What is Cloud Forensics? A Clear Guide for Modern Digital Investigators
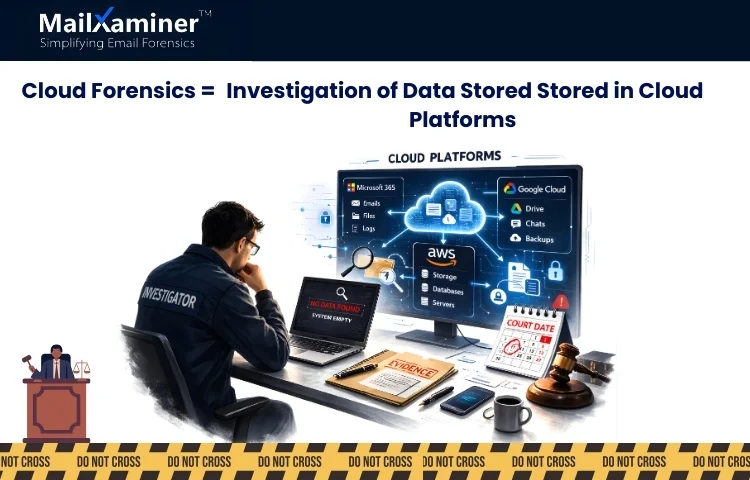
Imagine a situation where an investigator opens a suspect’s laptop. Finds there are nothing no files, emails, or logs. But the real evidence is not missing; it is sitting inside Microsoft 365, Google Cloud, and on other cloud platforms. Evidence needs to be found out as the court date is near. Now the question is, what is Cloud Forensics, and how can an investigator collect evidence from the cloud without tampering with data. In simple terms, it’s a branch of digital forensics that focuses on the examination of data stored and processed in cloud computing environments. Cloud-based forensics has become an essential tool for cybersecurity experts and law enforcement alike. In this blog, we will find it how to perform cloud forensics.
Why Cloud Forensics Matters Today
As we know, what is cloud-based forensics? It is the process of collecting, preserving, analysing, and presenting evidence stored in the cloud platforms. In this process, investigators have to research data stored in Cloud platforms like AWS, Microsoft Azure, or Google Cloud.
To make it clearer, it can be thought of with an example. Traditional forensics is like searching a single house. Cloud forensics is searching and analysing storage lockers spread across different cities without physically visiting them. Around the globe, many enterprises now use cloud services. This means frauds, insider threats, and cybercrimes now leave fingerprints inside cloud accounts.
Court evidence has to follow strict legal procedures. If the process is flawed. Evidence will be rejected in court.
Key Objectives of Cloud Forensics
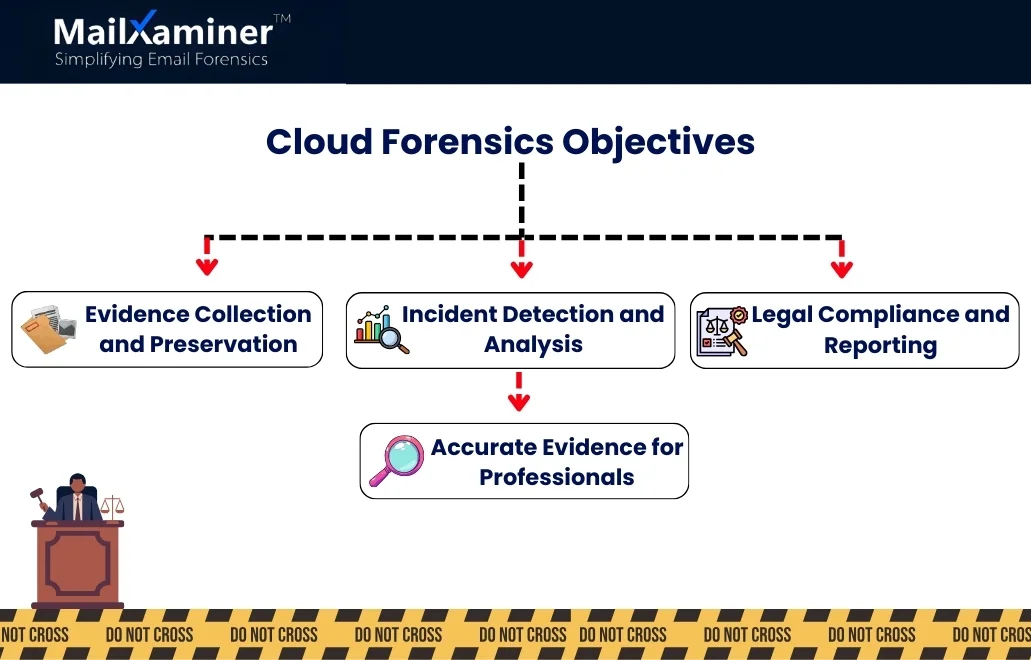
Once we understand what is Cloud Forensics. It becomes important to understand the key objectives of cloud forensics. The major objective is to
- Collect evidence
- Preserve it as per the legal compliance
- Reporting.
The Biggest Problem Investigators Face
The major concern is not just to find data but to collect it in a correct process.
As Cloud data is.
- Distributed across different servers.
- Stored in multi-tenant environments
- Protected by different provider agreements.
- In Cloud computing, data is stored in multiple machines in different geographic locations. If the data is deleted, then it becomes a challenging task to recover the deleted data, identify its owner, and make use of the data for the event reconstruction.
- Fragmented data and artefacts are present whose metadata has been altered.
Cloud evidence has to be handled with a lot of care. Many investigators do not understand how fragile the cloud evidence is.
- One improper download can alter timestamps.
- One missed log can break the timeline.
Now we know how cloud forensics is different from traditional digital forensics. Let’s have a look at why the traditional methods fail.
Why Traditional Methods Fail in the Cloud
Traditional forensics works by imaging a physical hard drive and other data storage equipment. But in a cloud forensic environment, there are no physical drives to seize. Cloud forensics requires some sort of specific tools and knowledge to extract the data remotely.
That means the investigator needs to work within the confines of cloud provider agreements, data encryption, and sometimes even international law to gather various information, such as PII data. The complexity of cloud forensics tools comes from handling multi-tenant environments and encrypted data. This adds an extra layer of difficulty.
Manual logins and simple exports can collect data. But they do not always preserve the integrity of metadata. Understanding what is cloud-based forensics means understanding that preservation is more important than collection.
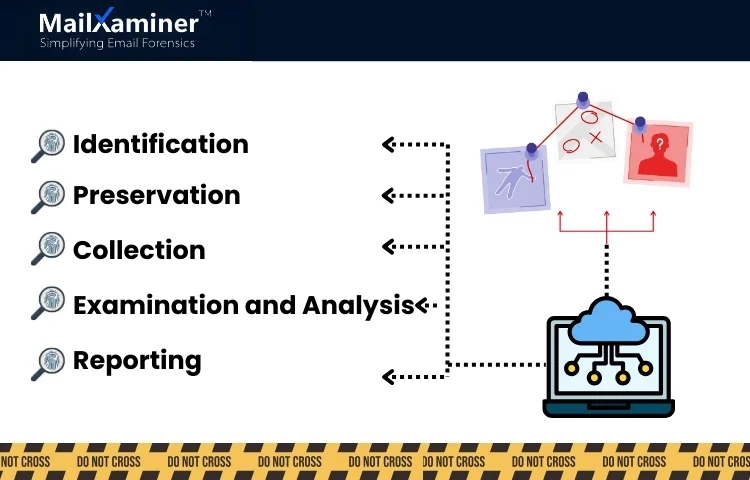
How Cloud Forensics Actually Works (Step-by-Step)
Once we understand what is Cloud forensics. We should know how it is performed. Cloud forensics is not about randomly downloading emails and data from the cloud. It follows the structured process to protect the evidence. It works in five simple phases:
Step 1 – Identification – Finding where the data to be investigated is. Microsoft 365, Google Workspace, AWS storage. Without proper identification, nothing can be done.
Step 2 – Preservation – This is the most sensitive stage. It means securing access to the cloud data in a way that does not modify important elements like timestamps, metadata, and activity log. It is like sealing a crime scene before collecting fingerprints. If preservation fails, the credibility weakens.
Step 3 – Collection – Once the preservation is completed, data is collected in a controlled way. The data can include.
- Emails
- Attachments
- Images
- Login activity
- Audit logs.
Collection of data must be documented to maintain legal defensibility.
Step 4 – Examination and Analysis – This is the place where an investigator examines the data and analyses them to find evidence. Investigators reconstruct timelines, communication patterns, and studies unusual login locations analysed. This stage transforms raw data into meaningful evidence by analysing message flow, relationships, and link analysis.
Step 5 – Reporting – The final step is reporting. Findings of the case must be documented in a very clear and effective way. It must be understood by legal teams and courtroom authorities.
We now know What is Cloud Forensics and how it is performed. When we talk about it, MailXaminer is the best software that helps you to investigate the cloud data as per your preferences. This can make your tasks smoother and more effective with today’s growing complexity of cloud environments. It is the best email forensics software, which is especially designed to effectively collect, preserve, and analyse cloud digital evidence.
How a Professional Approach Helps in Cloud Forensics
Cloud evidence must be managed very responsibly. Professional forensic tools connects to platforms like Microsoft 365, Google Workspace, Teams, and IMAP using secure, authenticated APIs. It helps investigators:
- Bring data from multiple cloud accounts to one place.
- Original metadata, like timestamps and headers remain preserved.
- MD5 hash values are generated to protect integrity.
If your role is in cloud and email forensics, opting for a tool-based approach for analysis keeps the evidence original, structured, and legally defensible.
Final Thoughts
Cloud environments have been completely changed the way digital evidence is stored. These days, evidence does not sit on a single computer or a laptop. It is spread across cloud platforms. Understanding what cloud-based forensics extremely important. As this work is about a lot of precision. When it is handled correctly and sensitively, it can support informed legal decisions with clarity.
Frequently Asked Questions (FAQ)
Q – What is cloud forensics in simple words?
Ans – Cloud forensics is finding, collecting, and extracting evidence from data that is on cloud platforms like Google Workspace and Microsoft 365 in such a way that it has the capacity to be presented in a courtroom.
Q – Why do traditional forensics methods fail in cloud investigations?
Ans – As cloud data is not stored in one physical device. It is distributed and controlled via different service providers. Here, traditional methods tend to fail in cloud forensics.

