Rackspace Cloud Sites Analysis
Rackspace sites are a platform-as-a-service proffering which are similar to the traditional web hosting services. The only difference is that the Rackspace cloud services are built on hardware infrastructure whose potential can be increased with a growth in its consumers. The users are given an access to this service on the basis of a monthly payment. This allows the users to have computer and storage resources. Subsequent to exhaustion of the allocated resources, extra charges are applied.
Rackspace, being a web-hosting service, gives the provision of using own domain names to its users and during Rackspace email forensics this domain name assists experts to perform in-depth investigation on users’ mailbox. The users can synchronize their Outlook or Mac Mail account with their Rackspace account.
Introduced in the year 2007, it offers a mailbox storage capacity of 25 GB to its users. The users can send attachments with their emails and the size of the attachments should not be exceeded above 50 MB. It supports both IMAP and POP. The cryptographic protocol supported by the client is SSL and it supports around 12 languages.
Necessity Of Rackspace Email Forensics
With the count of cyber-crimes reaching its peak, forensicators leave no stone unturned when it comes to investigation of suspect data. The investigation of each and every data chunk in relation with the suspect is the first priority of the investigators. Hence, the analysis of Rackspace data is an obvious step in case the suspect has been using Rackspace for hosting his account.
Rackspace mail analysis can be done only when the users have access to the Admin user credentials. While conducting Rackspace mailbox investigation, if the credentials are available, scrutinizing the suspect account is a very easy task. However, not every organization gives the investigators, the authority to access their Admin account in order to save the organization workflow from being hampered. Thus, in such a case accessing Rackspace data can turn out to be a big challenge for the investigators.
An Apt Solution For Getting Access To Rackspace Data
As mentioned in the above section, during Rackspace email forensics not every organization may provide its admin credentials to the investigators, in can become an impossible to carry on with the investigation process.
However, deployment of professional forensic tools like MailXaminer can enable the investigators to perform Rackspace mail analysis and access both Admin and the associated user accounts without hampering the workflow of the organization and without posing a threat to crucial data. This is due to the fact that this tool does not pose chances of accidental deletion or hampering of Rackspace data, as compared to the manual analysis of the data.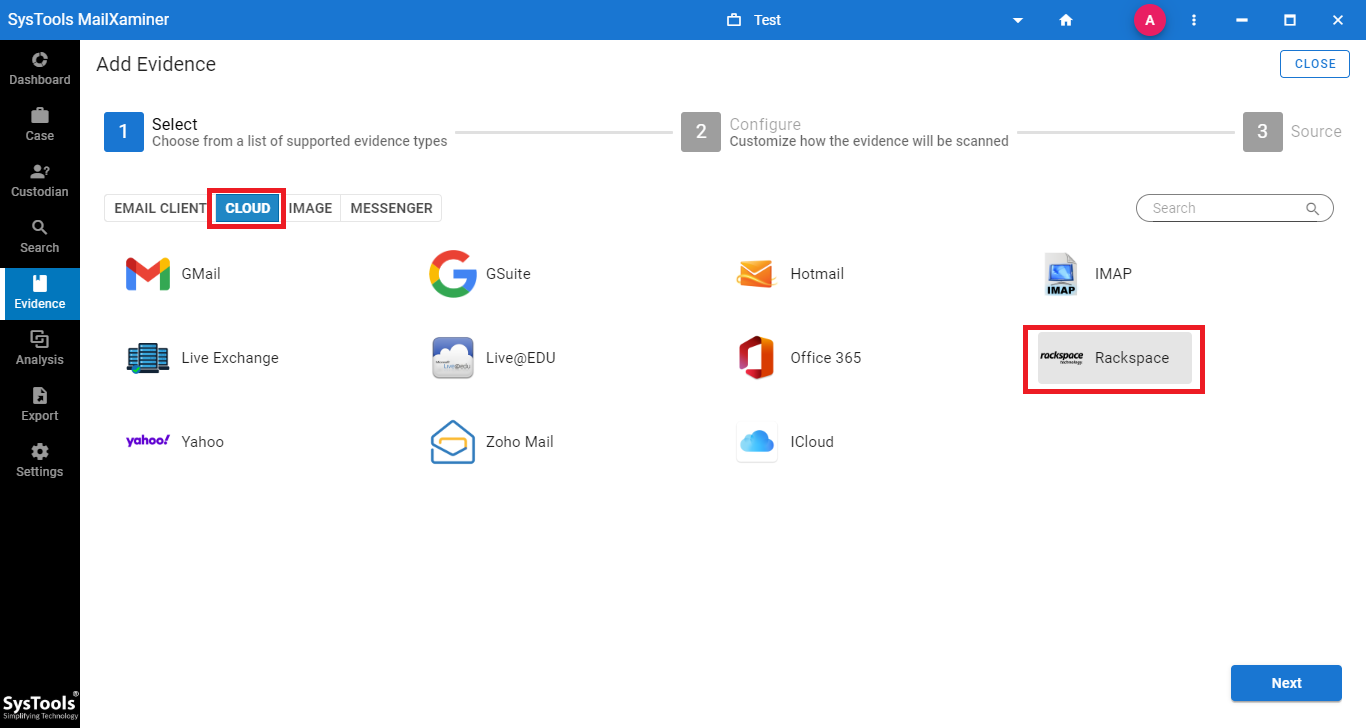 For its working, the investigators need to provide admin credentials to the software in order to scan the Admin as well as the suspect account data. The suspect account details should be stored in a CSV file and when the file is selected, the software enlists the data associated with the account.
For its working, the investigators need to provide admin credentials to the software in order to scan the Admin as well as the suspect account data. The suspect account details should be stored in a CSV file and when the file is selected, the software enlists the data associated with the account.
In case the investigators want to narrow their Rackspace mailbox investigation and are want to examine data shared on a particular date, the Date Filter option proves to be a good option for them.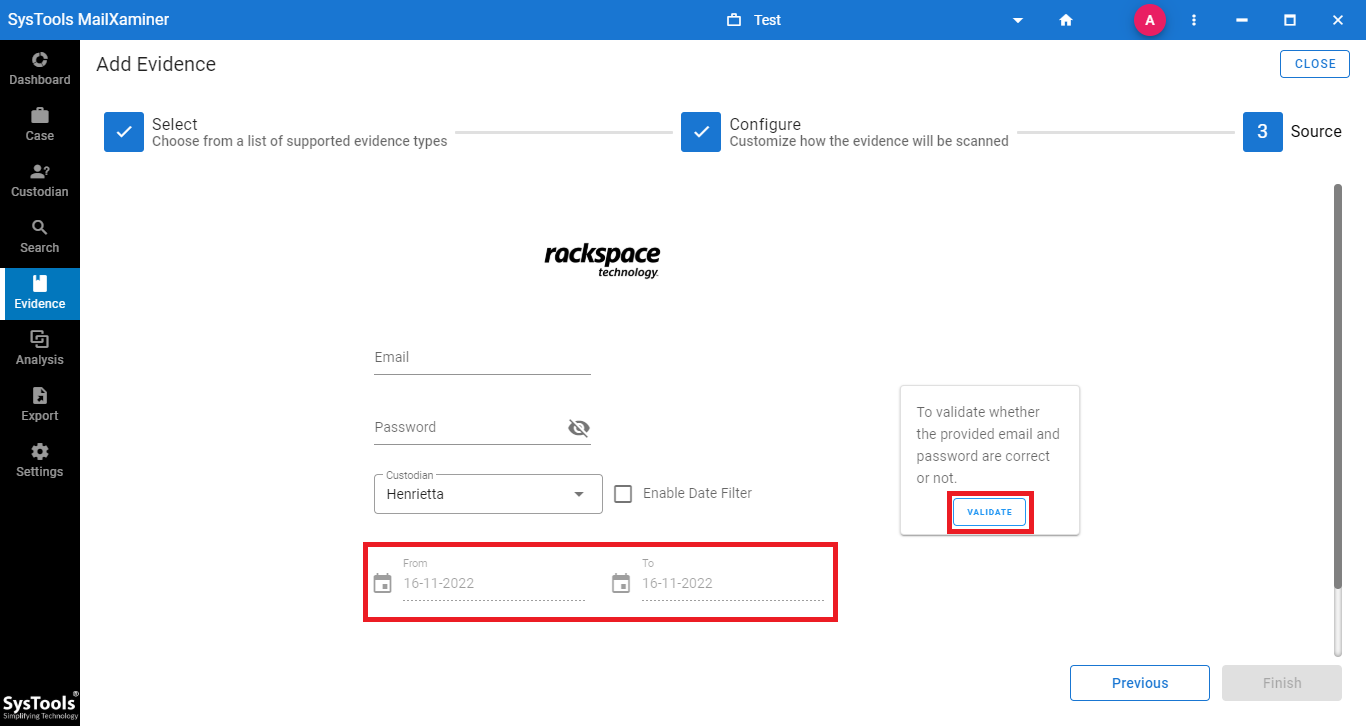 Performing Rackspace email forensics can be made both easy and quick with the help of this Digital Forensics Tool. Not only the software enables the investigators to access the suspect account but also enables to narrow the search process, thus saving the overall investigation time.
Performing Rackspace email forensics can be made both easy and quick with the help of this Digital Forensics Tool. Not only the software enables the investigators to access the suspect account but also enables to narrow the search process, thus saving the overall investigation time.

