What is Email Bombing in Cyber Crime Guide for Investigators
Picture this – You are working in your company on a normal day, and suddenly your email inbox explodes with thousands of emails in minutes. Alerts, random messages, you start receiving everything at once. You don’t know what is happening. This is not spam; it is a cyber attack. In this write-up, we will explain what is email bombing in cyber crime and how to investigate it step by step.
What is Email Bombing in Cyber Crime
It is a cyberattack where the target inbox is flooded with a large volume of emails quickly, within minutes. The goal of this attack is to distract and hide something more dangerous. To understand this, we can think of it like a thief who is triggering multiple alarms in a building to confuse the security team while the real theft can happen quietly.
Email bombing is not annoying. It is used as a cover for cyber crimes like account takeover, financial fraud, and data theft.
Why Email Bombing Is a Growing Threat

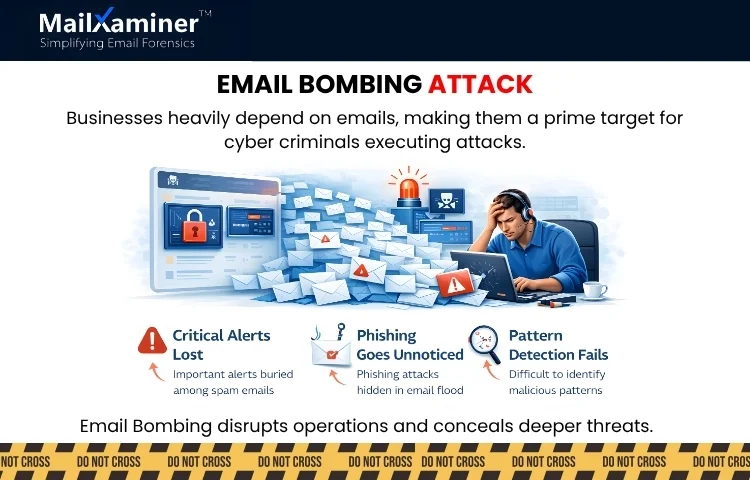
These days, businesses depend heavily on email as their daily communication channel. This makes it a perfect spot for cyber criminals. Attackers use this dependency of corporates on emails to execute attacks that really disrupt the business operations, waste IT resources, and cover more complex intrusions.
When email bombing starts, IT and security teams feel like air traffic controllers losing radar visibility. Thousands of emails appear at once, and it becomes almost impossible to identify which message is genuine and which are malicious. Due to this;
- Critical alerts get lost among other emails.
- Phishing attempts can go unnoticed.
- Investigators struggle with malicious pattern identification.
This confusion delays response and sometimes results in loss of sensitive information. We hope you are getting some clarity on what is email bombing in cybercrime.
Related read – How to write a digital forensic report
How Email Bombing Works
To make email bombing work, attackers use automated tools to send multiple emails in minutes. These emails are developed to look legitimate. They feel like:
- Newsletters and service confirmations.
- Fake account registrations.
- Random messages that look like they came from trusted domains.
Common types of email bombing:
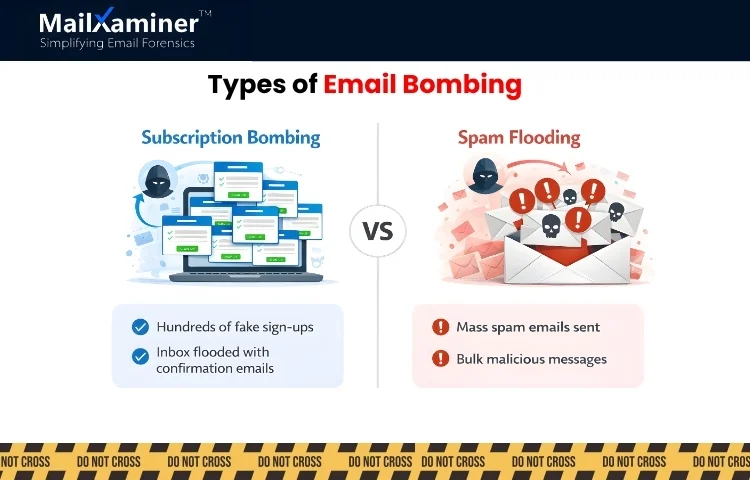
- Subscription bombing: Sending messages to the target email with hundreds of service sign-ups to overwhelm inboxes.
- Mass spam flooding: Directly sending malicious emails in bulk to create confusion.
To really understand email bombing, we can see it as dumping thousands of papers on your office desk so you can’t locate one important document that matters.
Why Detecting Email Bombing is Challenging
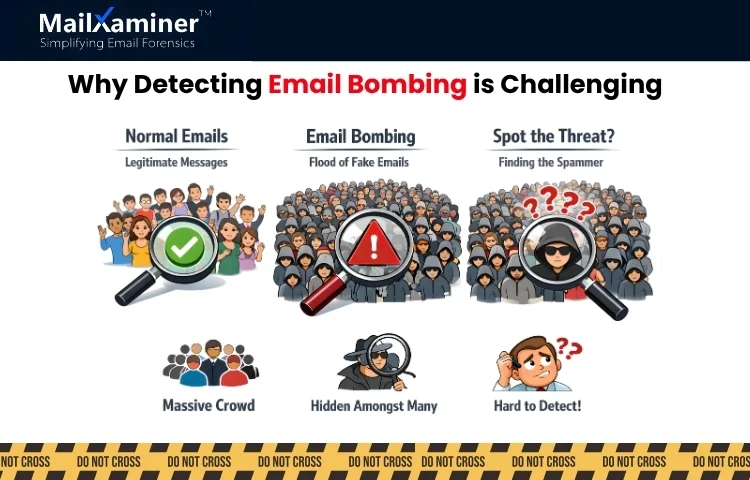
Now we know what is email bombing in cyber crime. Let’s discuss why its detection is challenging. The difficulty lies not just in the volume but in discerning malicious patterns within the legitimate-looking emails. There are some technical reasons why detection fails, which are as follows.
- The sender’s address attackers use looks legitimate.
- Logs and email metadata are scattered across servers.
- The volume of emails is sometimes so large that it exceeds manual processing capacity.
Finding malicious activity here is just like spotting a single suspicious person in a crowded stadium where everyone appears normal.
Manual Investigation and Its Limitations
After an email bombing attack, the next step security teams take is to manually analyze emails. They:
- Scroll through inboxes.
- Filter messages by a sender or keyword.
- Check headers individually.
This manual investigation becomes slow, error-prone, and inefficient. In manual investigation, critical evidence can be missed, leading to a delayed detection and potential financial and operational losses. Some of the common mistakes investigators make are.
- They ignore metadata that reveals many elements like origin and routing.
- Their focus remains on content rather than the patterns.
- Not connecting multiple emails to identify the coordinated attacks.
Even a single oversight can let attackers succeed in performing malicious activity.
Related read – Corporate espionage investigations, how investigators uncover hidden data
Smarter Investigation Approach
In an email investigation every data point has a value. Instead of reading each email and analyzing it one by one. Investigators need a tool that:
- Helps in organizing chaotic data.
- Detects patterns across emails.
- Highlighting anomalies and suspicious activity.
- Helps in extracting evidence for legal and internal investigations.
The structured approach helps and ensures no critical information is left. Once you know what email bombing is in cybercrime, solving it effectively needs a professional tool like MailXaminer.
How a Professional Tool Helps Investigate Email Bombing
A good professional tool is designed to perform sophisticated email forensic investigation. With the help of this one can solve email bombing via:
- Mass Email analysis – This quickly processes thousands of emails.
- Pattern and Timeline Detection – Identification of suspicious sequence and trend so all the emails can be analysed and a pattern can be detected of what truly happened.
- Evidence Extraction – Collect headers, attachments, and hidden metadata.
- Visual Intelligence – Provides easy-to-understand UI in the form of dashboards for investigative teams.
Tools like this act as a control tower during chaos which converts flood of messages into clear, actionable intelligence.
Why This Matters for Organizations
Email bombing is not an IT inconvenience. It poses serious issues like.
- Operational Risk: Slowdown in daily communication can result in missed opportunities.
- Security Risk: Undetected malicious activity.
- Compliance Risk: Missing or incomplete records.
In corporations and businesses, a clear, structured investigation is critical to prevent the loss of data and to strengthen defenses.
Final Thoughts
Email bombing may appear normal, but it is a window to a bigger threat or can be seen as a calculated distraction to hide a more serious cyber attack. Understanding what email bombing in cybercrime is the first step. To deal with these effectively, professionals should follow a tool-based approach that gives them speed, visibility, and intelligence necessary to investigate and respond effectively.
With the right strategy, organizations can turn chaos into clarity. This ensures every email is accounted for and an attack is traceable.
Frequently Asked Questions (FAQ)
Q – How can investigators detect email bombing attacks ?
A – Investigators can detect it by analyzing email patterns, headers, and timelines using dependable approaches like forensic tools instead of manual checking.
Q – What is email bombing in cybercrime ?
A – Email bombing is a cyber attack where an inbox receives multiple emails in thousands to disrupt operations or to cause malicious activities.

