Search on Unmounted EDB Files – How To
The most discussed topic among forensic experts, attorneys, investigators and e-discovery firms is how to perform search on unmounted EDB files and access e-mails to figure out possible evidence. So far, from Microsoft’s end, no such API has been released or suggested that can be considered as very well versed in carrying out the search action on unmounted Exchange Server’s EDB files. Traversing the dismounted Exchange database files can be a considerable option, but, it often proves to be a challenging task as shutting down of the Exchange Server can be really expensive and can also prove to be lossy. Also, shutting down of Exchange Server can be a bit finicky as it often serves as the backbone of the entire communication system within an organization’s network. With such never – ending issues, it becomes the most tiring and breath taking challenge for forensic investigators to traverse and search for evidence from the EDB files without preferring the option of dismounting them. But dismounting has been just an alternative nourished with hiccups.
Issues Faced In Analyzing The Unmounted Edb Files: –
- No Assistance from Microsoft: – No technical assistance from Microsoft via any service or API that may assist in sneaking within the unmounted EDB files.
- Insufficient Rights: – Often, the defined SeSecurityPrivilege rights restrict the investigators in gaining the complete access to the unmounted EDB files.
- Accidental modification in the transaction logs: – In no case, the antivirus programs that are safeguarding the Exchange Server, must traverse the transaction logs (as it often leads to crashing of the Exchange Server). Investigators, while intruding into the unmounted EDB files, may accidentally trigger the antivirus program to sneak in the transaction logs, thus, causing a disaster.
- Variation in the Exchange database structure: – The variation in the structure of EDB files, starting right from the version 2000, 2003 to current, often misguides the forensicators to look for the right evidence at the right place.
- Is ese.dll really a solution: – DLL has often been a choice of the investigators working in combined efforts with the developers to carve evidences from the unmounted Exchange database. But as per the postulates laid out in MSDN, no such support to the Exchange database has been verified.
As technology runs in our veins, we carve solution for every problem. Considering the above mentioned and many other issues, also, with a detailed R & D and pondering over the words and experiences of the experts, a tool was developed that may assist the Digital Forensic Investigators to perform detailed forensic analysis of the unmounted Exchange EDB files. The tool being “MailXaminer”.
Search Unmounted EDB Files with MailXaminer
The tool can be considered as the most trending and robust solution if you love messing with the Exchange Server database files, that too, in an unmounted state. This email forensic investigation tool is an output of the combined efforts of developers and email investigation experts to work on Exchange EDB and STM files. A perfect solution that answers your query, “How to analyze & search Exchange Server mailbox?”.
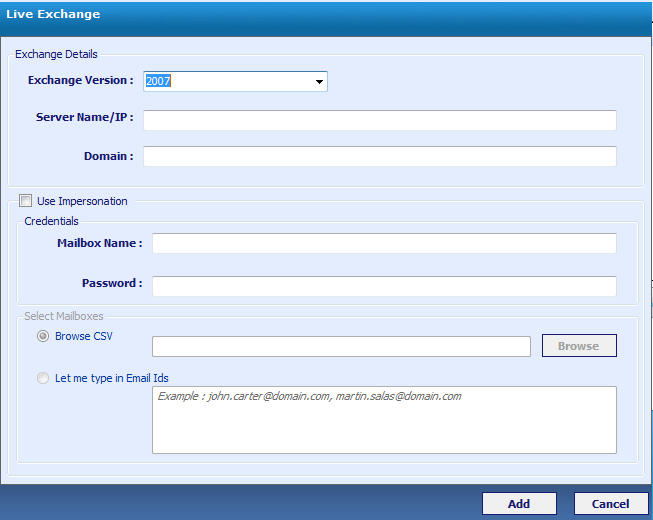
On the basis of investigative requirements, a very much focus has been laid down on product customization. To overcome the account authorship and other related issues, the software has also been delivered with an advanced feature of Impersonation.
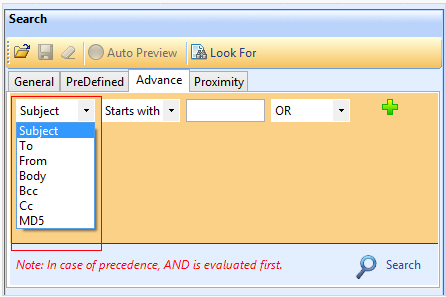
Investigators can find plenty of robust search algorithms integrated into the tool such as General, PreDefined, Advance and Proximity searches for comprehensive searching within the unmounted Exchange database.
Thus, with the available features, MailXaminer can be the most preferable tool to search for evidence and other related artifacts within the Exchange EDB database. Perform detailed investigation without dismounting the Exchange EDB file.