Examine Office 365 Mailboxes
In Office 365, a lot of Office application with Cloud-Based Services offered by Microsoft such as Exchange Online, Outlook, Skype, One Drive, and Share Point and Cloud-based software. Now Mailxaminer Email Forensics Tool equipped with features to access to Office 365 to access mailboxes to retrieve precious information stored in an Administrator or user mailboxes. The tool forensically scans the entire Office 365 database and let you find everything which is related to your search parameter.
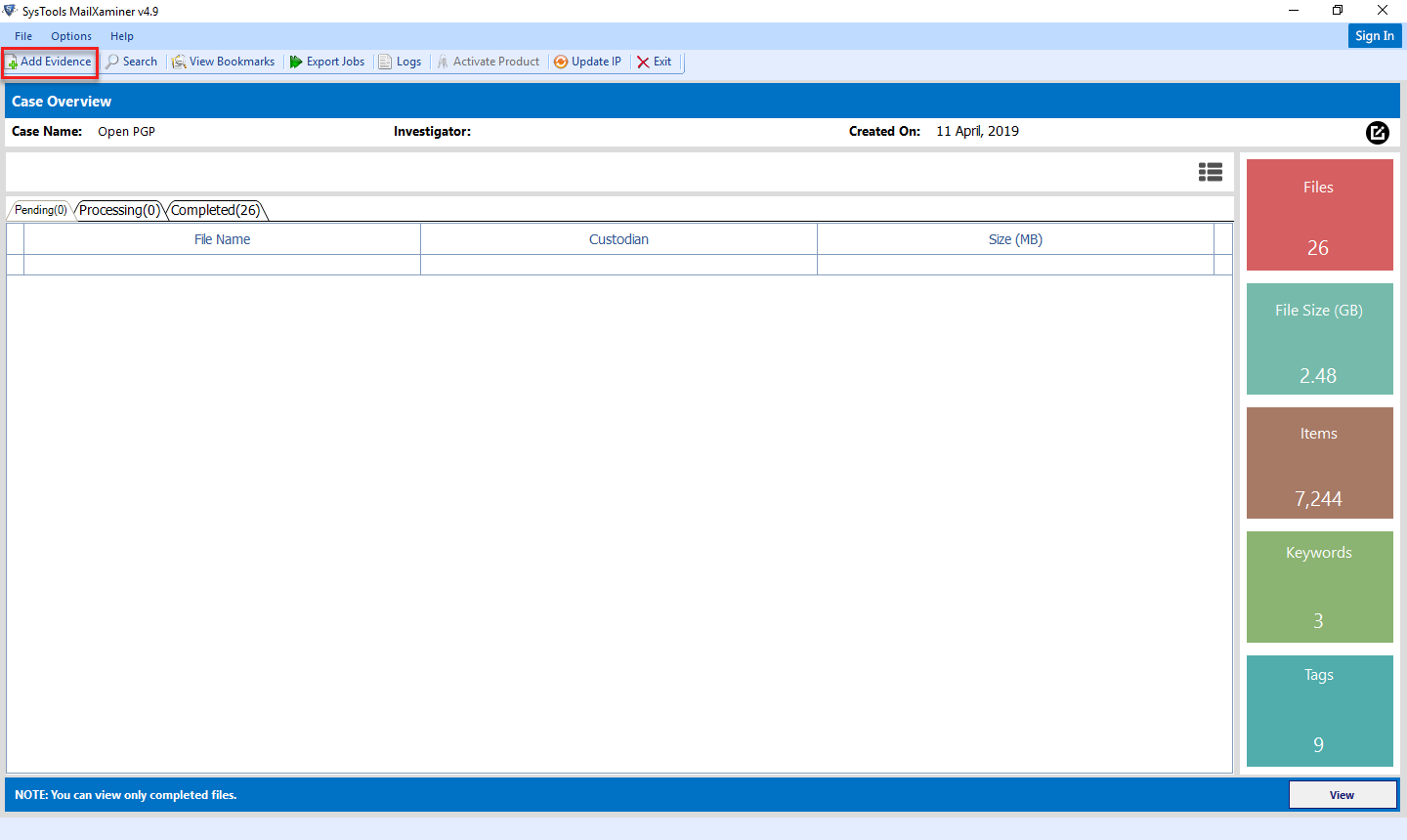
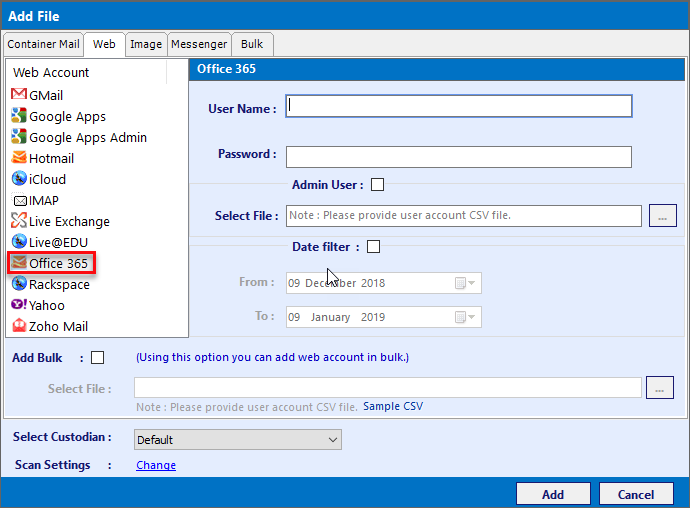
To Access Office 365 mailboxes, File need to access the Account for that, Click on "Add Evidence" >> "Web" >> Office 365
After selecting the Office 365 field from left side navigation panel, the Office 365 pop – up window appears.
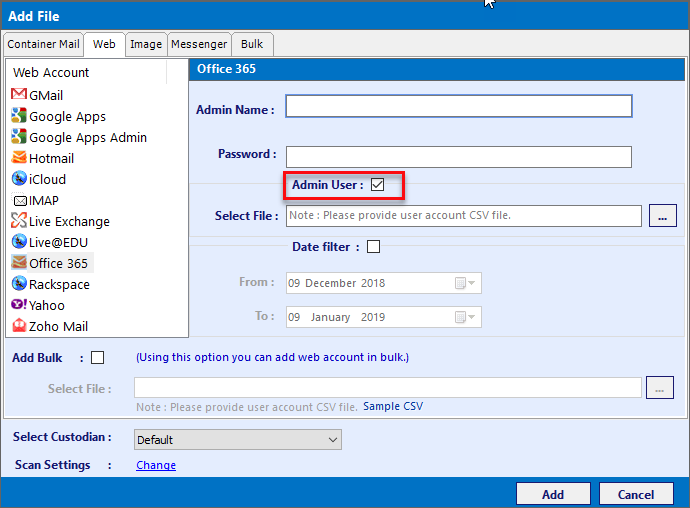
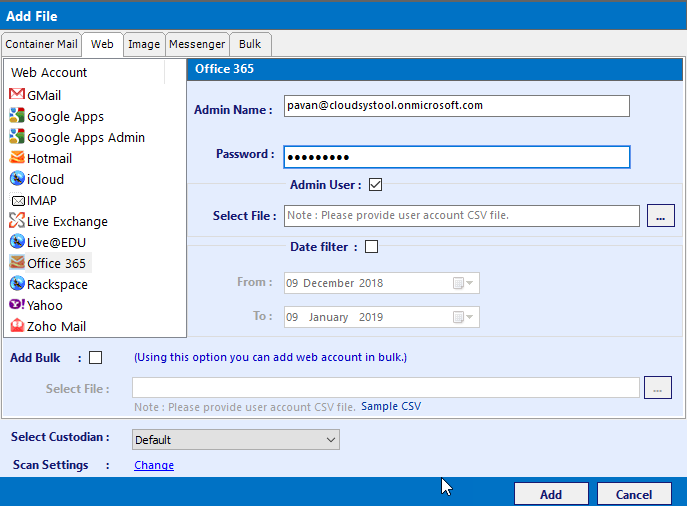
The Office 365 pop – up window asks the investigators to provide details for the following fields: -
- Admin: - Select option when Accessing Account as Administrator
- User Name: -Provide the Admin Username for the admin account
- Password: - Provide the Admin Password for the admin account.
- Date Filter: - This field requires the domain name of the corresponding Server.
Investigators very often face a challenge regarding the availability of account credentials while analyzing corresponding mailboxes. To assist the investigators with this part of the analysis, Software allows the investigators to analyze the Office 365(Exchange Online) mailboxes through a using impersonation features. The software provides a dual option of analyzing the Exchange Online Mailboxes in one of the two modes i.e. With Impersonation and Without Impersonation techniques.
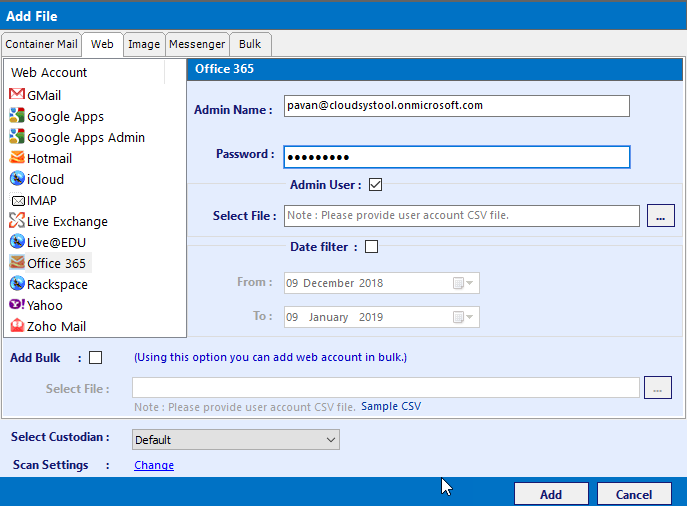
Without Impersonation: In this method, you need to provide User Mailbox Credentials such as "User Name and Password". Software validated the mailbox credentials and if all details are verified then software displays the details of the data items stored in user mailboxes.
Administrator Credentials: To Use this method, check the box of "Admin User". Now provide Administrator details such as "User Name and Password"
View the Details of User mailboxes items in Preview Pane.
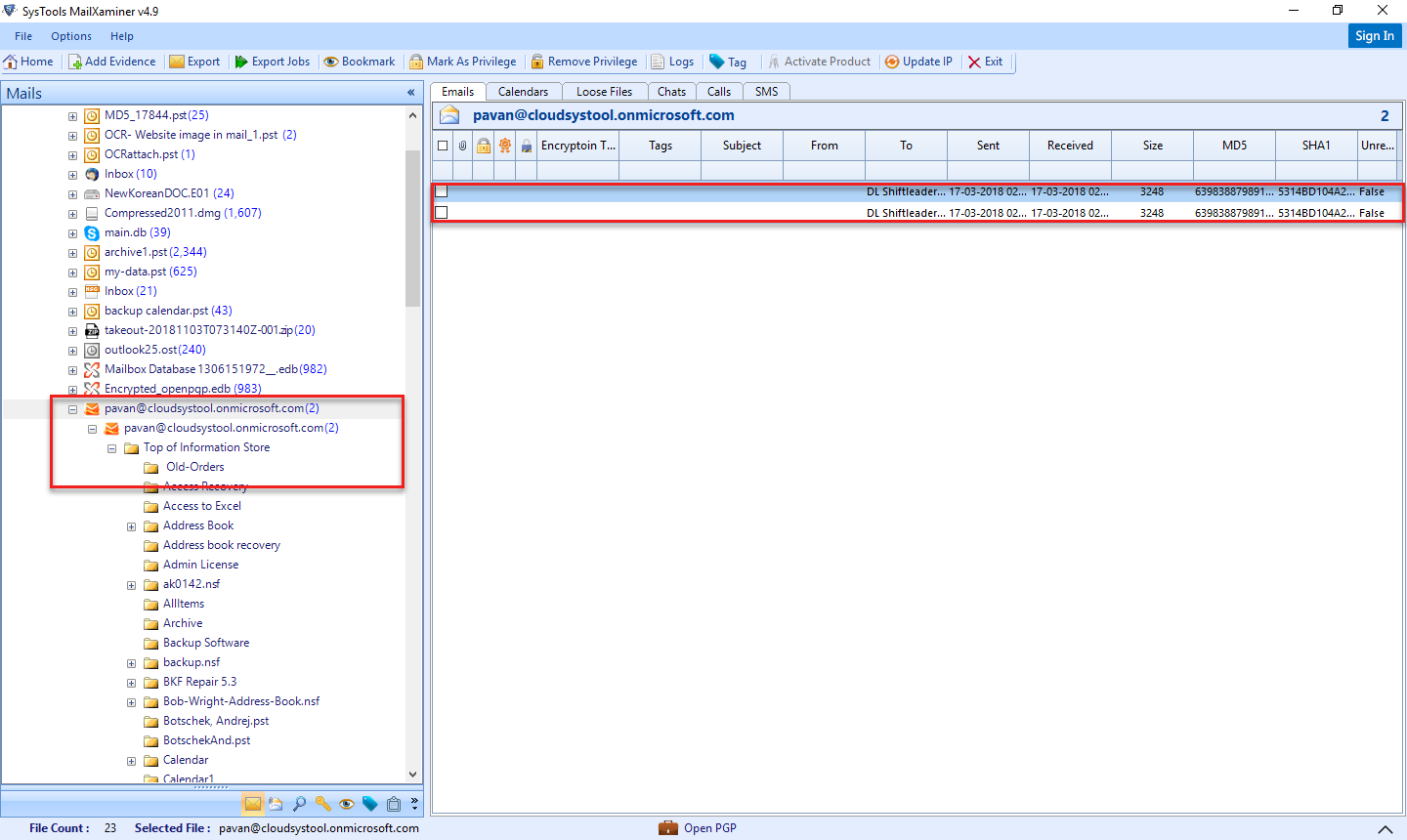
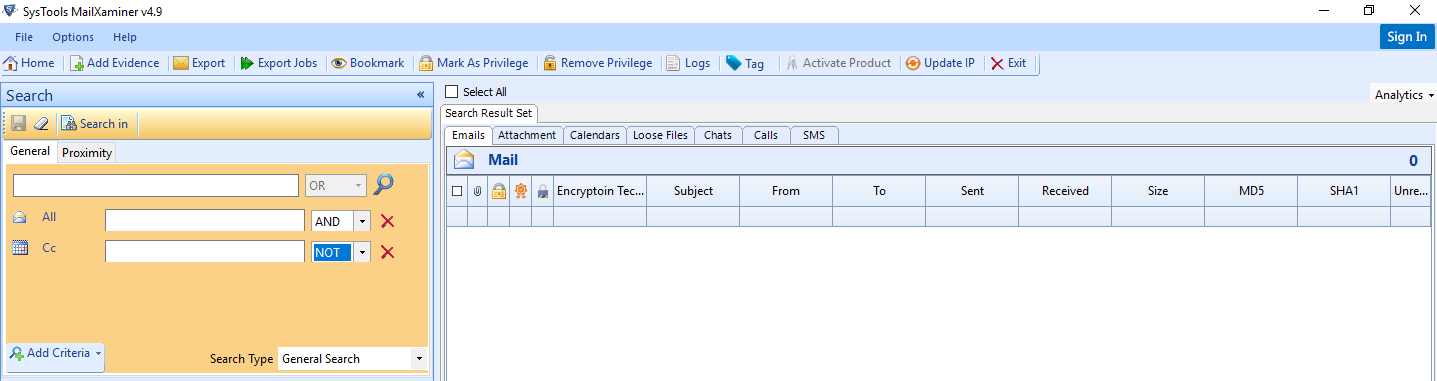
Now to perform eDiscovery search in Office 365, the investigator is required to move to the search pane available in the software.