Zarafa Email Forensics- View Necessary Zarafa Evidences
Databases are the key source of evidence, irrespective of size of organization or complexity in database used. There are different kinds of database applications available from the forensic point of view such as MySQL, Oracle database, ERP systems, etc.
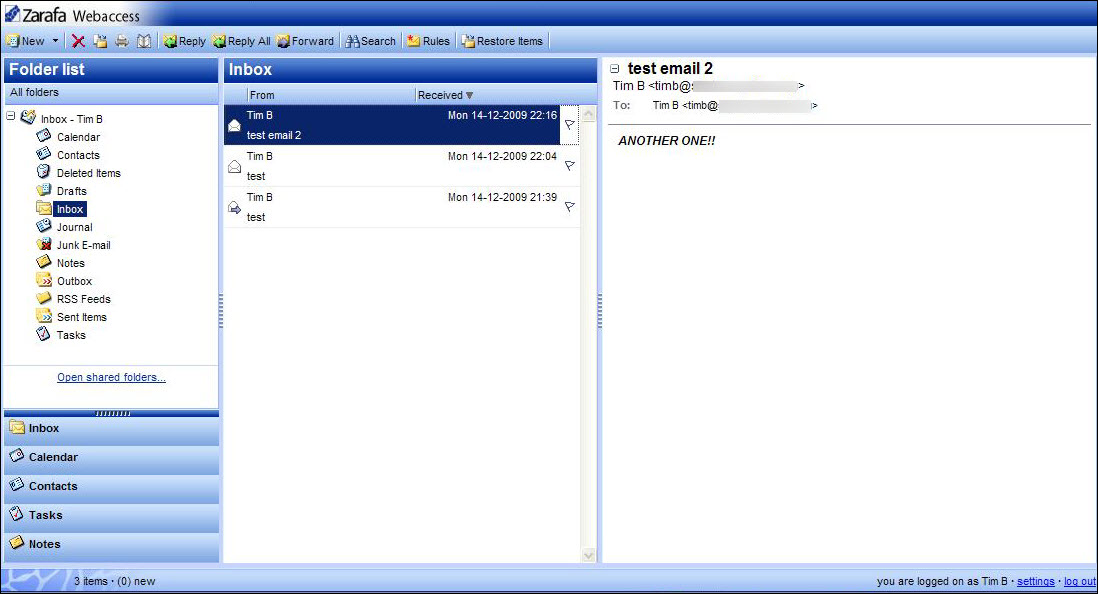
Zarafa is one such application, which can perform as an alternative to MS Exchange Server and allows sharing of data. It possesses its own email client known as WebAccess. It contains all data items such as tasks, appointments, and emails in MySQL database. In this discussion, we will illustrate the possible resolution and analysis about Zarafa Forensics to find the crime that was committed.
In-Depth Analysis for Zarafa Forensics
Considering the aspects of digital investigation involving data, firstly it is important to understand the structure of database on which there a need to perform analysis and implement methods to carry out the forensic investigation on Zarafa database.
Zarafa Server saves and manages all its data in an open MySQL database that consists of multiple records and tables. Records are of the data items like contacts, notes, mails, appointments, etc. A group of tables contains the information about the store records. The core targets during database forensics where there is probability of existence of some evidence persists, includes:
Properties: The properties table encloses all data item properties.
Hierarchy: Determines to correspond of the property with data item. It displays folders with respect to store.
LOB: Consists of all the attachments and contacts images
Users: Saves all groups and users
Usergroup_act: Saves all relations between users and groups
ACL: Store all the access rights
Outgoingqueue: Saves the link to message, which is made by server before sending it.
Database File: Zarafa uses various storage engines for the management and storage of data. Mainly, InnoDB is one of the popular storage engines, which is used by Zarafa server as it supports .frm and .ibdata file format to save data.
In addition, Zarafa supports various email applications such as MS Outlook, ActiveSync compatible PDAs, smartphones, WebAccess via Firefox, etc. By accessing these applications, it is used to save the contacts via client program. Zarafa offers proper management of database storage of contacts for Outlook, PDA, or Ajax based mail client users.
Obstacles in Zarafa Forensics: As discussed above that the entire user’s database is stored in form of tables on MySQL Server and it support to file format for data storage. However, if corruption occurs any of the two files, then it is difficult to access on the Zarafa database Server. Moreover, it also supports multiple database storage that creates a challenge in investigation and searching specific data within Zarafa db.
Alternatives for Zarafa Forensics
Challenges that have been discussed above can be resolved by using the third-party utility because they are programmed with options that make the investigation effortlessly executable with features like:
- No platform dependency
- Provides preview all data
- Offers defined search option
Out of which, one such utility is MailXaminer. This tool is an appropriate and simple way to analyze Zarafa database. It permits to export the identified artifacts to the required file formats such as EML, PST, HTML, PDF, Print, Tiff, HTML Reporter, etc. This tool has various features as mentioned.
Beyond this utility, there are various other ways of Zarafa database forensics by converting it to PST file format. As Outlook is, the most secure file format and one can perform investigation also. However, these methods are complicated and require much more time. As the time is important and investigation should proceed fast so, the platform of software is always helpful.
Observation
Zarafa forensics is mostly challenging for its dual roles of a client server and an email service over web. However, the understanding of its database along with its storage alone is enough to examine the activities carried out on the platform. Accordingly, using the third party tool is the most convenient way to perform the email forensics investigation as it saves user’s time and effort.

