Spotlight On The Communigate Server
What is Communigate Server?
It is an Email Server platform, which comes with N number of advanced features for emailing, instant messaging, calendar sharing, voice and video calling, screen sharing, file sharing, etc. The inbuilt integrated functions makes it all possible to be carried out. This server platform is compatible with several operating systems, including popular ones like; Windows and Linux.
Communigate Email Server (CGP), is counted amongst the most preferable email server options to handle distributed data in a centralized manner. If you are running an organization, then choosing an appropriate server to organize data is very important.
Communigate Email Server Forensics: The Need
Having your own email server, like the Communigate; helps to centralize data, create an atmosphere to establish connection among server’s client, and provide distinctive security for the database particularly. Here, the term security stands for prevention of email server and its data from cyber crime. However, in case of any such events, identifying / examining the root cause behind these is required to be done. This helps to ensure whether its about the mapping data connection or investigating data storage.
Obviously, if you encounter any kind of data manipulation, then a forensic investigator has to be hired in order to troubleshoot the methodology followed to commit the email crime. But, things can be changed. You can become the email server investigator that you are looking for by understanding the fundamental terminology of Communigate email server or examining Communigate email server profoundly.
This tutorial contains major terms in respect of the Communigate mail server, helpful for a novice as well as a cyber crime investigator.
Let’s bring Communigate server and its unknown facts under the limelight.
Which Protocols Are Supported?
Everyone is familiar that transmission of emails within a network only becomes possible with the help of protocols (which is also known as a Mail Transfer Agent – MTA). Basically, we have heard about POP3, SMTP, & IMAP as the common bus which makes the exchange of emails possible over a network to client machine & vice-versa. And yes, Communigate also supports these protocols with which an admin can create personalized webmail interface for a group of users. Apart from the type of protocols, this exchange server platform also uses major encryptions to transport emails which includes SSL and TLS:
SSL: Secure Sockets Layer
TLS: Transport Layer Security
Notes: This server platform has its own integrated scanning program.
Encryptions and integrated scanning programs are more than enough to assure the security of Communigate Mail Server and its data. However, there are still some factors which can impact and break down the data security.
The need of Coummunigate Email Server Forensic gets evoked against these factors where things become more complicated.
How Coummunigate Works?
To simplify how actually Coummunigate works, we will create an account for an alias client by using the admin control panel on Coumminagate server. And then we will start exploring the data, file types, and different schemas which the server enforces to save client data on the server machine.
Creating an Email Account:
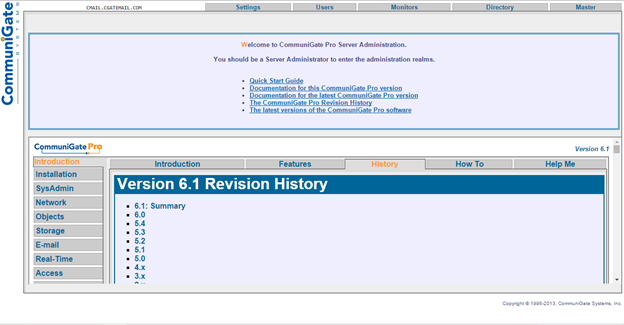
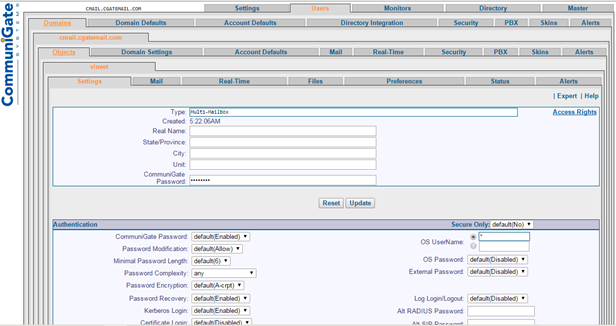
1.) Open the Communigate email server Admin Panel by using the web server path on the address bar.
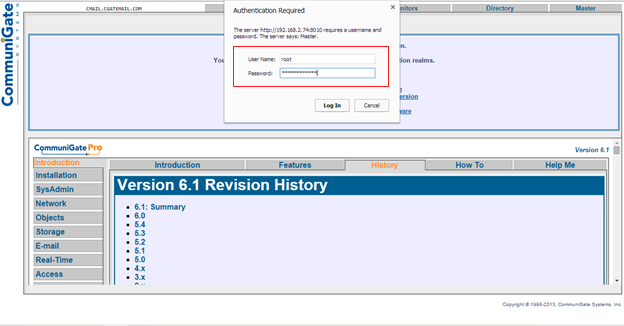
2.) Click on “Users” button located on top of the menu bar to which the browser will prompt a screen for admin login credential input.
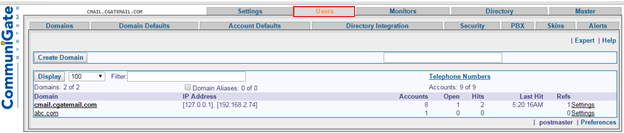
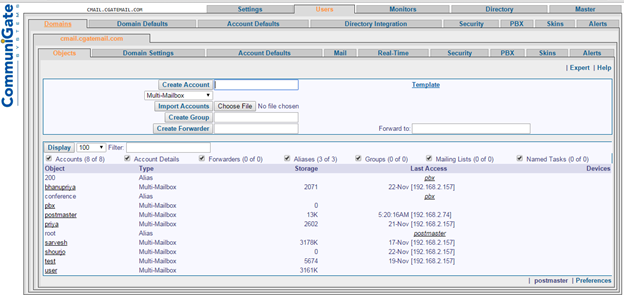
3.) Now, you have successfully logged into the Admin Panel. Choose a domain from the domain list and double click on it to move further.
4.) Type a desired name in the “Create Account” field provided.
5.) In this step, input all required details regarding the email account such as; type, real name, state, city, and most importantly – a password for the account. Finally, click on “Update” button to implement these settings.
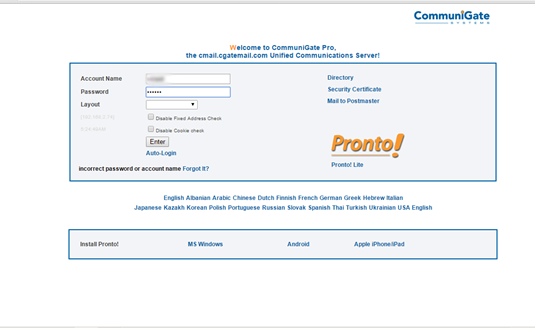
6.) Now, type web server address path in the web browser to log in. Input the defined login credentials now.
7.) Now, you have logged into the user’s web mail account.
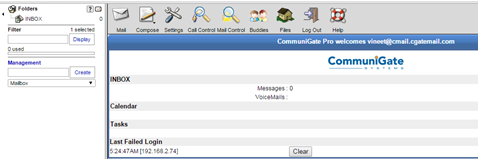
8.) Create an email (dummy email) and type it in the “To” field. Click on “Send” button.

Where Is The Server Data Being Stored?
The most important part of this blog is to elaborate the data storing schema of Coummnigate server and performing investigation upon Communigate Email Server and its entire database. Like a desktop based email client (e.g. Microsoft Outlook), Communigate also saves its data within a store location. But, things are different here and more complicated in comparison to the data storage method of Microsoft Outlook, and other email servers.
The last section of this blog has explicitly defined the working of email at a basic level.
Email Storage Location for Communigate Mail Server:
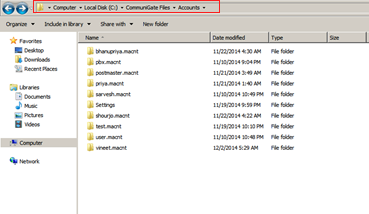
C://Communigate Files//Accounts//Users
Communigate server does not make any changes to the root folder hierarchy of the OS. And creates its own folder structure in the drive where it is used to save. As you can see, this server specifically builds a folder storage area for each of its account created using the email server admin.
Communigate Email Server Forensic: The Final Step
Perform a deeper analysis on these files. As we are familiar with the fact that Communigate server stores data in its own folder structure, the next step is to determine how this server divides the sub-folder (inbox, sent, draft, trash, etc.) of web email account.
Suppose, if user X has created an email account recently, then the machine (where the data of communigate is getting stored) will create a folder named X, within the accounts folder and will start saving the sub-folders of that account in it. Folder for each user account is created with “.macnt” extension and when you open each of the user’s folder, you will find a file for each sub-folder with “.mbox” extension.
E.g.
Inbox.mbox
Sent.mbox
Draft.mbox
Trash.mbox
How To Make Sure?
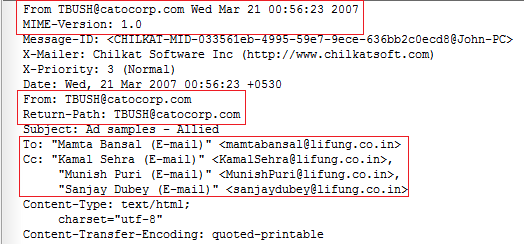
This file format has its own quality which is; it maintains all the emails in a text file by series (1,2,3….to N). To read an MBOX file, open it using a text editor so you could dig out the core details from its header section like; sender, receiver, time, etc.
Number of email based crimes or deceptions, like email spoofing; is done by manipulating these header details. However, it is a much complicated task for a novice user to bring them out in the limelight and study it. But, using MBOX Viewer makes things simpler for all types of users.


