iCloud Forensics – Compromised Platform Examination
Before diving into iCloud forensics, we need to know about iCloud first. The iCloud is a free of cost cloud storage and computing service designed and rendered by Apple. The primary motto of introducing this service allows its users to store their data remotely and make it flexibly accessible (via browser access) despite the unavailability of the user’s device.
The storage supports all essential data of an Apple device, including Music, Pictures, Applications, Contacts, Videos and other assorted storage. Accessing the iCloud account enables users to not only use the data but also share it over to another user with an iOS 5 and above-configured Apple device.
The synchronization feature of the service makes it more special, for users who have their mobile devices connected to an iCloud account. They do not need to take data backups separately. The data on their iPhones/iPads are under regular syncing and securely kept in the cloud storage of their respective iCloud accounts. By setting up iTunes on the user’s machine, users can also generate Apple data backup and save the data locally rather than remotely.
Security and iCloud Forensics Vulnerability
The above discussion brings the focus of attention because of the extensive dependency of Apple users on iCloud. Apple gives guaranteed security of its user’s data stored on iCloud storage. However, coincidentally the cases of iCloud vulnerability to hacking late emerged.
Digital safety has become a major concern nowadays as compared to the bygone days. In the recent catastrophe, iCloud accounts of popular celebrities were hacked which lead to the obvious misuse of data stored in the accounts, i.e. leak of bare pictures.
Evidently, the privacy intrusion of the service led to situations that are against the safety measures guaranteed by Apple. The security breach on accounts got highlighted because it involves celebrities or VIP personalities. However, it clearly shows the reality of showcase security that Apple has implemented in securing its iCloud accounts.
Moreover, as far as the security measures are of current standards, cybercriminals can hack the storage easily. It is either by gaining physical access to the device or cracking the credentials of the iCloud account. Technically speaking, all the requirements to access an iCloud account are the user’s login credentials. Anyone can use the login details and get direct access to the account data. They don’t even have to testify that they are the authorized account holder.
Forensically Examining iCloud Storage
The breach of security shows the security level of iCloud data implemented by Apple. In order to access such sensitive and private data belonging to a user, simply enter the respective account holder’s login credentials. Moreover, the absence of multi-layered security is evident.
Vulnerability to such majorly destructive attacks is led to the requirement of applying forensic science while examining iCloud storage. In addition, it helps to find out how the hackers got access to users’ accounts and how to fix the loopholes to avoid such occurrences in the future.
In order to test the environment and perform an iCloud analysis at the same time, the investigation revealed two strategies that can be implemented to examine this data leak. Two ways to carry out iCloud forensics are:
- Manual Workarounds
There are some manual methods available for this task. Some of them work perfectly including local attacks and devices with Wi-Fi connections. Users can execute this by retrieving the pairing code that Apple devices use to connect with Wi-Fi. By doing this, there is a high chance of backing up its data by spoofing the machine via Wi-Fi connectivity. - iCloud Analysis Utilities
The programming of these applications is complex. It can get the user to pull out data kept on an iCloud account for investigation purposes. Law enforcement or other legal purposes are the only sectors where the use of these professional tools isn’t under any restriction.
Use Efficient Forensic Application for Apple iCloud Analysis
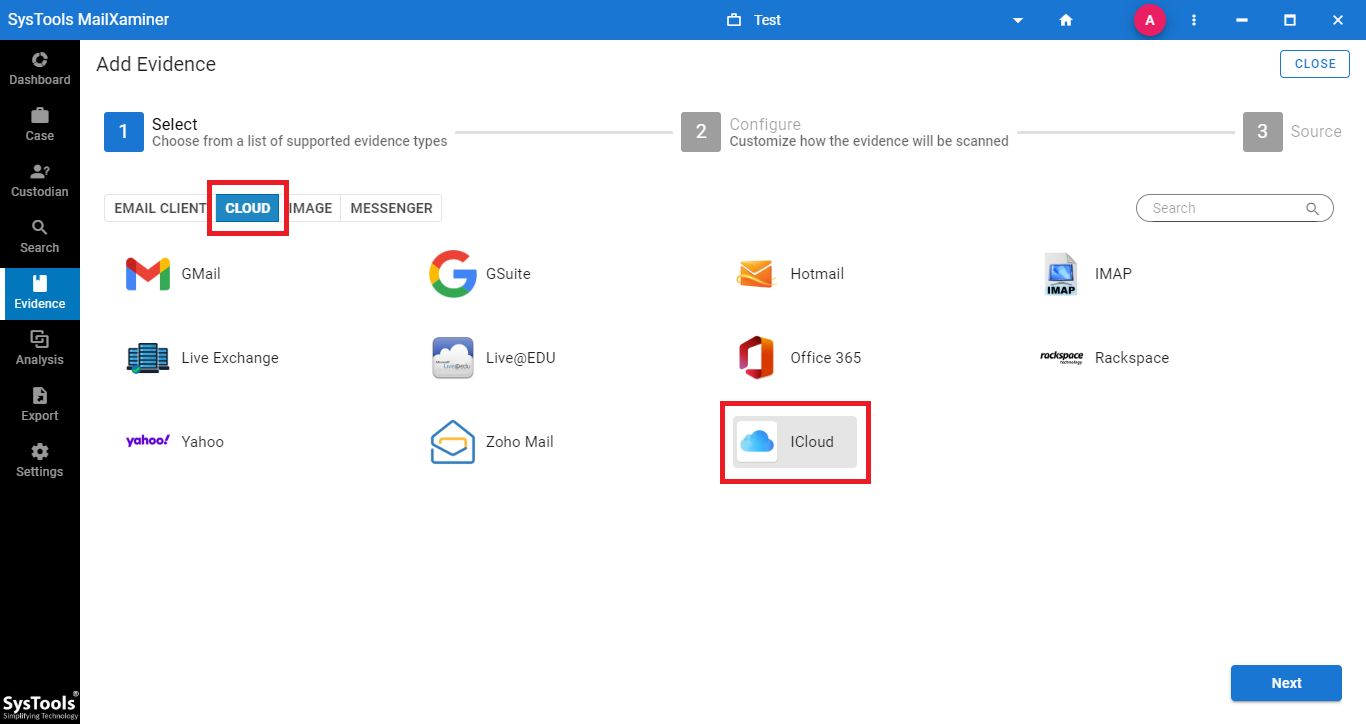
MailXaminer Email Examiner is a renowned tool that allows investigation of the hosted server and Cloud-based storage successfully. iCloud is supported as part of its web-based environment for investigation. Forensic examiners can conduct examinations of data stored on an iCloud account using the credentials investigators took in their custody.
Therefore, once the storage is in use and read by the application, the featured scanners can examine it. This is because of applying Advanced Searches, Filters, and Skin Tone Analysis on videos and image-based media. Apart from this, there is much more that users can do.
Moreover, users can implement this application’s advanced features to use for advanced forensic analysis of iCloud data to accomplish iCloud Forensics.
Conclusion
iCloud services are from Apple that users are utilizing widely because of the advanced features and top-level security. However, recently we get to know about a case of iCloud account hacking by cybercriminals. This shows that its multi-layered security is apparent. Hackers only need login credentials to access sensitive or personal data of users saved on iCloud accounts. In this write-up, we suggested two ways for Apple iCloud forensics analysis i.e. Manual Workaround and, iCloud Analysis Utilities.
The above mentioned software is one of the best Email Forensics Tool that is widely being used by forensic investigators to extract evidence from suspected data. It has a wide variety of inbuilt features which makes the analysis process convenient and less time-consuming.

