Mailbird Forensics for Finding Evidences in Email
Mailbird is a desktop-based email client, which allows users to access emails besides connecting with various social networking sites. This includes Facebook, Google Plus, WhatsApp, etc. The first version of Mailbird was released for the public on January 27, 2014. It has been awarded as the best free email application for Windows OS in 2014 & 2015 by IT World. It incorporates countless advanced features such as Email Snooze, Video Meetings, Speed Readers, connectivity with social networks, and much more.
One can easily make the best use of their social network’s contacts for instant communication with the end-users. It is designed with a user-friendly interface with the ability to connect with any email server.
Mailbird Forensics Examination
The latest version 2.8.4.0 of Mailbird has been released on April 14, 2020. It provides numerous features, which can be utilized by both small-scale and large-scale organizations. With its remarkable features such as options for attachment search, LinkedIn lookup, multilingual support, etc. has encouraged users to adopt this application. As a result, many users are migrating to Mailbird from their default email applications like Outlook and Mozilla Thunderbird.
With the increasing users of Mailbird, the possibilities of targeted cyber-crimes have also been increased. Therefore, there comes a need to investigate the Mailbird email client to examine the occurred cybercrime. However, the question that arises is how to get access to Mailbird emails, which is stored in local computer. It is an important factor to find the stored emails and email folders to produce evidence against a suspect. All these things can be achieved only when each evidence is correct and in an orderly format. In the upcoming section, we will focus on how to analyze evidence in the Mailbird email client.
How to Analyze Mailbird Email Client?
It is quite difficult to find the potential evidence from the email applications which store the data in its respective file format. There are different ways to navigate the evidential information from the local computer. Moreover, every forensic tool has the functionality to seamlessly search the evidential data. However, it also imposes certain downsides in terms of performing the search operation. To be more precise, there are tools that only support searching text data. Whereas, there is email forensic software which can search both texts as well as images. Additionally, there are tools that are capable of searching text, image, and videos while gathering the artifact.
Now, to search for evidence from the Mailbird, it is necessary to know the email’s storage location in the local system. The Mailbird can easily support multiple email applications such as Gmail, Hotmail, Yahoo, Thunderbird, etc. As a result, the email examination of Mailbird can be achieved corresponding to the email applications used. Moreover, it is important for the forensic investigator to know the location of the Mailbird’s user data. This is because it stores all the emails and other data items in the user data location. Besides this, it creates a separate storage folder for each user who is accessing the Mailbird on a single machine.
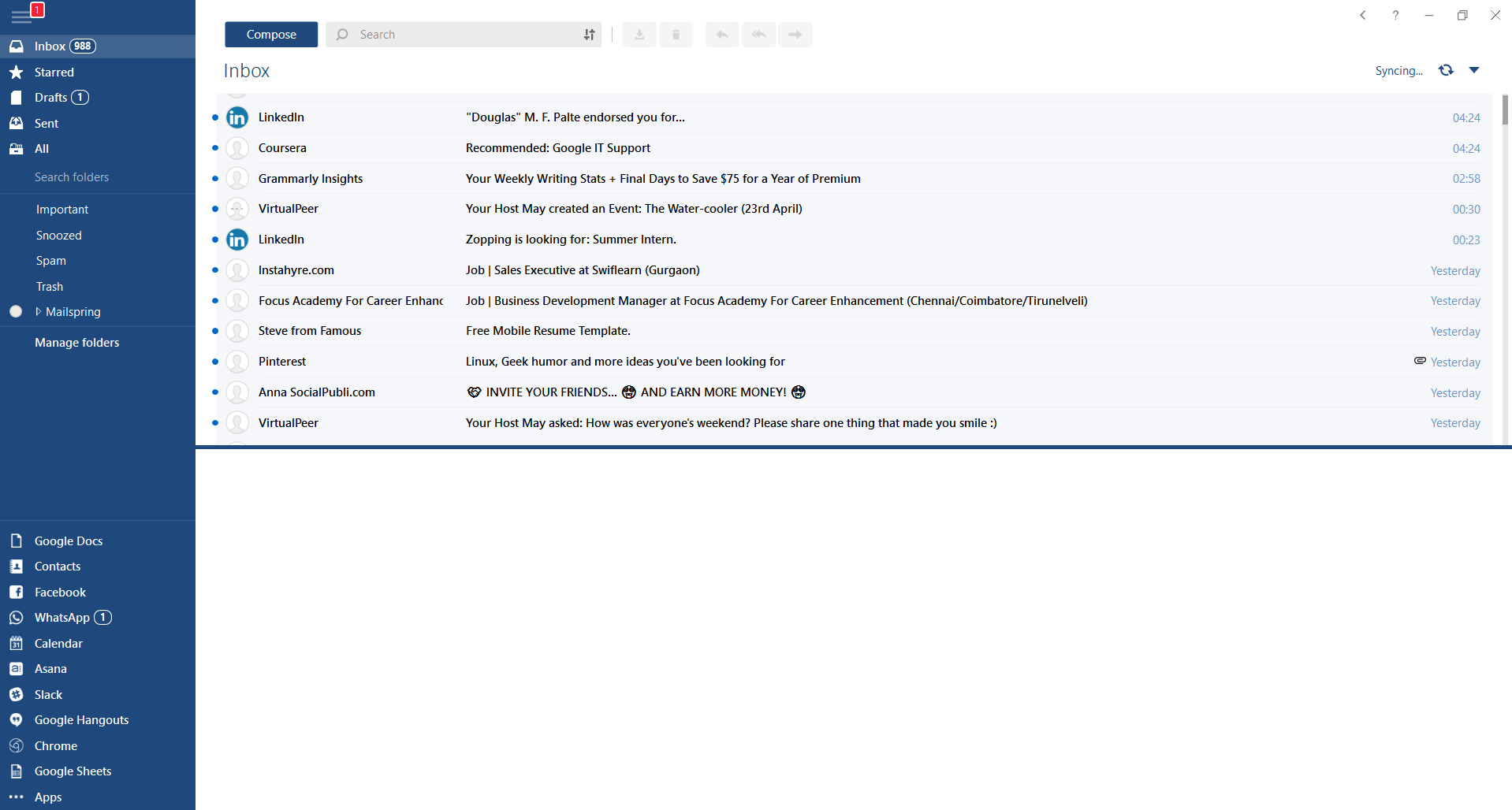
Below given is the image which specifies the user data location in the Mailbird email application. Within the Mailbird folder, there are three different folders and three files. While searching for information in mailbox user data, it is important to search the Store folder. It is the folder where actual data is being stored.
From the above-given image, we can see that there are two different folders A, MessageIndex, and three different files. During the investigation purpose, the main focus must be given to Store.db file. All attachments are stored in A folder, email headers are stored in the MessageIndex folder and Store.db file stores all text messages. If a forensic investigator wants to take data from any machine to access it in their own machine using Mailbird. Then, they will copy the Mailbird folder completely and paste it at the same location in their machine. This will enable them to access the data and to search the artifact.
What is the Problem While Copying Mailbird User Account Data?
As we have discussed that all user data is saved within the mailbox folder. However, inside the mailbox folder, each of its parts is separated and present in different folders. Therefore, it is not a good idea to just copy and paste the Mailbird folder to access all data in other machines for Mailbird forensic examination. This is because there is a probability of user data corruption while copying the data. Therefore, it is recommended to save the Mailbird folder in TGZ format, which is also called Tar Zipped format. After that, copy and paste the .tgz folder before initiating the investigation process.
Concluding Thoughts
With the increasing use of Mailbird application among both personal and business users, cases of Mailbird cybercrime has also drastically increased. To smartly investigate the Mailbird email client, the user data must be saved in the .tgz file format. This helps in avoiding the corruption of user data files. Also, the investigation should be implemented using a reliable third-party tool. For that, MailXaminer is the best-recommended Email Analysis Tool providing versatile features to easily meet up forensic investigation challenges for Mailbird application.

