investigators uncover hidden data
Step 3: Create a Detailed Evidence Log
Chain of custody is like a tracking sheet of digital evidence. Every time when the evidence moves, or it is accessed, the log records are updated.
| Evidence Event | Information Record |
|---|---|
| Discovery | Where the evidence was found and who discovered it. |
| Collection | Method used, time of collection, and the device or source. |
| Transfer | Details of who received or handled the evidence. |
| Storage | Location where the evidence was securely stored. |
| Analysis | Information about the examiner who analyzed the evidence. |
This log becomes the timeline that proves the integrity of the evidence.
Step 4: Secure Storage of Evidence
Collected digital evidence has to be stored in an environment that is secured to prevent modification and unauthorized access. Common practices to be followed are:
- Storing of evidence in controlled and forensic environments.
- Usage of read-only copies for analysis.
- Keep the original evidence untouched.
- Restricted access to authorized investigators only.
This is just like placing a valuable item in an extremely secure locker. Only authorized individuals can open it.
Step 5: Document Every Evidence Transfer
Evidence does not stay with one person during the investigation. Analysts, legal teams, and experts may all need access, so whenever the evidence is transferred, each transfer must be recorded.
- Who transferred the evidence?
- Who received it?
- Date and time of the transfer.
- Purpose of assessment.
In this process, even if one transfer goes undocumented, the chain of custody breaks, and evidence can be questioned. This is how to maintain chain of custody for digital forensic evidence.
Risks of Handling Digital Evidence Manually
Many investigations still depend on spreadsheets and manual documentation for evidence tracking. These approaches can work for smaller cases. It often creates serious risks.
In these manual methods human errors can happen. Investigators may forget:
- To log a transfer
- Mistyped timestamps
- Misplace files.
In a process these small mistakes can create gaps in the evidence timeline.
Another risk is metadata loss. As digital evidence has hidden information such as,
- Creation time.
- Sender details
- File history
If that evidence is exported incorrectly, the metadata can disappear, making it extremely difficult to prove authenticity. This can be thought of as building a case or assembling a puzzle. In this missing metadata is like losing several puzzle pieces. The picture becomes incomplete.
A Smarter Way to Preserve Email Evidence
We will talk about emails now as they are one of the most common sources of digital evidence in corporate investigations. Fraud, insider threats, and violations often leave traces in email communication. In corporate espionage investigations most common source of evidence is emails.
Modern forensic solutions like MailXaminer help investigators:
- Examine large volumes of emails efficiently.
- Maintenance of evidence integrity during examination.
- Preserving of email headers and metadata.
- Tracking of investigation steps in an organized manner.
As a manual approach increases the chance of accidental errors, a tool-based approach can assure you accuracy.
Common Mistakes That Break Chain of Custody
We now know how to maintain chain of custody for digital forensic evidence. Many investigators still face problems because they repeat small mistakes, which can be avoided which are.
- Accessing evidence without recording it in the log.
- Sharing of evidence files through emails or insecure channels.
- Export of evidence without metadata preservation.
- Allowance to multiple investigators for modification of the same data copy.
These mistakes lead to uncertainty about whether the evidence was altered or not.
Related read – How to authenticate emails for evidence
Closing Thoughts
Digital evidence is extremely powerful, but only when it is trusted. A well-maintained chain of custody can prove that the evidence is authentic from the time it was discovered until the time it was analyzed.
If one can carefully identify evidence, document every action, protect metadata, and store data securely. Findings remain credible in court. Understanding how to maintain chain of custody for digital forensic evidence is not a technical process. It is the foundation that protects the truth.
Frequently Asked Questions
Q – Why is documentation needed when handling digital evidence?
Proper documentation gives a brief of who accessed the evidence and when. It helps prove that the evidence was not altered during the investigation.
Q – How can investigators reduce mistakes during evidence handling?
Investigators can reduce mistakes by using structured procedures and dependable investigation tools, which help track every action and can protect the integrity of the evidence.

