Zimbra Email Forensic Analysis – A Detailed Research
Zimbra Desktop is another desktop email client that is highly demanded worldwide. Zimbra email forensic is equally trending nowadays. It is used by a wide range of users across the globe whether they are home users or professionals. This email client is an open-source application and highly demanded as it can be availed free of cost.
Nevertheless, there are many other reasons as well, such as its advanced features, easy-to-operate, etc. Moreover, it has the ability to be supported on cross-platforms like MS Windows, Apple’s Mac and, Linux operating system.
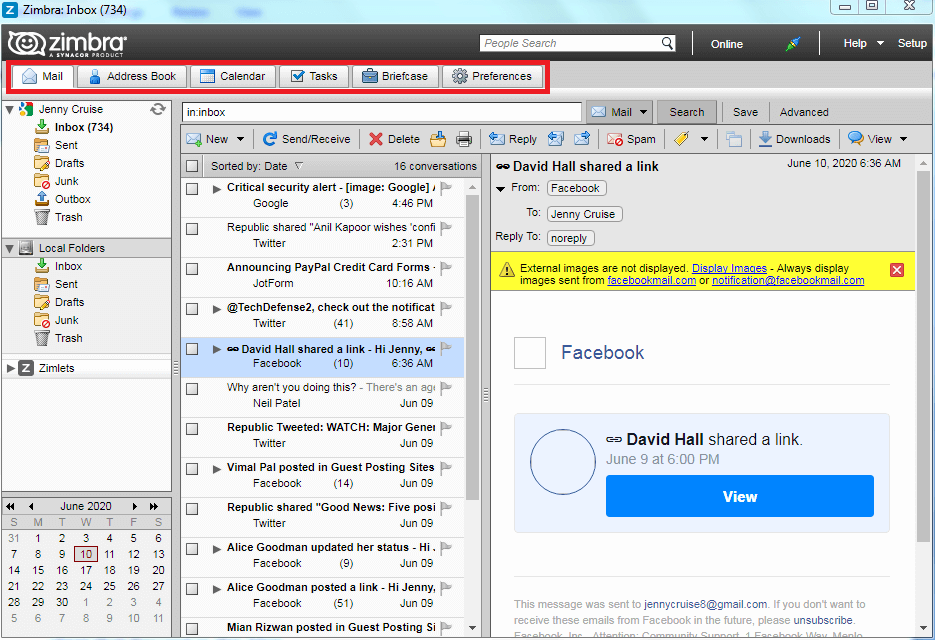
Zimbra can also work with several web based mail programs to sync data of emails, contacts, to-do-items, etc. and store the data locally in computer hard drive. It requires internet access during the synchronization as needed by any other desktop client. Once data is being synced, then it can be accessed in offline mode i.e. when the system does not have internet connectivity. To store user’s data, it contains categories like Mail, Address Book, Calendar, Tasks, and Briefcase.
Zimbra Email Forensic Examination
The vast use of Zimbra Desktop client for emailing purposes made it a destination or rather say target of cybercrimes. Nowadays, it has also become the host of many digital offenses. In order to prove the crime conducted with the Zimbra email program, it gets necessary to conduct Zimbra email forensics investigation. Here, the trouble arises is how to grab important information within the sent or received emails.
It is essential to produce the evidence against suspects which should be in a correct and orderly format so that they become admissible in a court of law. The next section highlights some techniques that can be utilized to analyze the specific email client.
How to Analyze the Details of Zimbra Desktop Emails?
As emails are the most targeted means to commit various kinds of cybercrimes.In a digital forensic investigation, inspection of emails is important because it contains highly significant information that can be collected and presented as evidence. Supported data and facts can also be extracted from the technicalities of emails that are not unknown to normal users. The Zip file forensics is also similar to this.
Below given methods are presented to acquire details from email data and helps to reach out to the offenders. In other words, it can be said that we are going to describe the procedure to perform Zimbra Desktop email forensic analysis.
Method: By Carrying Out Examination of ‘User Data’
Zimbra Desktop allows supporting various kinds of accounts such as: Zimbra, Gmail, Yahoo Mail, MS Exchange (via IMAP) and other emailing services using either POP3 or IMAP4 access. Regardless of the account type or operating system, it works well for all and creates a specific file format to store user data. However, the location of user data within the system varies depending on OS and their different versions. It is necessary for the investigators to know the location of user data files in order to inspect the information that is given below:
User Data Location
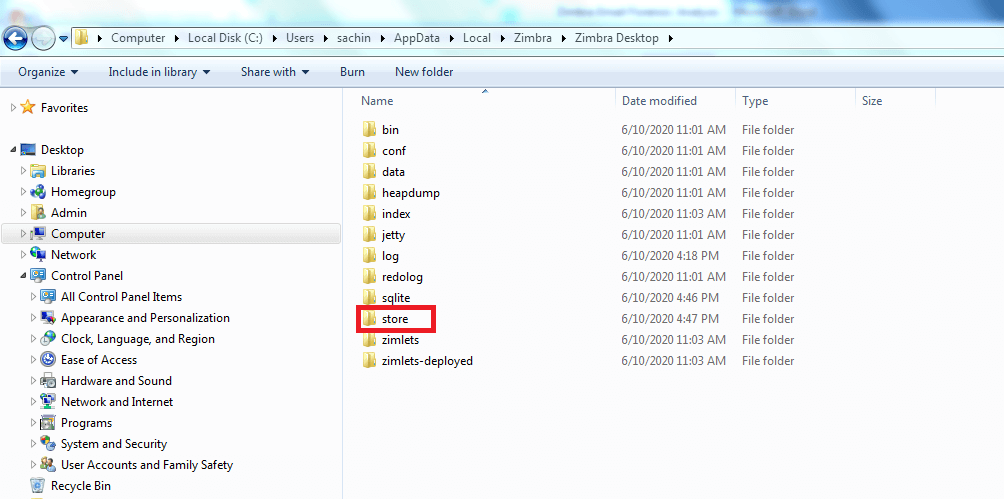
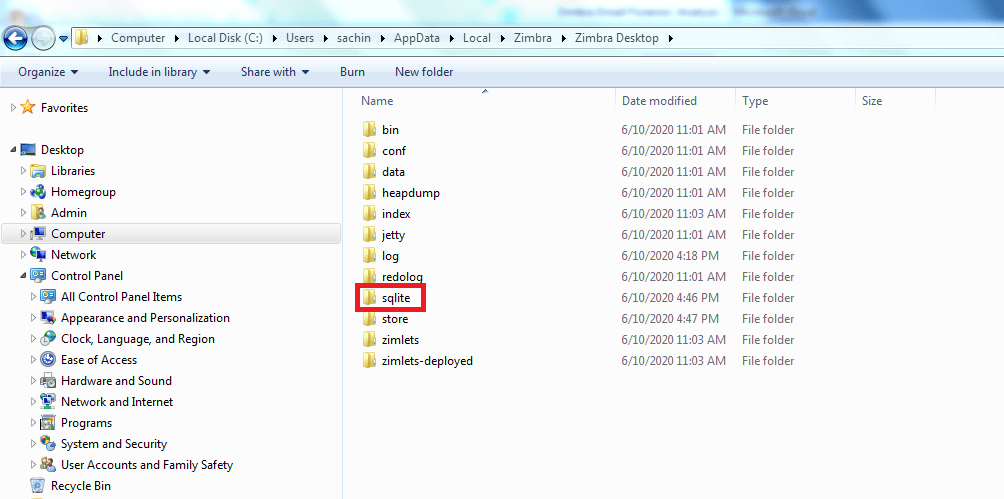
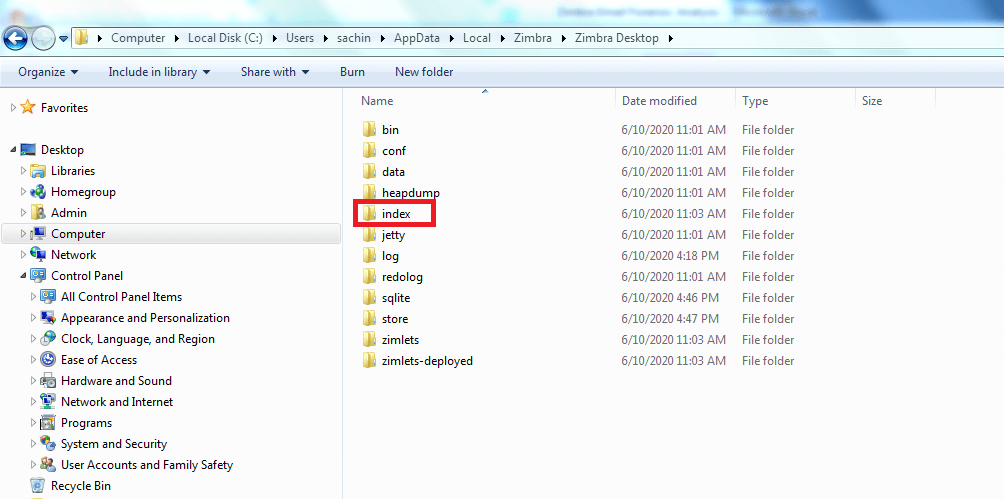
The mailbox data including emails are generally stored at the standard location specified by Zimbra email client. There are three folders that contains all the user data i.e. store, sqlite, and index.
By default, Actual Data is saved in the folder named as “Store” at location
C:/users/admin/AppData/Local/Zimbra/Zimbra Desktop/Store
where each item is saved as a single file.
Metadata is saved in a SQLite database at location
C:/users/admin/AppData/Local/Zimbra/Zimbra Desktop/sqlite
And, Index data is saved at location
C:/users/admin/AppData/Local/Zimbra/Zimbra Desktop/index
Finally, in this way the data files of Zimbra Desktop can be availed and investigated. But there exist a problem mentioned in the section below.
Trouble in Carrying Out Zimbra Desktop Forensics Investigation
Sometimes, all the user data stored in the folders (index, sqlite, and store) may get damage during copying and relocating folders at any other location. In such situation, investigators cannot seize information from it. Hence, it is recommended that before exporting or moving the data items, convert files intoTGZ files. To investigate Zimbra data files including emails, data must be exported into another file format called Tar-GZippedor TGZ file type.
The reason for this migration is that TGZ files can efficiently store all the emails, contacts, calendar, notes, and tasks. Email data available within the TGZ files are proved as the key evidence resources. It encourages forensic examiners to proceed with forensic investigation of Zimbra emails to find the clue that can be obtained here.
Move data from one account to another – Firstly, forensic experts of investigating agencies exports or move all the suspected data from the account(s) for investigation.It includes email messages, attachments, calendar, contacts, tasks and briefcase folders. Then, they save the suspected data into any other system or other locations, or they can even import it to another application.
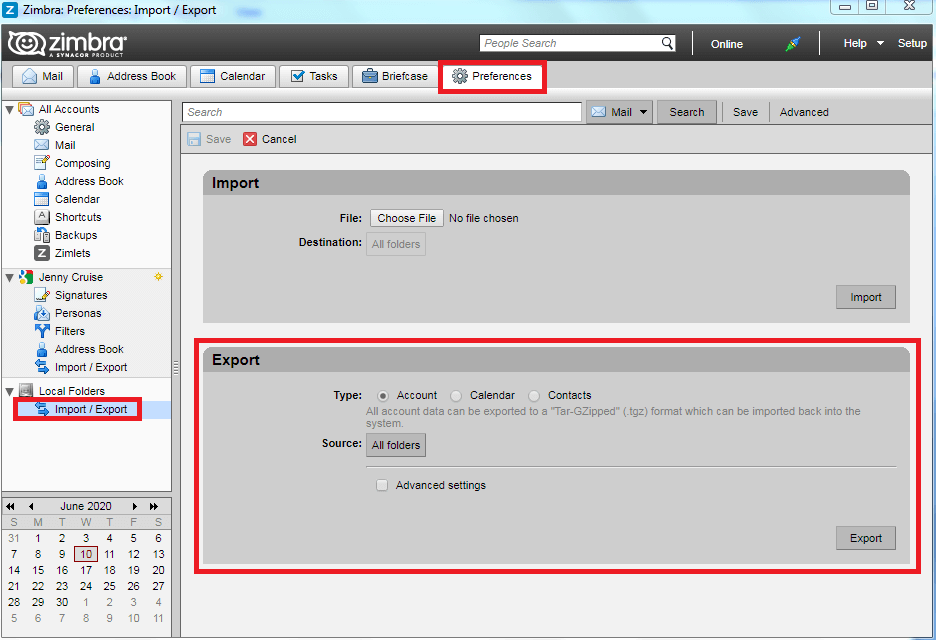
However, for this, the Import/Export feature of Zimbra email program is quite necessary. First task is to export the data items into the .tgz format. Thereafter, import it to the investigator’s computer for investigation. Moreover, data items are in fact copied and not erased from the account. It must be noted that when contact and calendar folders are exported singly they are saved as .csv and .ics file respectively. File can be exported from Preferences >> Import/Export page as shown in the images below.
Conclusion
As we know that TGZ files store the key data that can help forensic investigators during the examination. The complete set of emails is in the “.eml” format in TGZ folders. Experts analyze his email data forensically via MailXaminer. The tool allows forensic examiners to analyze .eml email artifacts to extract email evidence. Thus, law enforcement agencies and investigators can make use of MailXaminer for Zimbra email forensic investigations.

