DD File Forensics: Fetch the Evidence From Image File
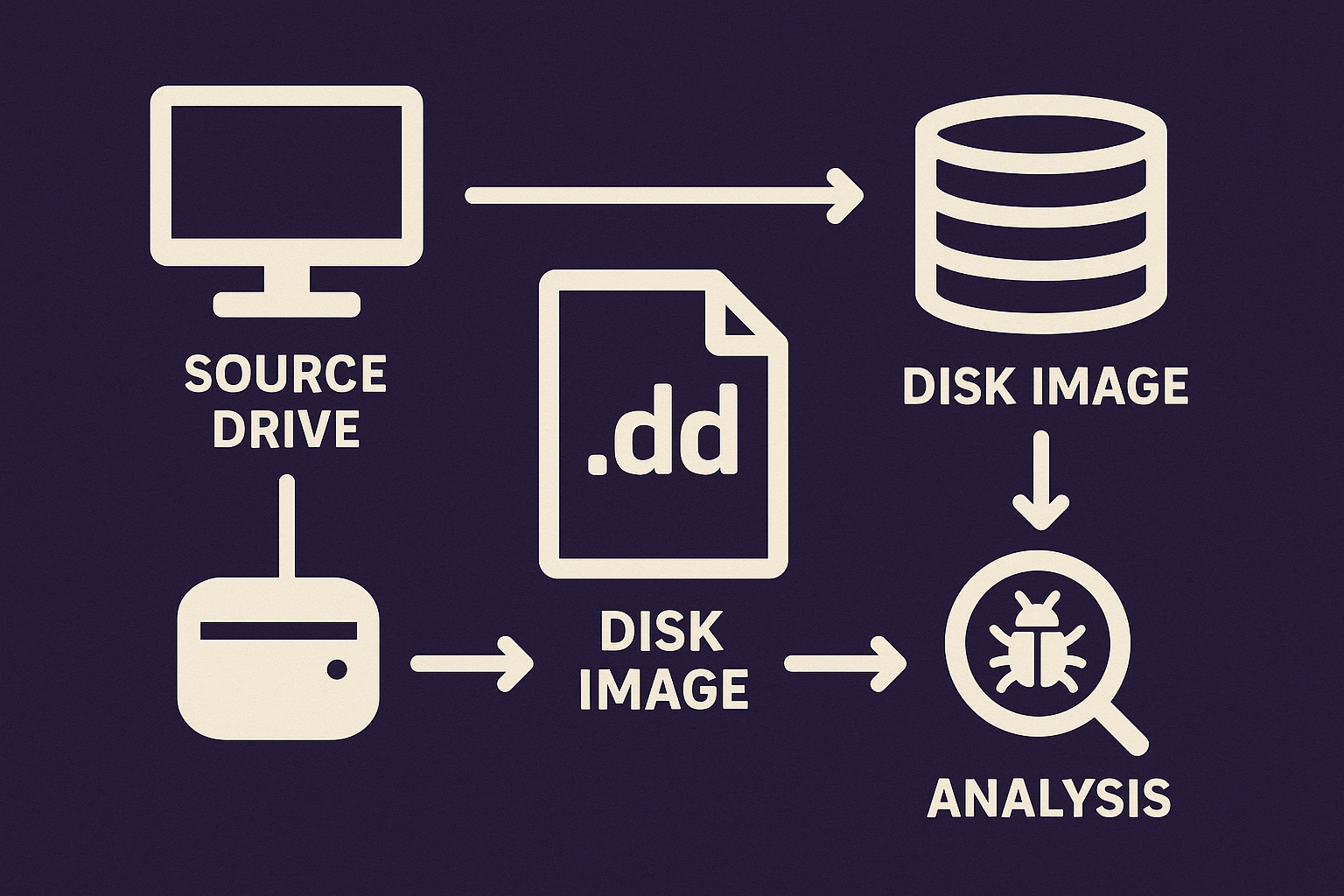
DD file forensics involves analyzing disk image files that you create using the dd command on Unix or Linux systems. These files use the .dd file extension. They store a bit-by-bit copy of the storage device, and forensic investigators use them to extract, analyze, and preserve digital evidence.
Table of Contents
- Need and Use of .dd Extension Files
- How to Analyze a DD Image File for Forensics Quickly
- Efficient Platform to Investigate DD Files
- Analyzing .dd File Artifacts Using This Smart Way
- Preview Email Files and Attachments Present in the DD File
- DD Image File Forensic – Shows All Files Present
- DD File Forensics – Export Options
- Conclusion
- Frequently Asked Questions
So, the first question would be what is a .dd file?
The answer is that a DD file is an image file created using .dd commands. It is a powerful and simple command-line tool used to create disk images, copy files, and other files from hard drives on Unix or Linux Operating Systems.
The syntax for creating a DD file with the command is:
dd if=”source” of=”destination”
The utility is inbuilt and installed in Linux or Unix OS to create raw images for forensic image analysis of drives, folders, files, etc. Users can create the output file either in .img or .dd file or other file formats by specifying the file type at the “of” part.
Windows users can also run the command using the “Cygwin” framework or the MKS Toolkit to create the disk image. Cygwin gives the same interface as that of the command line in Linux or Unix, which enables Windows users to work on it. If you set the destination as .dd, the tool will create a .dd image file as the Output. But be careful if you accidentally swap the source and destination, the destination will overwrite your source data.
Need and Use of .dd File Extension
People generally keep disk image files to verify the data in the future, to check for any manipulations or alterations in the data. In digital forensics, many of the forensic examiners depend on .dd file forensics, since it sometimes reveals the roots for their investigation.
However, when it comes to opening the file to view the structure, things get complicated. The need for a perfect platform to view and analyze .dd image file forensics is always challenging. Without a proper platform, working on these files is a threat. But this challenge has been resolved now with a tool that is discussed in the article, the third-party software. This advanced forensic application is an appropriate and simple solution to view and examine .dd file content.
How to Analyze a DD Image File for Forensics Quickly
To analyze DD files, follow these steps:
- Set up MailXaminer and select “Add File”.
- Choose the “Image” tab and browse for the .dd file.
- Configure scan settings and start scanning.
- Preview data and export evidence as needed.
To know the deep functioning of the software, refer to the next section, which describes the software in detail.
Efficient Platform to Investigate DD Files
You can try many methods beyond software to view a file’s content, but they are complicated and take a lot of time. Forensics software always helps to proceed investigation fast and efficiently.
The best email analysis software can help to examine DD file format data. Through this software, forensics examiners can analyze and investigate files with advanced functionalities to find digital footprint.
So, let’s further discuss some major features of software that help in DD image file forensics.
Analyzing .dd File Artifacts Using an Advanced Way
The application enables users to analyze and collect the digital footprint without tampering with the data content. You can view the file content, search for the data, and do more, all within a few minutes. To examine the file, all you need to do is, just add the file into the software for scanning.
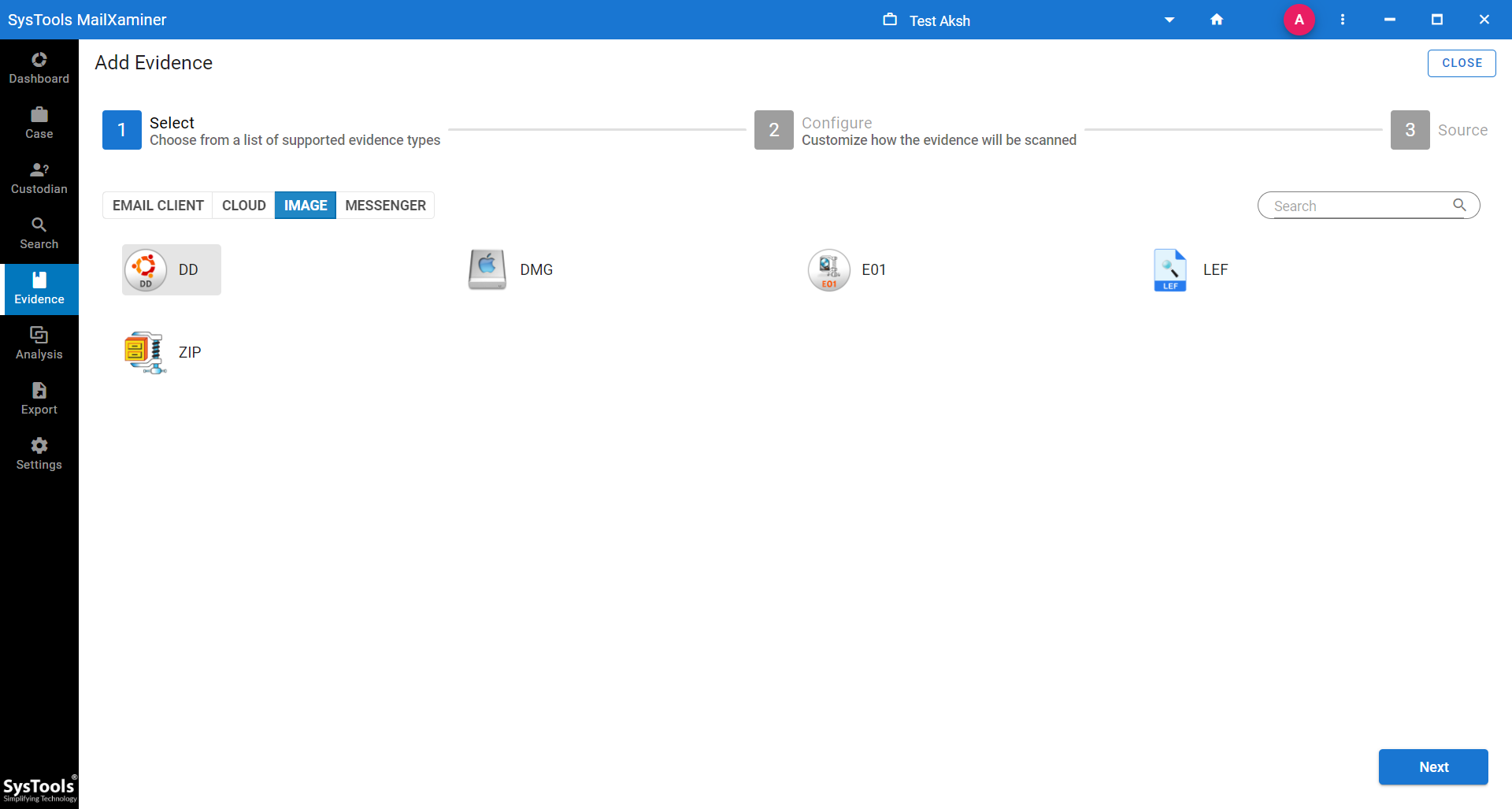
- In the “Add File” window, select the “Image” tab and choose the DD file format. Later, browse the location of the file on the system to view and examine it
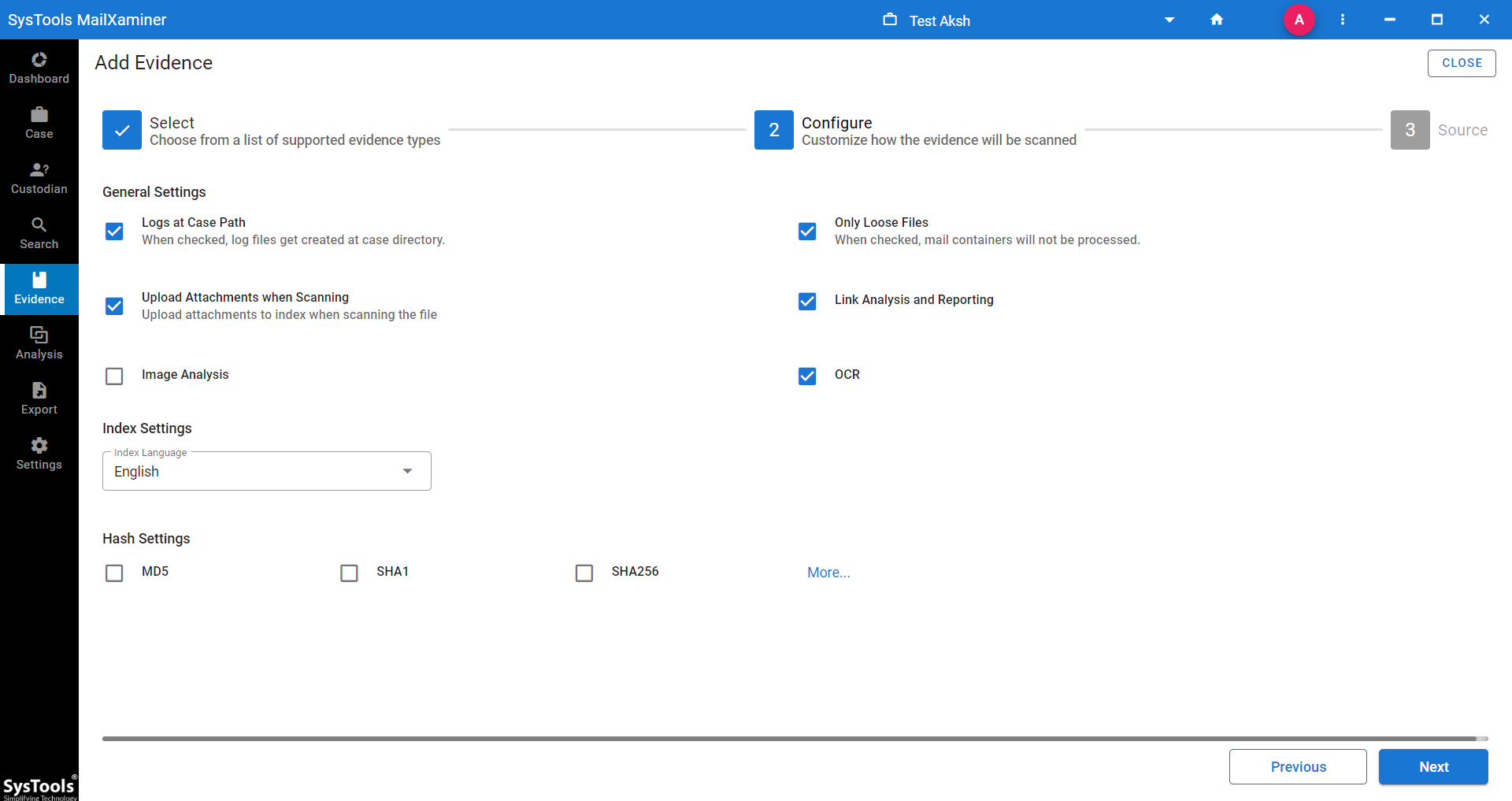
- Before clicking on the “Add” button, just set the “Scan Settings”. Then, save the setting by clicking on the “NEXT” button
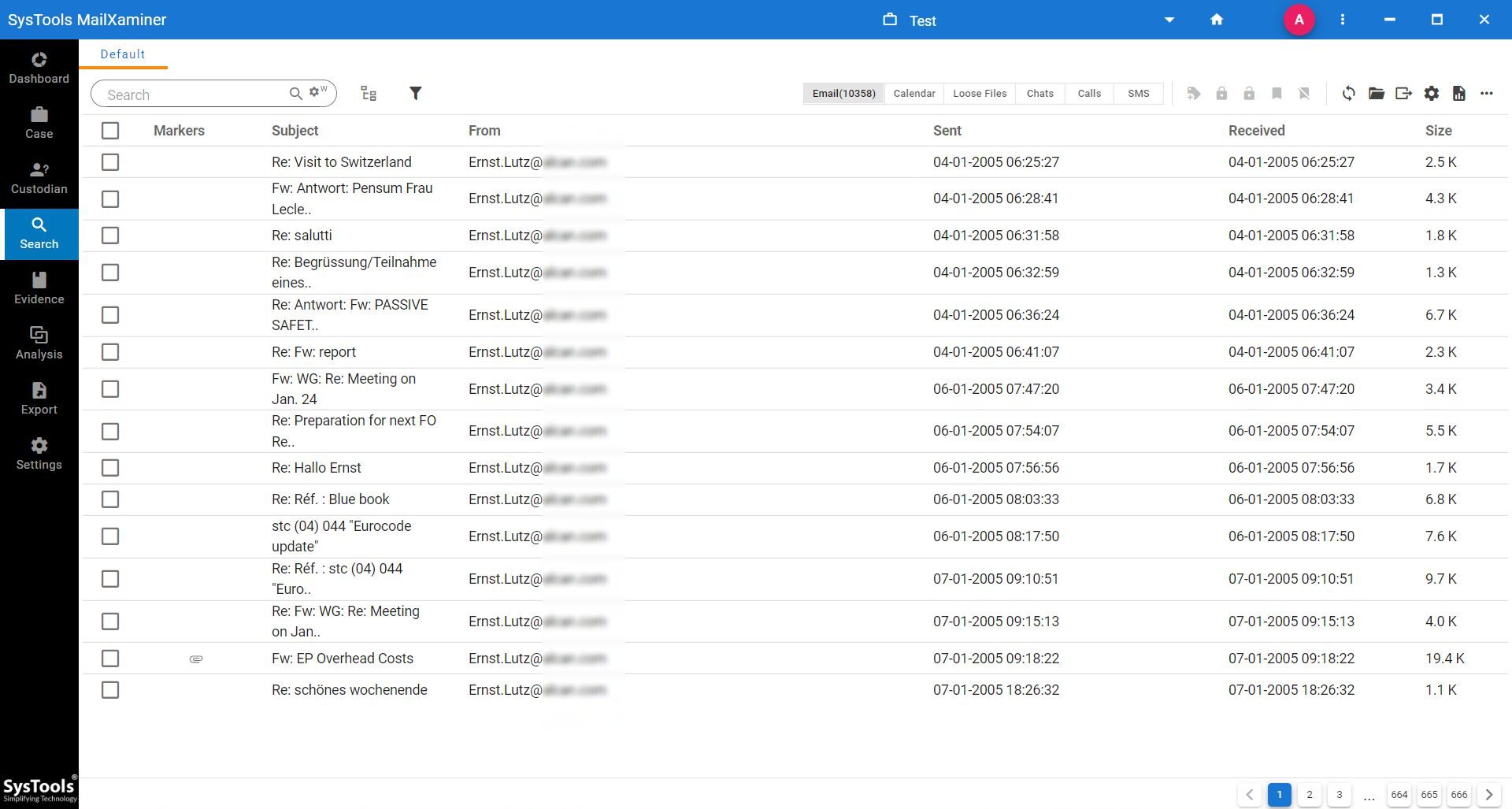
- Once the Scanning Process is completed, the user will get a preview of all the files on the screen in hierarchical order.
Preview Email Files and Attachments Present in the DD File
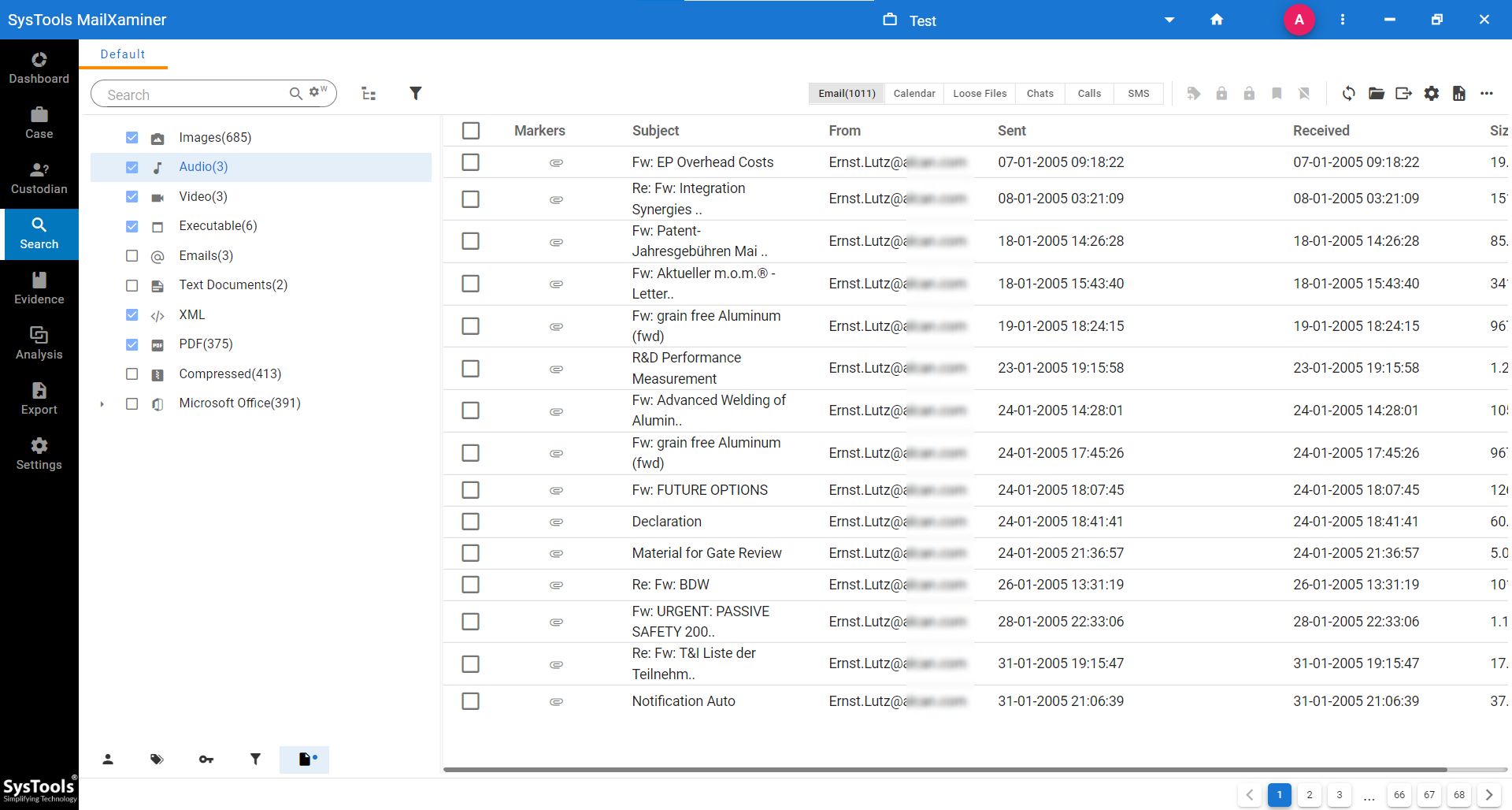
- To investigate email data contained in PST, the user can choose the corresponding PST file from the list. The “Email” tab will show all the emails listed in the selected folder
DD Image File Forensic – Shows All Files Present
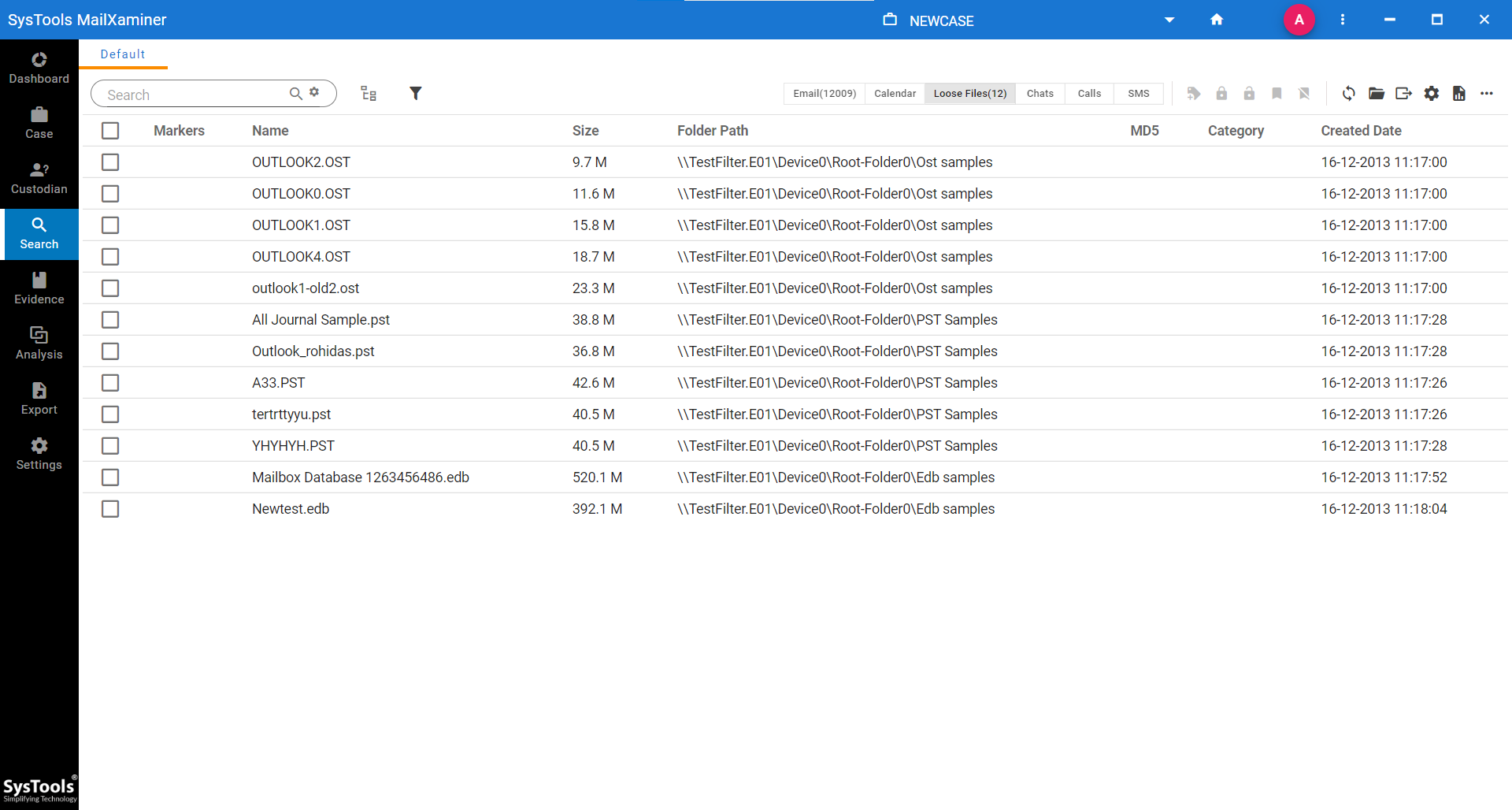
Apart from previewing the email contents, users can get an overall document list contained in the file.
DD File Forensics – Export Options
Evidence is an important loophole to win the case so, securing them is very important. The application enables users to export identified artifacts in multiple file formats. Users can save the data in any of the various file formats, such as EML / MSG / PDF / PST / HTML / CSV / HTML Reporter at desired location.
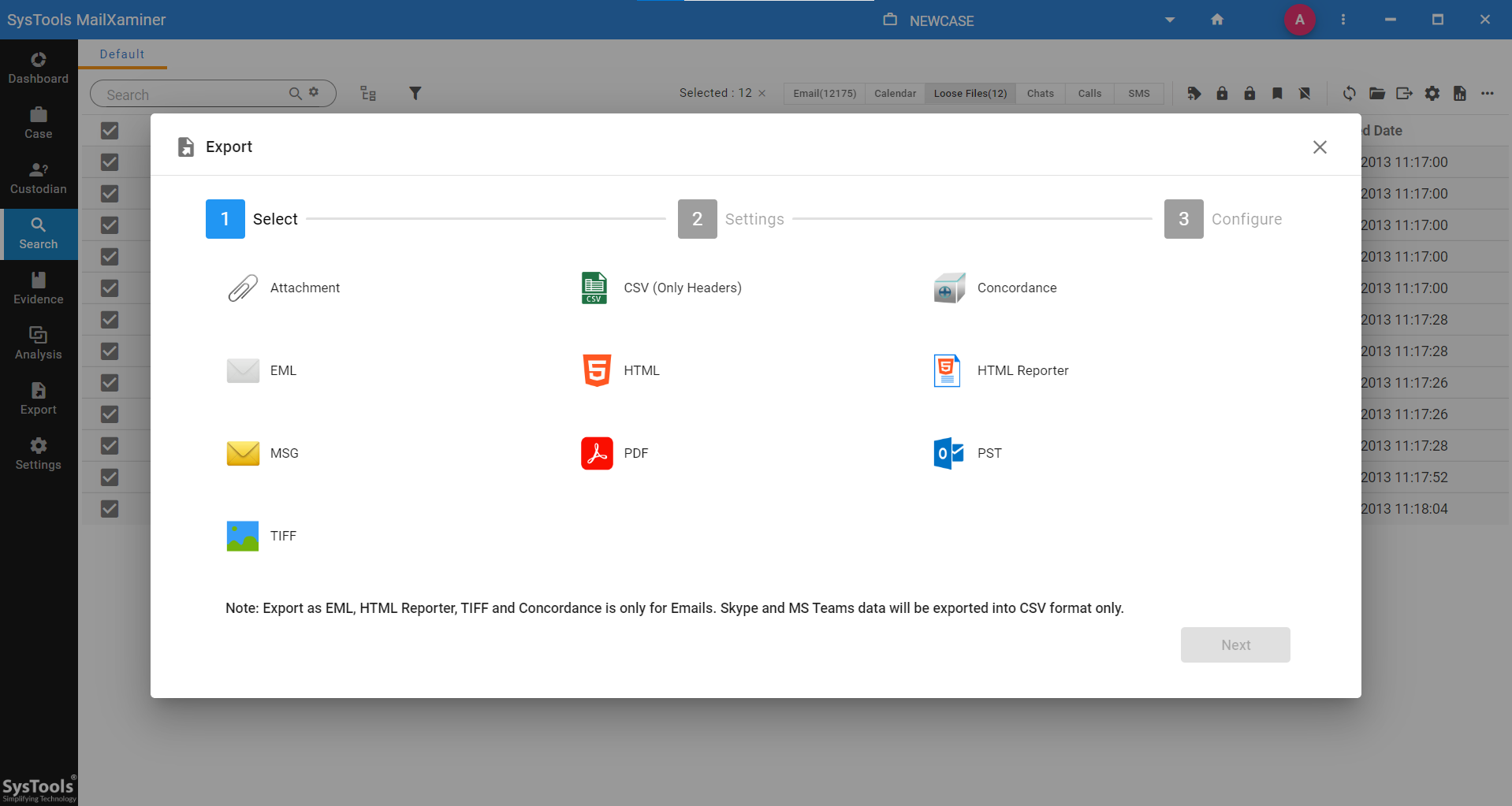
NOTE: PDF file format has recognized the efficient format since it is non-editable. Hence, the court of law prefers to accept the evidentiary documents in PDF file format. For detail PDF file analysis or to submit the evidence in the court in PDF file, the user can export the evidence report file to PDF.
Conclusion
The tool discussed in the article is an efficient and effective software for examining .dd files. While carrying out .dd file forensics, users can collect all the data from the file without any loss of information. This email forensics software will help to view all the data files and documents within the DD file.
Frequently Asked Questions
Q. What are DD files in digital forensics?
A DD file is a raw disk file that is created using Unix/Linux dd commands. This file captures every bit of data from a storage device. DD image file Forensic is a practice wisely used in different digital forensic investigation techniques.
Q. Which tool is used to open a DD file?
Digital forensic investigators consider DD image files important evidence. You can open them with any forensic tool that supports disk images. To open DD files for forensics investigations, you can opt for the Digital Evidence Analysis Tool. It provides you with advanced features to view emails, attachments, and file structures within DD images.
Q. Can I open DD files on Windows?
Yes, DD files can be opened in Windows using the DD forensic tool. With the help of this software, you can add DD files as evidence. This software can analyze the files as evidence without altering the original data.

